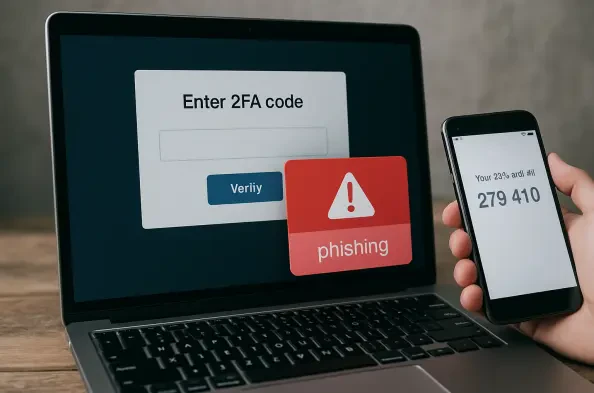
The illusion of absolute security provided by multi-factor authentication has been shattered by the realization that even the most robust digital locks can be picked if the burglar controls the hallway. As organizations increasingly leaned on secondary verification to defend their perimeters, a sophisticated adversary emerged to exploit the very communication layer between the user and the service. Tycoon 2FA is not merely a collection of malicious scripts; it is a refined industrial-grade engine designed to bypass modern defenses by standing directly in the flow of data. This technology has redefined the threat landscape by moving past simple credential theft and toward the complete hijacking of authenticated identities.
The emergence of Tycoon 2FA within the Phishing-as-a-Service (PhaaS) market marked a professionalization of cybercrime that few anticipated. While earlier kits required significant manual configuration and technical expertise, this toolkit offered a turnkey solution for attackers of varying skill levels. It appeared during a period of transition where traditional phishing was losing its efficacy due to the widespread adoption of one-time passwords and authenticator apps. Tycoon 2FA filled this gap by providing a reliable method to neutralize these defenses, quickly becoming a preferred choice for those looking to infiltrate enterprise environments with minimal resistance.
The Emergence of Tycoon 2FA in the PhaaS Market
The technology represents a paradigm shift in how digital fraud is executed and distributed. At its core, it functions as a comprehensive platform that provides the infrastructure, templates, and backend logic necessary to launch high-fidelity attacks. This development is significant because it democratizes high-level exploitation, allowing actors who lack deep cryptographic knowledge to bypass security measures that cost corporations millions to implement. The toolkit has evolved from a niche underground project into a dominant force in the cyber-criminal service industry by focusing on reliability and user experience for the attacker.
Its relevance in the broader technological landscape cannot be overstated, as it directly challenges the zero-trust architecture that many firms have adopted. By targeting the session layer rather than just the password, Tycoon 2FA has forced security professionals to reconsider the longevity and validity of digital tokens. The toolkit emerged in a context where “identity” is the new perimeter, and its ability to compromise that identity suggests that our current reliance on transient codes may be insufficient. It sits at the intersection of automation and social engineering, proving that technical sophistication is most dangerous when paired with an easy-to-use business model.
Technical Architecture and Service Capabilities
Adversary-in-the-Middle: The AitM Framework
The primary engine behind Tycoon 2FA is the Adversary-in-the-Middle (AitM) framework, a sophisticated proxy system that intercepts communication in real-time. Unlike older phishing methods that directed users to a static, fake page, this framework acts as a transparent relay between the victim and a legitimate service like Microsoft 365. When a user enters their credentials, the toolkit passes them to the real login portal instantly. When the real portal requests an MFA code, the toolkit prompts the user for it and relays it back to the service. This performance is seamless, often leaving the victim entirely unaware that their interaction was being monitored and manipulated.
The significance of this architecture lies in its ability to capture session cookies, which are the digital “passports” issued after a successful login. By securing these tokens, the toolkit allows the attacker to clone the user’s authenticated state on their own device. This effectively renders the password and the MFA code irrelevant for the duration of the session. The technical performance of Tycoon 2FA in this regard is highly efficient, minimizing latency to ensure the victim does not experience the “lag” that often characterizes less sophisticated proxy attacks. It turns the security handshake into a vulnerability by simply being the silent participant in the conversation.
Phishing-as-a-Service: The PhaaS Business Model
Beyond the technical code, the toolkit’s success is driven by its Phishing-as-a-Service (PhaaS) business model, which treats cyber-attacks like a legitimate software subscription. For a monthly fee, users gain access to a web-based administration panel that manages the entire lifecycle of a campaign. This includes automated deployment of phishing pages, real-time tracking of victims, and an organized database of harvested session tokens. This commercialization is unique because it removes the “maintenance” burden from the attacker; the developers of Tycoon 2FA handle the hosting, domain rotation, and code updates, allowing the subscriber to focus solely on distribution.
The real-world usage of this model has seen it used to target nearly 100,000 organizations globally. The technical aspects of the panel are designed for high-volume operations, featuring built-in templates that perfectly mimic trusted corporate brands and productivity suites. This implementation is far more effective than competitors’ because it integrates redirection logic that sends the victim to a legitimate site after the theft is complete, further obscuring the crime. This “service” approach has turned a complex technical hurdle into a manageable operational expense for criminal enterprises, leading to a massive increase in attack volume across the globe.
Innovations in Evasion and Persistence
One of the most impressive, albeit destructive, innovations in this toolkit is its dynamic infrastructure management. To stay ahead of security scanners, the platform utilizes rapid domain turnover and heavy JavaScript obfuscation. These updates are not static; the toolkit employs browser fingerprinting to detect if a visitor is a human victim or a security bot. If a bot is detected, the toolkit serves a harmless page, effectively “ghosting” the analysts and extending the lifespan of the malicious domain. This level of adaptability ensures that the infrastructure remains operational even under heavy scrutiny from global security firms.
Furthermore, the toolkit has popularized the concept of “ATO Jumping,” or Account Takeover Jumping. Once a single account is compromised via the AitM framework, the toolkit facilitates the distribution of further phishing links from that legitimate, internal email address. Because the emails originate from a trusted source within the organization, they bypass traditional spam filters and security gateways. This trend in persistence marks a shift toward more organic, lateral movement within a network, where the initial compromise is just a springboard for a much larger, more integrated infiltration of the corporate environment.
Real-World Deployment and Sector Impact
The deployment of Tycoon 2FA has been particularly devastating in the enterprise and public sectors. While individual users are targeted, the primary focus has been on high-value targets in healthcare, education, and government agencies. In these environments, the toolkit is used to gain access to centralized productivity hubs like SharePoint and OneDrive. Because these platforms house sensitive data and internal communications, a single hijacked session can lead to massive data exfiltration or the deployment of ransomware. The toolkit’s ability to maintain access without re-triggering MFA makes it an ideal tool for long-term corporate espionage.
Unique use cases have also emerged in the financial sector, where attackers use captured sessions to authorize fraudulent wire transfers or modify payroll details. Because the attacker is using a legitimate session token, the bank’s security systems often see the transaction as coming from a recognized, “trusted” device and browser. This sector-wide impact highlights a critical flaw in current defense strategies: we have focused so much on the “entry” that we have neglected the security of the “stay.” Tycoon 2FA exploited this gap with surgical precision, leading to billions of dollars in potential risks across several international markets.
Mitigation Hurdles and Strategic Countermeasures
Countering Tycoon 2FA presents several technical and regulatory hurdles. Traditional defensive measures, such as IP blocking or static blacklists, are largely ineffective against the platform’s rapid domain rotation and Cloudflare-backed infrastructure. Moreover, the move toward encrypted messaging apps for customer support and sales makes it difficult for law enforcement to track the developers. The primary challenge is that the toolkit exploits the fundamental design of how web authentication works; as long as session cookies are the primary method for maintaining login states, the AitM technique will remain a viable threat.
Ongoing development efforts to mitigate these limitations now focus on “session-aware” security. This includes shortening session lifetimes, implementing device-bound passkeys, and using behavioral analytics to detect when a session token is being used from an unexpected location or browser fingerprint. However, these countermeasures often come at the cost of user convenience, creating a friction-filled experience that many organizations are hesitant to adopt. The struggle is no longer just about stopping a login; it is about continuously verifying that the entity holding the session is the same entity that started it.
Future Projections for Identity-Centric Security
Looking forward, the legacy of Tycoon 2FA will likely catalyze a shift away from traditional MFA and toward more resilient, hardware-backed authentication. Breakthroughs in phishing-resistant standards, such as FIDO2 and WebAuthn, offer the most promising path forward. These technologies require a physical hardware key or a biometric verification that cannot be easily proxied by a middleman toolkit. As these standards become more accessible and easier to deploy, the effectiveness of AitM frameworks will eventually diminish, forcing attackers to find new vulnerabilities in the identity chain.
The long-term impact on society will be a redefinition of digital trust. We are moving toward an era where identity is not something you “know” or “receive,” but something you “possess” through hardware. While Tycoon 2FA has caused immense damage, it has also accelerated the obsolescence of insecure authentication methods. Future developments will likely involve AI-driven identity verification that monitors session behavior in real-time, effectively creating a “living” security perimeter that adapts to the user’s actions rather than just their initial credentials.
Final Assessment of the Tycoon 2FA Era
The era of Tycoon 2FA provided a stark reminder that cyber-criminals are often more agile than the defenses built to stop them. The platform successfully exploited a critical vulnerability in the human-to-digital interface, proving that even multi-factor authentication was not a panacea. By industrializing the Adversary-in-the-Middle technique, the developers created a tool that was both technically sophisticated and commercially accessible. This combination resulted in an unprecedented wave of account takeovers that affected nearly every major industry, highlighting the fragility of our current session-based security models.
The eventual disruption of its infrastructure by international law enforcement was a significant achievement, yet it served more as a tactical victory than a strategic one. The core methodologies pioneered by the toolkit—specifically its focus on session hijacking and its seamless PhaaS delivery—have already been adopted by a new generation of developers. Organizations were forced to recognize that identity-centric security requires more than just a password and a code; it requires a continuous, hardware-validated verification process. Ultimately, the toolkit’s greatest impact was in exposing the limitations of our digital trust, paving the way for more resilient, phishing-resistant technologies.