Vernon Yai is a preeminent authority on data protection and cybersecurity governance, known for his pragmatic approach to risk management in an increasingly volatile digital landscape. With a career spanning decades of advising both federal agencies and Fortune 500 companies, he has become a leading voice on how to balance national security imperatives with the need for private-sector innovation. In this discussion, we explore the evolving American cyber strategy, from the aggressive “America First” stance on offensive operations to the complexities of integrating agentic AI and post-quantum cryptography into aging infrastructure.
The current national strategy emphasizes “imposing costs” on adversaries through offensive operations to deter attacks. How can military cyber units effectively scale these operations, and what specific metrics determine if these maneuvers actually discourage nation-state hackers? Please provide a step-by-step breakdown of how offensive actions protect private networks.
Scaling offensive operations requires a shift from reactive defense to proactive disruption, moving beyond the traditional seven-page strategy outlines into real-world “unleashing” of capabilities. We measure success not just by the number of blocked intrusions, but by the tangible erosion of an attacker’s capacity; for instance, if we can dismantle the financial exit ramps for criminal groups, their motivation evaporates. To protect private networks, our cyber warriors first identify adversary infrastructure, then penetrate those foreign systems to neutralize threats before they reach domestic soil, and finally impose a “steep and terrible price” through retaliatory strikes. This creates a psychological and operational barrier that forces nation-states to recalculate the cost-benefit ratio of targeting American critical infrastructure.
Efforts are underway to streamline cyber regulations and reduce compliance burdens for the private sector. What are the practical trade-offs of delaying incident-reporting rules, and how can companies maintain high security standards without a federal checklist? Please explain the potential impact on industry transparency using specific examples.
The primary trade-off in delaying incident-reporting rules is a temporary dip in real-time visibility across the ecosystem, but the benefit is allowing security teams to focus on recovery rather than filling out forms during a crisis. By removing the “costly checklist” that often delays preparedness, we empower companies to innovate quickly and adopt emerging technologies tailored to their specific risks. Without a rigid federal mandate, high standards are maintained through market incentives and a focus on “continuity of the American economy,” where businesses prioritize resilience to protect their own intellectual property and brand reputation. However, this shift requires a high degree of trust, as the lack of a standardized reporting rule could lead to gaps in public knowledge about the true scale of transnational cybercrime.
There is an increasing expectation for state and local authorities to harden their own infrastructure, such as power grids and water systems. How can local leaders bridge the funding gap during federal downsizing, and what specific collaborative steps must occur to ensure national security isn’t weakened by regional constraints?
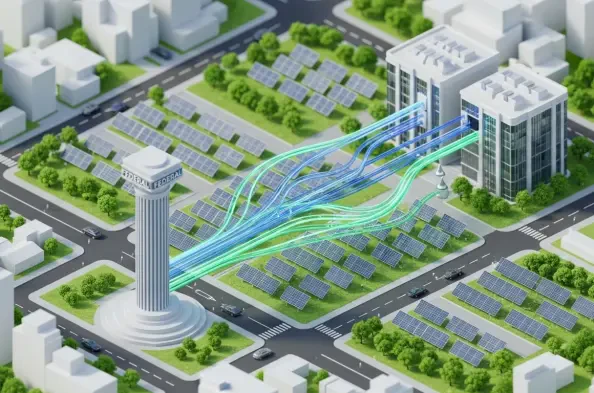
Local leaders are understandably concerned about the financial burden of defending infrastructure, especially as agencies like CISA see a reduction in size. To bridge this gap, the federal government must act as a “complement to—not a substitute for” regional efforts, providing specialized technical expertise even when direct funding is lean. Collaborative steps must include the sharing of state-of-the-art AI tools and decentralized threat intelligence that allow local water or power utilities to detect anomalies without needing a massive internal security staff. By galvanizing tribal and territorial authorities into a unified front, we ensure that a single weak link in a regional power grid doesn’t become a backdoor for a national-scale catastrophe.
The government is moving to rapidly adopt agentic AI and AI-enabled tools to detect and divert threat actors. How will these automated systems be integrated into existing defense frameworks, and what challenges arise when trying to establish international technology standards that prioritize national values over global consensus?
Agentic AI will be integrated as an autonomous layer within our Security Operations Centers, capable of making split-second decisions to “detect, divert, and deceive” threat actors without human intervention. This transition is critical because humans can no longer match the speed of machine-led attacks, especially those originating from peer competitors who are also investing heavily in AI. The challenge with international standards is that we are moving away from a global consensus that focuses on “harms” like bias, preferring instead to set standards that reflect American values of innovation and operational dominance. This creates a diplomatic friction point where the U.S. must lead through commerce and technical superiority rather than purely through traditional multilateral agreements.
Federal agencies are tasked with transitioning to zero-trust architecture and adopting post-quantum cryptography to secure their systems. What are the primary technical hurdles when modernizing legacy government networks for quantum readiness, and how does the implementation of AI-powered solutions change the daily workflow for security personnel?
The most daunting technical hurdle is the sheer volume of legacy federal information systems that were never designed for the complexity of post-quantum encryption algorithms. Transitioning these systems requires a massive overhaul of the underlying supply chains and a move toward cloud platforms that can support zero-trust architecture natively. For the workforce, AI-powered solutions change the daily grind by automating the “low-level” noise—the thousands of false positives—allowing personnel to focus on high-level strategic defense and workforce alignment. It shifts the human role from being a “sentry” at the gate to being a “commander” of an automated defensive fleet that operates at a scale previously unimaginable.
What is your forecast for American cybersecurity?
My forecast for American cybersecurity is a period of intense, tech-driven friction where the boundaries between private enterprise and national defense become almost entirely blurred. We will see the U.S. successfully “uproot criminal infrastructure” and make the country a harder target, but this will be a high-stakes race to maintain our lead in AI and quantum-ready systems before adversaries can adapt. Within the next few years, the success of this “America First” cyber posture will depend entirely on our ability to build a highly skilled workforce that can manage these autonomous systems while navigating a world where international norms are secondary to technological dominance. We are entering an era where the best defense is not a wall, but an active, intelligent, and highly disruptive presence in every corner of the digital world.