Data Security
The escalation of automated cyberattacks has forced managed service providers to rethink the traditional patchwork of disconnected tools that once defined the standard for digital defense strategies. As the industry moves through 2026, the complexity of managing disparate endpoint detection, email security, and incident logging systems has become
The rapid acceleration of quantum hardware has long been cited as the ultimate Achilles' heel for decentralized financial networks, yet recent industry analysis suggests the threat is far more manageable than the doom-laden headlines often imply. This shift in perspective comes as analysts from firms like Bernstein categorize the quantum
The illusion of security within the modern software development lifecycle shattered recently as a sophisticated threat actor demonstrated that the very tools designed to protect us can become the ultimate Trojan horses. This operation, orchestrated by an entity known as TeamPCP, marks a pivotal shift in the cloud-native threat landscape, moving
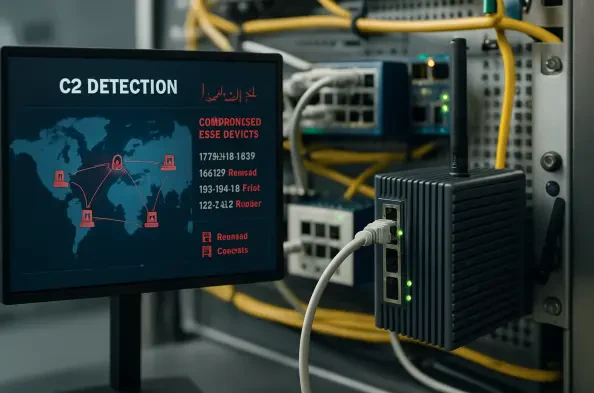
The persistent vulnerability of perimeter hardware has long served as a quiet sanctuary for sophisticated cyber threat actors who exploit the inherent lack of visibility within these critical systems. While traditional endpoints like workstations and servers benefit from robust security stacks including endpoint detection and response tools, edge
The Great Virtualization Migration: An Industry at a Crossroads The massive upheaval currently rattling the enterprise virtualization market is driven by a startling revelation that half of all existing customers are looking to move away from their primary vendor. Following the high-profile acquisition of VMware by Broadcom, an independent survey