Isla Bailey
Cloud Security SpecialistIn a definitive move that signals a seismic shift in corporate strategy, financial giant Charles Schwab has dismantled the traditional walls separating its technological, operational, and data divisions, forging a new, unified command structure designed for an era dominated by artificial intelligence. The decision places Chief Information Officer
The security promised by multi-factor authentication has created a dangerous sense of complacency within many organizations, a weakness that a sophisticated threat group is now ruthlessly exploiting. A comprehensive intelligence analysis by Mandiant and the Google Threat Intelligence Group (GTIG) has brought to light a significant expansion of
The meteoric rise of artificial intelligence is often discussed in terms of algorithms and processing power, yet its very foundation rests on a physical, tangible network of data centers connected by vast webs of fiber optic cables. A landmark multiyear agreement between Corning Inc. and Meta Platforms has cast a brilliant spotlight on this
In the complex and high-stakes arena of cybersecurity, where the difference between protection and a catastrophic breach can hinge on a single decision, the unfiltered opinions of frontline practitioners offer the most resonant form of validation. While analyst reports provide crucial market analysis, it is the voice of the customer—the IT and
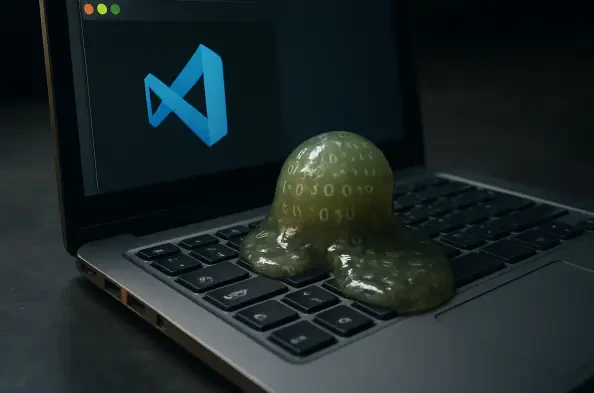
The allure of a powerful, free AI coding assistant became a trap for unsuspecting developers with the discovery of a malicious extension on the official Visual Studio Code Marketplace, an application designed not to enhance productivity but to stealthily hijack their systems. This incident highlights a sophisticated attack vector that preys on the
Within the sterile, highly regulated environment of modern medicine, a clandestine technological revolution is unfolding, driven not by institutional policy but by the individual initiative of clinicians and administrators seeking a competitive edge against their overwhelming workloads. This unsanctioned use of artificial intelligence, operating