The rapid evolution of quantum computing has fundamentally shifted the cybersecurity landscape, moving the primary concern from classical brute-force attacks to the sophisticated realm of quantum-level decryption. While significant industry resources have been poured into hardening massive data centers and central cloud hubs, a glaring vulnerability remains at the network edge where billions of industrial sensors, autonomous controllers, and remote field devices operate. These endpoints often lack the computational resources to run modern cryptographic suites, yet they handle the critical operational data that keeps global infrastructure functioning. As quantum processors approach the threshold of breaking current encryption, these peripheral devices represent the weakest link in the digital chain. Bridging this gap requires a departure from traditional software-based security, favoring hardware-driven solutions that can provide a permanent shield against both contemporary and future cryptographic threats.
Anticipating the Quantum Threat and Regulatory Shifts
The Looming Deadline for Modern Encryption
The concept of a “quantum apocalypse” is no longer a theoretical abstraction confined to physics laboratories but a looming operational reality for high-stakes industries. Experts generally agree that by the mid-2030s, quantum systems will likely possess the required qubit count and error correction capabilities to render current standards like RSA-2048 and Elliptic Curve Cryptography (ECC) obsolete. This timeline is particularly alarming because of the “Harvest Now, Decrypt Later” strategy employed by various adversarial actors. In this scenario, encrypted data is intercepted and stored today with the specific intent of unlocking it once quantum technology matures. This means that data with a long shelf life, such as national security secrets or long-term financial records, is already effectively compromised if it is transmitted using legacy encryption methods that cannot withstand a quantum-assisted brute-force attack.
Protecting the longevity of data requires an immediate transition to Post-Quantum Cryptography (PQC) rather than waiting for the arrival of a viable quantum threat. The shift in perspective focuses on the realization that encryption is not just about securing a current session but about ensuring that the information remains unreadable for its entire useful lifespan. Organizations are beginning to understand that if their data must remain confidential for twenty years, the transition to quantum-safe protocols must happen now. This has led to a surge in demand for hardware that can implement lattice-based algorithms, which are mathematically designed to be resistant to the Shor’s algorithm used by quantum computers. By integrating these defenses at the point of data origin, companies can negate the risk of retrospective decryption, ensuring that even if a packet is intercepted today, it remains a useless string of characters for decades to come.
Government Mandates and Compliance Timelines
Regulatory bodies have recognized the severity of this shift, leading to a series of aggressive mandates designed to force the hand of both public and private sectors. The U.S. government, through the National Security Agency’s Commercial National Security Algorithm Suite 2.0, has established a clear roadmap requiring that all national security systems transition to quantum-safe standards by 2035. This directive is not merely a suggestion; it includes specific milestones for software and hardware vendors to ensure that every layer of the infrastructure is hardened. For organizations operating within the defense industrial base or critical infrastructure sectors, these mandates create a high-pressure environment where compliance is a prerequisite for continued operation. The focus is specifically on moving toward NIST-standardized algorithms like ML-KEM and ML-DSA, which have undergone rigorous public scrutiny to ensure their resilience.
The challenge for many enterprises lies in the technical debt associated with legacy systems that were never designed for the high overhead of quantum-resistant math. Replacing every sensor or controller in a multi-billion-dollar utility grid is economically unfeasible, which has opened the door for “plug-and-play” security gateways. These devices, such as the Isidore Quantum, serve as a protective layer that sits in front of older equipment, effectively “wrapping” legacy traffic in a quantum-safe envelope. By adopting this architectural approach, organizations can meet federal compliance deadlines without the catastrophic costs of a full hardware refresh. This strategy allows for a phased transition where the most sensitive or exposed parts of the network are secured first, creating a manageable path toward total quantum resilience across the entire organizational footprint while adhering to the strict timelines set by global security agencies.
Technical Architecture of the Isidore Quantum Device
The Switch Isidore Three-Processor Design
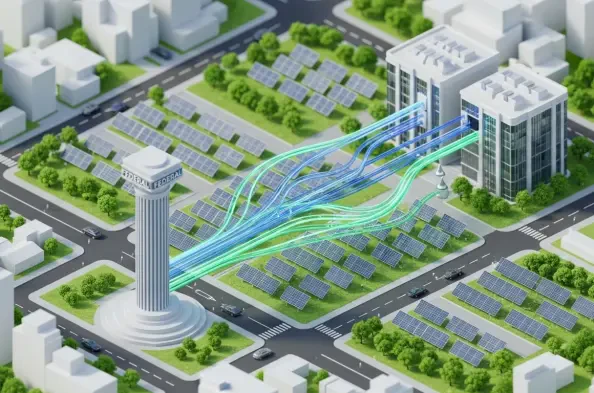
At the heart of the Isidore Quantum’s efficacy is its unique “Switch Isidore” architecture, which utilizes a dedicated three-processor system to create an impenetrable barrier. Most traditional security appliances rely on a single central processing unit to handle both network management and encryption, which creates a single point of failure and potential for software-based exploits. In contrast, the Isidore design separates these functions into discrete physical components. Two of these processors act as specialized Encryption Units (EUs), which are responsible for the heavy lifting of the NIST-standardized lattice-based cryptography. These units operate in a unidirectional manner, functioning as a data diode that allows information to exit a secure zone while preventing any incoming traffic from reaching the sensitive internal controller. This physical separation ensures that even if the external interface is compromised, the core system remains isolated.
The third processor in this triad functions as the Network Interface Device (NID), serving as the external-facing gateway that communicates with the broader internet or corporate network. There is a fundamental “trust boundary” maintained between the NID and the internal encryption units, governed by both physical circuitry and logical isolation. This design prevents common attack vectors such as man-in-the-middle interceptions and side-channel attacks, as there is no direct software path for an adversary to traverse from the outside world into the internal logic of the device. By enforcing this strict architectural hygiene, the system moves beyond the vulnerabilities of traditional firewalls, which are often susceptible to configuration errors or zero-day exploits. The result is a hardware-enforced security posture that provides deterministic protection, ensuring that the integrity of the data flow is maintained regardless of the complexity of the external threat landscape.
AI-Driven Defense and Performance Optimization
To augment its physical security layers, the device incorporates an autonomous “immune system” that utilizes machine learning models to identify and mitigate threats in real time. This AI layer is trained on massive datasets comprising trillions of known attack vectors, allowing it to recognize subtle anomalies in packet behavior that might indicate a sophisticated cyberattack. If the device detects suspicious activity, it can automatically execute defensive protocols, such as rerouting traffic or altering communication parameters, without requiring human intervention. This capability is vital for edge deployments where security personnel are often unavailable and the response time must be measured in milliseconds. By combining the rigid certainty of hardware data diodes with the fluid adaptability of artificial intelligence, the system creates a multi-layered defense that evolves alongside the tactics of modern cyber adversaries.
Performance is often the casualty of high security, but the Isidore Quantum is engineered to maintain high throughput and low latency within a constrained power envelope. Operating at less than 8 watts, the device is optimized for “Size, Weight, and Power” (SWaP), making it small enough to be integrated into satellite payloads, autonomous drones, or remote weather stations. Despite its diminutive form factor, it supports data rates of up to 2 Gbps with latency under 0.5 milliseconds, which is essential for time-sensitive applications like industrial control loops or real-time telemetry. This optimization ensures that adding a layer of quantum-safe security does not create a bottleneck in the system. The ability to provide enterprise-grade encryption and AI-driven monitoring in a palm-sized device marks a significant milestone in edge security, allowing for the protection of mobile and remote assets that were previously considered too resource-constrained for robust cryptographic hardening.
Global Deployment and the Strategic Ecosystem
Field Validation Across Defense and Research
The transition from laboratory prototype to field-ready hardware has been facilitated by an extensive series of pilot programs across various branches of the U.S. military. The Navy and Coast Guard have utilized the technology to secure the communication links of autonomous vessels, proving that the hardware can withstand the harsh environmental conditions of maritime operations while maintaining a secure link to command centers. Similarly, the Space Force and Air Force have integrated these units into satellite ground stations and aircraft telemetry systems, where the need for lightweight, low-power, and high-security hardware is paramount. These deployments serve as a rigorous validation of the device’s reliability, demonstrating that it can perform consistently in mission-critical scenarios where the failure of a security component could have catastrophic physical or strategic consequences for the national defense infrastructure.
Beyond domestic military applications, the technology has found a foothold in international academic and research environments, which are frequent targets for intellectual property theft. National Central University in Taiwan has successfully deployed the system to protect sensitive data shared between its research laboratories and external collaborators. This use case is particularly relevant given the rise of state-sponsored “Harvest Now, Decrypt Later” campaigns aimed at stealing advanced technological blueprints and scientific breakthroughs. By providing a quantum-safe conduit for this information, the device ensures that research institutions can collaborate globally without the fear that their future discoveries will be compromised by quantum-capable adversaries. The successful implementation in such diverse environments—from the high seas to university labs—underscores the versatility of the hardware and its ability to adapt to a wide variety of operational requirements and threat models.
Collaborative Security and Managed Services
A critical component of the broader rollout is the establishment of a strategic ecosystem that includes major technology providers and managed service partners. Forward Edge-AI has collaborated with Microsoft to leverage vast amounts of AI training data, ensuring the device’s anomaly detection algorithms remain ahead of emerging threats. Furthermore, the integration with Lumen Technologies allows for the delivery of “Security as a Service,” where enterprises can deploy these hardware units and have them monitored 24/7 by professional security operations centers. This partnership model is essential for the rapid scaling of quantum-safe technology, as it allows smaller organizations to benefit from high-end security without having to hire an in-house team of quantum experts. The managed service approach simplifies the complexity of the transition, providing a clear path for businesses to harden their edge infrastructure through a subscription-based model.
To address the global shortage of cybersecurity professionals who understand post-quantum protocols, the company has also pioneered specialized certification programs. These initiatives, developed in conjunction with international partners from Japan and South Korea, are designed to train a new generation of technicians in the deployment and maintenance of one-way quantum networks. This focus on human capital is just as important as the hardware itself, as even the most advanced encryption system can be undermined by improper installation or management. By building a certified workforce and a network of reliable industrial partners, the ecosystem ensures that the move to quantum-resistant infrastructure is supported by both robust technology and expert oversight. This holistic approach builds long-term confidence in the system, fostering a collaborative environment where security is treated as a shared responsibility across the entire supply chain.
Market Positioning and Industry Trends
Competitive Advantages in Post-Quantum Readiness
In the current market for cybersecurity hardware, the distinction between standard data diodes and quantum-ready gateways has become a primary differentiator for procurement officers. While established players have long offered unidirectional gateways to protect industrial control systems, most of these products were designed before the standardization of post-quantum algorithms. The Isidore Quantum distinguishes itself by being one of the first edge-optimized devices to achieve FIPS 140-3 compliance, the most modern federal benchmark for cryptographic modules. This certification provides a level of assurance that is mandatory for many government and regulated industry contracts. By focusing on the specific mathematical requirements of lattice-based cryptography from the outset, the device avoids the performance “tax” often associated with retrofitting older hardware to support new, computationally intensive encryption standards.
The competitive landscape is also shifting toward a preference for hardware that addresses the dual threats of intrusion and data harvesting. Traditional firewalls and software-based diodes are increasingly seen as insufficient for high-value targets because they remain vulnerable to sophisticated exploitation of the underlying operating system. The Isidore Quantum’s use of a hardware-enforced trust boundary and dedicated encryption processors offers a “zero-trust” architecture at the physical level, which is a significant selling point for sectors like finance and energy. As organizations move away from a “perimeter-only” defense strategy, the demand for decentralized security nodes that can operate independently of a central server has grown. The ability to provide this level of protection in a palm-sized, low-power unit positions the device as a leader in the emerging category of post-quantum edge security, where portability and performance are just as important as cryptographic strength.
The Future of Edge-Centric Cybersecurity
The rise of specialized hardware like the Isidore Quantum signals a fundamental change in how the industry conceptualizes the network perimeter. In the past, security was something that happened at the data center door, but the modern reality of the Internet of Things and autonomous systems has pushed that door to the very edges of the physical world. The industry is moving toward a model where every sensor and actuator is its own secure enclave, capable of protecting its own data and making autonomous decisions about the legitimacy of incoming traffic. This decentralization is necessary to manage the sheer volume of data being generated at the edge and to ensure that a breach in one remote node does not compromise the entire network. The transition to hardware-based, AI-driven, and unidirectional security is the natural evolution of this trend, providing a resilient foundation for the next generation of global digital infrastructure.
As the industry prepares for the inevitable arrival of powerful quantum processors, the focus will continue to shift toward “self-healing” and “immune-responsive” networks. These systems will not just wait for an administrator to patch a vulnerability but will actively monitor their own state and adapt to threats in real time. The integration of high-speed PQC into these edge nodes ensures that the fundamental privacy of data is maintained even against the most advanced future threats. This proactive posture is becoming the global standard for any organization that values the long-term integrity of its operational technology. By adopting these technologies today, the cybersecurity community is not just reacting to a future deadline but is actively building a more robust and trustworthy digital world that is prepared for the challenges of the quantum era and beyond.
Building a Resilient Digital Foundation
The development and deployment of the Isidore Quantum have provided a concrete framework for addressing the critical vulnerabilities of the network edge in a post-quantum world. Organizations should now prioritize the identification of their most sensitive edge assets and begin the process of wrapping legacy systems in quantum-safe hardware shells to mitigate the risk of data harvesting. The transition to NIST-standardized algorithms is no longer a choice but a requirement for maintaining operational viability and regulatory compliance. Waiting for the full arrival of quantum computing is a strategic error that leaves current data exposed to future decryption; therefore, immediate implementation of hardware-based data diodes is the most effective way to ensure long-term data integrity and system security.
Moving forward, the focus must expand beyond simple encryption to include the widespread adoption of AI-driven, autonomous defense mechanisms that can function without constant human oversight. Enterprises are encouraged to leverage managed security services and strategic partnerships to navigate the complexities of this transition, ensuring that their security posture remains agile and informed by the latest threat intelligence. By investing in the training of a specialized workforce and adhering to modern cryptographic standards like FIPS 140-3, the global community can build a decentralized infrastructure that is inherently resistant to both classical and quantum-era attacks. This proactive approach turned the theoretical threat of a quantum apocalypse into a manageable transition toward a more secure and resilient global digital architecture.