The speed at which a single compromised credential can transform into a full-scale corporate data exfiltration event has forced a radical reimagining of how digital perimeters are policed. For years, security operations centers operated under a fragmented model, where analysts spent more time toggling between disconnected browser tabs than actually neutralizing threats. This “swivel-chair” effect created dangerous latency, allowing sophisticated actors to linger in systems undetected. Today, AWS Security Hub is fundamentally changing this dynamic by evolving from a simple repository of findings into a centralized “mini-SOC” that orchestrates defense across the entire enterprise footprint.
By transitioning from a passive aggregator to a proactive command center, the platform now addresses the critical need for speed. It no longer just lists problems; it provides the context necessary to solve them. This shift marks a departure from the era of alert fatigue, where the sheer volume of notifications often obscured the most critical risks. Modern teams now utilize the service to gain a prioritized, actionable view of their security posture, ensuring that high-stakes vulnerabilities are met with immediate, automated responses rather than manual investigation.
The Shift: From Passive Visibility to Proactive Command
The traditional role of security monitoring has often been reactive, focusing on documenting incidents after they occur rather than preventing them in real time. AWS Security Hub has disrupted this cycle by integrating advanced orchestration capabilities that allow for automated remediation. By leveraging native cloud intelligence, the platform can now identify a misconfiguration and trigger a Lambda function to fix it before a human analyst even views the alert. This move toward self-healing infrastructure reduces the window of opportunity for attackers and allows security teams to focus on high-level strategy.
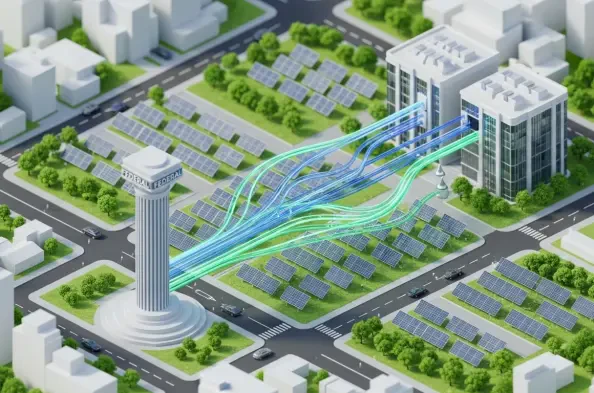
Moreover, the platform’s ability to consolidate diverse signals into a single pane of glass has eliminated the silos that previously hindered enterprise protection. When threat detection is no longer isolated from vulnerability management, organizations gain a holistic understanding of their risk. This centralized command structure ensures that security policies are applied consistently across thousands of accounts, making it nearly impossible for “shadow IT” or forgotten resources to remain unprotected.
Bridging the Gap: Cloud Infrastructure and Global Ecosystems
The modern enterprise does not live in a vacuum, yet security tools often act as if they do. For years, the industry has struggled with the “visibility gap”—the space between native cloud logs and third-party security signals from endpoints, email, and identity providers. This fragmentation is the primary reason why sophisticated threats remain undetected for long periods. The emergence of “Security Hub Extended” addresses this by recognizing that enterprise protection must be vendor-agnostic and data-fluid, reflecting a real-world trend where cloud security and traditional cybersecurity function as a single unit.
This bridge allows organizations to treat their entire infrastructure as a unified entity, regardless of where the data resides. By pulling in signals from external environments, the platform provides a comprehensive narrative of an attack’s lifecycle. Whether a threat begins with a phishing email or a suspicious login attempt on a mobile device, the Hub correlates these disparate events. This end-to-end visibility ensures that the security team is never blindsided by activity occurring outside the immediate cloud environment.
Unpacking the Evolution: The Path to Security Hub Extended
The transformation of the platform is defined by a strategic trajectory that moved from basic visibility to intelligent correlation. Initially launched for simple alert aggregation, the service underwent a massive reimagining in late 2025 to unify AWS-native powerhouses like GuardDuty and Inspector. This internal integration allowed for a prioritized view where vulnerabilities were finally mapped against active threat data. The introduction of the “Extended” tier completes this evolution by incorporating curated third-party solutions into the same ecosystem, effectively managing security across domains as diverse as endpoint protection and identity management.
This three-stage progression reflects the maturing needs of global organizations that require more than just a list of bugs. By mapping active threats against known vulnerabilities, the platform provides a “risk-based” perspective that was previously difficult to achieve. This means that a vulnerability on a public-facing server is automatically flagged with higher urgency than the same bug on an isolated test machine. Such intelligence is the cornerstone of the new extended tier, which brings the same level of scrutiny to third-party integrations.
Standardizing the Language: Cyber Defense via OCSF
The technical backbone of this new era of protection is the Open Cybersecurity Schema Framework (OCSF). By mandating that partner vendors—including industry leaders like CrowdStrike, Okta, Splunk, and Zscaler—deliver data in this normalized format, AWS has solved the historical problem of data incompatibility. This standardization allows for instantaneous, automatic cross-domain correlation. This move toward data normalization is what finally enables the detection of granular, multi-stage threats that previously vanished in the noise of disparate logs and custom integrations.
When every tool speaks the same language, the need for complex, custom-built middleware disappears. Security engineers no longer have to write scripts to translate a “severity 4” alert from one vendor into a “high” alert for another. Instead, the OCSF ensures that every piece of data is categorized and weighted identically. This uniformity is what allows the platform’s correlation engines to work at scale, identifying patterns that would be invisible to a human eye or a non-standardized system.
Streamlining Operations: Unified Procurement and Correlation
Enterprises can now apply a specific framework to reduce both technical and administrative overhead. By positioning AWS as the “seller of record,” organizations can consolidate their entire security spend—including third-party licenses—into a single invoice, removing the friction of managing dozens of individual contracts. Beyond the financial benefits, the platform provides a practical strategy for “full-stack” posture management: teams can utilize the curated ecosystem of 14 elite partners to ensure that every layer of the tech stack is automatically correlated within the Hub without manual coding.
The operational efficiency gained through this model extends far beyond the billing department. By reducing the number of APIs that need to be maintained and the number of vendor relationships that require active management, IT departments reclaimed hundreds of hours previously lost to administrative tasks. This streamlined approach ensured that the focus remained on defending the perimeter, while the underlying platform handled the complexities of integration. Organizations moved toward a future where security was a built-in feature of the business, rather than a costly and fragmented add-on.