Data Security
The massive $61 billion acquisition of VMware by Broadcom has fundamentally reshaped how modern enterprises view their virtualization infrastructure and long-term vendor partnerships. Initially, the industry landscape was defined by a sense of urgency and alarm, with many IT leaders fearing that their foundational software would suddenly become
The Dawn of a New Era in Enterprise Financial Management The sheer velocity of artificial intelligence deployment has forced a radical restructuring of how the modern enterprise views every single dollar allocated toward its technological infrastructure. Once a niche discipline focused solely on monitoring cloud consumption, FinOps (Financial
Vernon Yai is a preeminent figure in the landscape of data governance and hardware security, known for his deep technical expertise in protecting complex silicon architectures. With an illustrious career focused on risk management and the creation of advanced detection protocols, he provides critical oversight for companies navigating the
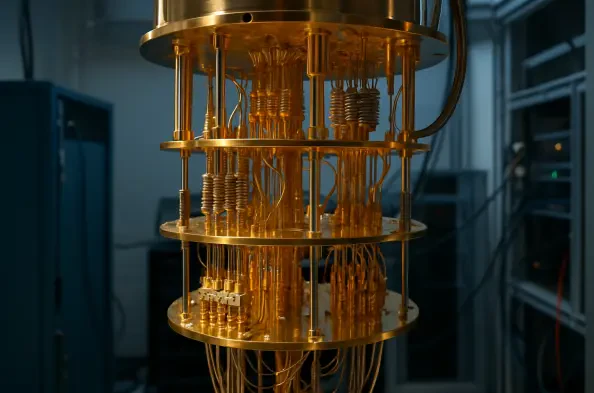
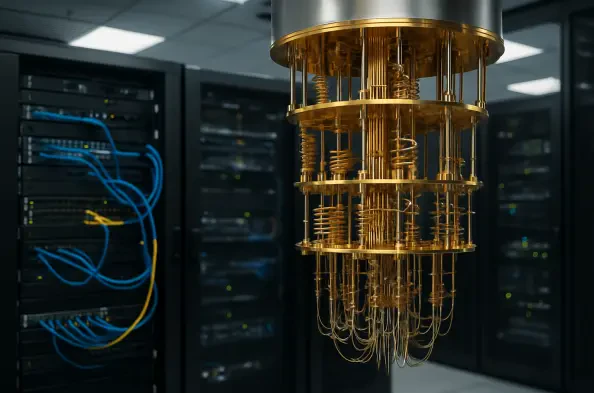
The theoretical vulnerability of elliptical curve cryptography to advanced computational threats has evolved from a distant concern into a measurable market variable that dictates current institutional strategies. As quantum hardware continues to advance, the concept of "Q-Day"—the moment when a quantum computer can successfully compromise
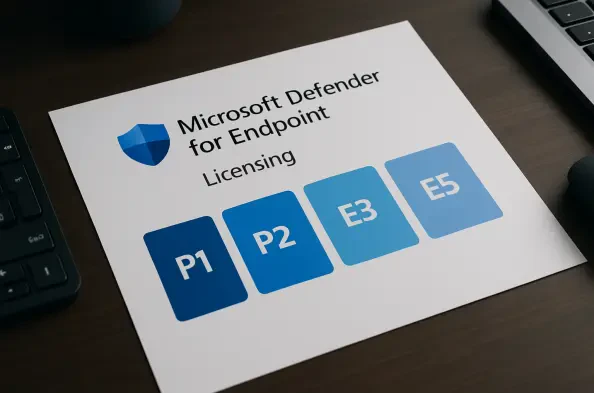
Modern cybersecurity professionals no longer view endpoint protection as a secondary defensive layer but rather as the primary battleground where the integrity of an entire corporate network is decided. Microsoft Defender for Endpoint represents a fundamental shift in how organizations approach this challenge, moving away from the antiquated model