The persistent vulnerability of perimeter hardware has long served as a quiet sanctuary for sophisticated cyber threat actors who exploit the inherent lack of visibility within these critical systems. While traditional endpoints like workstations and servers benefit from robust security stacks including endpoint detection and response tools, edge devices such as routers, firewalls, and load balancers remain largely opaque. These hardware components frequently lack the processing power or architectural compatibility to host modern security agents, leaving them susceptible to stealthy exploitation. Attackers recognize this gap and increasingly target edge infrastructure to establish initial persistence, using these devices to tunnel malicious traffic and coordinate secondary attacks without alerting internal monitoring systems. Because these devices sit at the very edge of the network, they often bypass the scrutiny of internal traffic analysis, allowing compromised hardware to function as a reliable gateway for external command and control operations that remain hidden for extended periods.
Strategic Shifts: Moving Beyond Inbound Telemetry
The Evolution of Perimeter Surveillance: From Scanning to Outbound Analysis
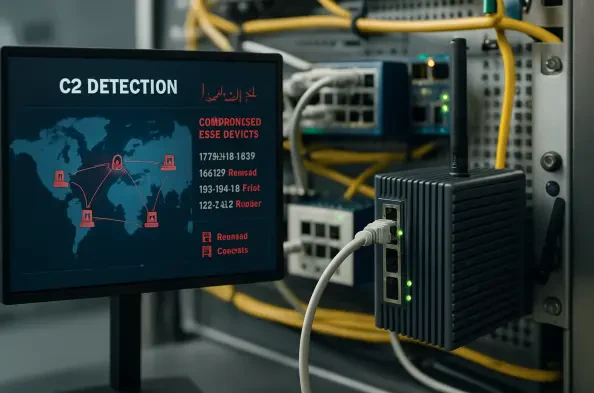
Security teams have historically focused on blocking inbound threats by monitoring external scanning activity and known malicious probes directed at their networks. However, the emergence of advanced command and control detection capabilities shifts this focus toward the more critical phase of the attack lifecycle: what happens after a device is potentially compromised. By analyzing outbound traffic patterns and identifying connections to verified infrastructure, defenders can identify breaches that have already bypassed the initial perimeter defense. This proactive methodology relies on a global sensor network that intercepts exploit payloads as they are broadcast across the public internet. Instead of merely recording the attempt, the system extracts embedded callback addresses that attackers use to communicate with their malware. This level of intelligence provides a high-fidelity view of the adversary’s infrastructure, allowing organizations to distinguish between harmless internet noise and a targeted, active breach involving their edge equipment.
Operationalizing Threat Intelligence: Actionable Stages for Incident Response
Identifying a suspicious connection is only the first step in a complex defense strategy; the real value lies in the ability to prioritize responses based on the severity of the threat. To address this, a structured framework categorizes threats into distinct stages that reflect the adversary’s progress within the kill chain. For instance, an unconfirmed status indicates that an address appeared in a payload but has not yet provided a downloadable malicious file, requiring watchful caution rather than immediate panic. In contrast, when a host is confirmed to be serving stage-one payloads, it serves as a definitive indicator that any internal device communicating with that host is already compromised. This tiered approach allows security operations centers to automate their workflows, focusing resources on confirmed infections while maintaining a secondary watch on emerging risks. By integrating this intelligence into existing security orchestration platforms, teams can perform historical audits to uncover past intrusions that may have eluded detection.
Enhanced Visibility: Securing the Untraceable Network Edge
Infrastructure Mapping: Identifying Malicious Assets Through Active Verification
The process of mapping attacker infrastructure requires more than just passive observation of network traffic; it demands an active verification process to ensure the accuracy of the data. Once a callback IP address is extracted from a malicious payload, the system proactively connects to these remote destinations to retrieve and analyze the specific malware being hosted. This ensures that every flagged IP address is backed by concrete evidence, such as verified file hashes and confirmed malicious behavior, rather than mere suspicion or outdated reputation scores. This level of detail is essential for defenders who must justify taking critical edge devices offline for remediation. By identifying the specific command and control servers that are actively participating in current campaigns, organizations can build a more resilient defense that anticipates the moves of threat actors. This active mapping process effectively turns the attacker’s own infrastructure against them, providing defenders with the blueprints needed to block future communication attempts.
Remediation Strategies: Future-Proofing the Perimeter Against Persistent Threats
Security professionals successfully utilized these automated detection capabilities to close the visibility gap that previously allowed edge device compromises to persist indefinitely. By shifting focus toward the verification of outbound callbacks and the analysis of malicious file hashes, organizations transformed their defensive posture from a reactive state to a proactive hunt for indicators of compromise. This approach proved highly effective in neutralizing stealthy persistence mechanisms that traditional logging had failed to capture. Moving forward, the integration of real-time payload analysis into standard network auditing will remain a fundamental component of a modern security architecture. It is recommended that security teams prioritize the continuous monitoring of egress logs against high-fidelity intelligence feeds to ensure that any deviation from normal behavior is immediately investigated. Maintaining this level of scrutiny over edge hardware ensures that the perimeter remains a barrier to entry rather than a hidden springboard for lateral movement within the corporate environment.