Data Security
The rapid integration of artificial intelligence into daily corporate workflows has inadvertently opened a sophisticated new frontier for cybercriminals seeking to mask their activities within legitimate network traffic. This evolution marks a significant departure from previous years when generative models were primarily viewed as aids for
Modern enterprise defense rests on a paradox where the very software engineered to repel sophisticated digital incursions often serves as the most effective Trojan horse for high-level attackers. The recent discovery of critical vulnerabilities within Trend Micro’s Apex One, now rebranded under the TrendAI banner, underscores a precarious shift in
The sudden proliferation of autonomous artificial intelligence agents across corporate networks has fundamentally altered the baseline of digital operations, turning what were once static analytical tools into independent decision-makers. While initial iterations of AI focused on passive observation and defensive monitoring, the current generation
The relentless pursuit of digital agility has forced modern enterprises to confront a staggering reality where the sheer speed of AI-driven software development is frequently neutralized by the stagnant bureaucracy of legacy network security protocols. In the race to achieve complete digital transformation, many organizations are hitting a
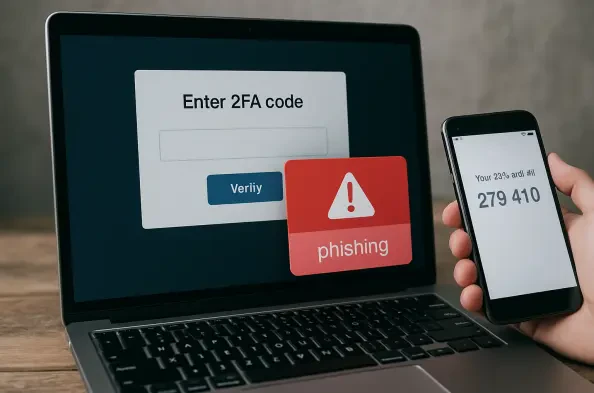
The illusion of absolute security provided by multi-factor authentication has been shattered by the realization that even the most robust digital locks can be picked if the burglar controls the hallway. As organizations increasingly leaned on secondary verification to defend their perimeters, a sophisticated adversary emerged to exploit the very