The rapid disappearance of the traditional network perimeter has forced a radical rethinking of how organizations protect their most sensitive digital assets. As enterprises migrate to complex multi-cloud environments, the old method of guarding the “front door” with a single firewall has become obsolete. Today, the real battlefield is identity, specifically the high-level permissions granted to administrators, developers, and automated systems. Privileged Access Management (PAM) has transitioned from being a niche compliance tool to the cornerstone of modern zero-trust architecture. This evolution reflects a shift in priority from simply locking away passwords to actively managing the risky behaviors associated with elevated rights.
The Evolution of Identity Security and Modern PAM
The foundational principles of PAM were once rooted in the concept of a “digital vault,” a secure repository where static administrative passwords were kept under lock and key. In this legacy model, an administrator would “check out” a credential, perform a task, and then return it, often leaving the password unchanged for months. However, the rise of ephemeral cloud infrastructure and microservices has rendered this slow, manual process a liability. Modern PAM has evolved into a dynamic, identity-centric discipline that focuses on verifying the user’s identity and context in real-time before any access is granted.
This shift is critical because today’s technological landscape is no longer confined to human users sitting at desks. It now encompasses a vast web of non-human identities, such as service accounts, containers, and automated deployment pipelines. By moving away from static vaulting toward a model where identity is the primary control plane, organizations can ensure that privileges are tied to the specific intent of a session rather than an indefinite set of permissions. This context-aware approach allows security teams to move at the speed of business without compromising the integrity of the underlying systems.
Architectural Innovations in Access Control
Just-in-Time: The Death of Standing Privileges
One of the most significant breakthroughs in recent years is the implementation of Just-in-Time (JIT) access and ephemeral credentials. Traditional systems often suffered from “standing privileges,” where an account held administrative rights 24/7, regardless of whether they were being used. This created a massive attack surface; if a credential was compromised at midnight, it was just as dangerous as it was at noon. JIT access solves this by granting permissions only for the duration of a specific task, effectively shrinking the window of vulnerability to near zero.
Furthermore, the use of ephemeral credentials—passwords or tokens that expire automatically after a few minutes—removes the need for credential rotation entirely. Because the secret literally ceases to exist once the task is finished, there is nothing for a lateral-moving attacker to steal. This architectural shift not only bolsters security but also simplifies the lives of IT teams who previously spent countless hours managing complex password rotation schedules across thousands of servers.
Protocol-Aware Zero-Trust Proxies
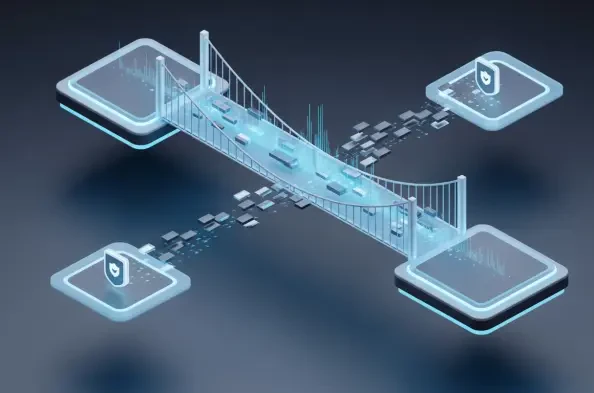
The technical backbone of modern PAM has moved from simple gateways to sophisticated protocol-aware proxies. Unlike traditional gateways that merely pass traffic through, these proxies understand the specific language of the database, cloud console, or terminal being accessed. This deep visibility allows the system to perform runtime authorization, meaning it can inspect the actual commands being typed and block a “delete database” request even if the user has the general right to access the server.
In high-velocity DevOps environments, this level of granularity is indispensable. Developers require seamless access to disparate tools without the friction of multiple logins or VPNs. Protocol-aware proxies provide a “frictionless” experience by intercepting connection requests and injecting the necessary credentials behind the scenes. This ensures that the security layer remains invisible to the end-user, reducing the likelihood that employees will attempt to bypass security protocols to maintain their productivity.
Current Trends and Strategic Market Shifts
The market is currently witnessing a massive consolidation as established vault-centric vendors acquire agile, cloud-native startups. This trend is driven by the realization that traditional PAM cannot keep up with the demands of modern engineering teams on its own. The industry is moving toward “unified identity platforms” that merge standard identity management with privileged access, creating a single pane of glass for all user types. This consolidation helps eliminate the silos between IT operations and security teams, fostering a more cohesive defense strategy.
Real-World Applications and Industry Implementation
In the realm of Kubernetes orchestration and cloud-scale infrastructure, modern PAM is no longer optional. When a developer needs to debug a container in a production cluster, providing them with permanent root access would be a catastrophic risk. Modern implementations allow for the temporary elevation of rights based on a specific ticket or request, ensuring that the developer can fix the issue without leaving a permanent back door open. This integration is vital for maintaining the “infrastructure-as-code” philosophy that defines modern software development.
Moreover, these systems are bridging the gap between traditional database management and modern workflows. By providing a unified access layer for SQL databases, NoSQL clusters, and legacy mainframes, organizations can enforce a single set of security policies across their entire data estate. This consistency is particularly important for global enterprises that must comply with varying regional data protection regulations while maintaining a centralized security posture.
Technical Challenges and Adoption Obstacles
Despite its benefits, the adoption of advanced PAM technology is not without its hurdles. The primary challenge remains the inherent friction between stringent security requirements and developer velocity. If a security tool adds even a few seconds of delay to a routine task, developers may find workarounds, inadvertently creating “shadow IT” risks. Balancing this tension requires a cultural shift within the organization, where security is viewed as an enabler rather than a roadblock.
Additionally, managing fragmented identities across multi-cloud environments remains a significant technical difficulty. As organizations use a mix of different cloud providers, the number of distinct identity providers and permission sets can become overwhelming. Achieving a “single source of truth” for identity requires complex integration work and a high level of technical maturity, which can be a barrier for smaller organizations with limited cybersecurity staff.
Future Outlook: AI Governance and Autonomous Identities
The next frontier for PAM is the governance of artificial intelligence agents. As autonomous agents begin to perform complex tasks like system optimization or automated threat response, they will require their own set of privileged credentials. The challenge will be managing the “intent” of these agents. Future developments will likely focus on intent-based access control, where the PAM system uses machine learning to predict whether an agent’s request aligns with its designated role or if it indicates a potential breach.
As the lines between human and machine identities continue to blur, the role of automated security governance will expand. We will likely see the rise of autonomous PAM systems that can self-adjust permissions based on real-time risk scores. This would mean that a user’s access level could fluctuate throughout the day based on their location, the health of their device, and the sensitivity of the data they are accessing, all without human intervention.
Comprehensive Assessment of PAM Technology
The transition toward frictionless, proxy-based security has proven to be an essential step for the modern enterprise. By moving away from the rigid structures of the past and embracing dynamic, just-in-time access, organizations successfully mitigated the risks associated with credential theft and lateral movement. The integration of privileged access into the broader identity ecosystem allowed for a more holistic view of risk, which became indispensable as infrastructure grew more decentralized and complex.
Ultimately, the maturation of PAM technology provided the necessary bridge between the high-speed requirements of development and the rigorous demands of security compliance. Organizations that adopted these advanced architectural patterns found themselves better positioned to handle the emergence of non-human identities and AI-driven workflows. This shift transformed privileged access from a reactive hurdle into a proactive strategic advantage in an increasingly hyper-connected digital landscape.