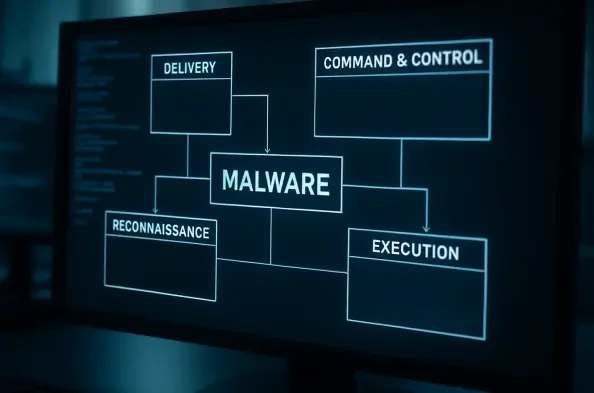
The silent infiltration of cloud-native infrastructure has entered a new phase of maturity where the distinction between professional security tools and malicious implants has effectively dissolved. Within this volatile landscape, the VoidLink malware framework has surfaced as a sophisticated, modular toolkit specifically engineered for high-performance operations in Linux environments. This framework is not merely a collection of scripts but a comprehensive ecosystem designed for long-term stealth and persistence, marking a departure from traditional, “noisy” attack methods. Its emergence reflects a calculated response to the increasing reliance of global enterprises on Linux-based cloud services, transforming what was once a secure sanctuary into a primary theater of cyber conflict.
Evolution and Core Principles of the VoidLink Architecture
The development of VoidLink is closely associated with the operations of UAT-9921, a threat actor that has maintained a persistent presence in the cyber landscape since at least 2019. While the group’s early efforts were focused on more conventional exploitation, the transition toward a highly modular and stealthy architecture indicates a maturation of their strategic goals. VoidLink represents the culmination of this evolution, prioritizing stability and surgical precision over broad-spectrum delivery. By focusing on the Linux ecosystem, the creators have exploited the inherent trust placed in backend cloud servers, which often lack the same level of endpoint monitoring found in Windows-heavy office environments.
This architecture is built on the principle of minimal footprint during the initial compromise, followed by the dynamic deployment of specialized capabilities. The shift toward Linux-centric exploitation is a logical progression given the industry’s migration to containerized workloads and microservices. VoidLink fits perfectly into this niche, providing a reliable bridge for attackers to maintain access without triggering the behavioral alarms that typically accompany more rigid malware strains. This design philosophy ensures that the framework can survive across various distributions and kernel versions, making it a versatile asset for a sustained campaign.
Technical Composition and Functional Architecture
Multilingual “Compile-on-Demand” Engine
The framework’s most distinctive feature is its “compile-on-demand” capability, powered by a sophisticated multilingual coding base. The core implant is written in Zig, a modern systems programming language that offers the performance of C with enhanced safety and memory management features. This choice is significant because Zig produces small, efficient binaries that are difficult to signature-match with older security tools. Plugins are typically developed in C for low-level system interaction, while the backend command-and-control infrastructure utilizes GoLang, leveraging its native support for concurrent networking.
This diverse language stack allows VoidLink to be tailored for specific Linux distributions on the fly, facilitating precise reconnaissance and data extraction based on the target environment’s unique constraints. Instead of delivering a generic payload that might fail on an obscure kernel version, the framework generates a bespoke implant. This adaptability ensures that the malware can navigate different library dependencies and system architectures, significantly reducing the likelihood of a crash or detection during the critical stages of lateral movement.
AI-Assisted Development and Kernel-Level Persistence
The sophistication of VoidLink’s internals suggests a heavy reliance on Large Language Models during its creation. This “spec-driven development” involves using AI to interpret complex technical requirements and generate the corresponding low-level code, particularly for hard-to-detect rootkits. By automating the production of kernel-level components, the developers can bypass the tedious manual debugging process usually required for such sensitive code. This approach allows for the creation of intricate persistence mechanisms that reside deep within the operating system, often operating beneath the visibility of standard security agents.
The use of AI-assisted coding represents a paradigm shift in how malware is constructed, lowering the barrier for producing professional-grade software that rivals the quality of commercial security products. These AI-generated modules are designed to hook system calls and manipulate kernel structures, effectively hiding files, processes, and network connections from the user. The result is a nearly invisible presence that can survive reboots and even most system updates, providing UAT-9921 with a permanent foothold within compromised cloud networks.
Tiered Management and Operational Oversight
Beyond its technical payload, VoidLink features a professional-grade Role-Based Access Control system, which is a rarity in the world of independent malware. This internal structure includes SuperAdmin, Operator, and Viewer tiers, mirroring the organizational logic of a legitimate software enterprise or a military intelligence unit. Such an arrangement allows for a clear division of labor: the SuperAdmin manages the infrastructure, the Operator executes the tactical mission, and the Viewer monitors the data flow for intelligence purposes.
The significance of this tiered management lies in its auditability and operational security. By restricting high-level permissions, the threat actor reduces the risk of accidental exposure or internal mishandling of sensitive target data. This level of organizational discipline suggests that VoidLink is intended for large-scale, coordinated campaigns where multiple individuals or teams must collaborate within a single unified framework. It points toward a highly structured operational environment that prioritizes long-term strategic gains over immediate, opportunistic theft.
Emerging Trends in AI-Augmented Cyber Weaponry
The rise of frameworks like VoidLink signals a broader trend toward “near-production-ready” modular kits that blur the line between cybercrime and professional red teaming. There is a visible shift toward automating the tool-preparation phase, where the manual labor of researching vulnerabilities and drafting exploits is replaced by automated systems. This trend is democratizing access to high-tier cyber weaponry, allowing actors with fewer resources to deploy tools that were previously the exclusive domain of state-sponsored entities.
Furthermore, these frameworks are increasingly adopting the modularity of modern software development, such as the use of standardized APIs for plugin integration. This allows for rapid iteration and the quick inclusion of new exploit modules as soon as a zero-day vulnerability is discovered. The move toward this agile development model means that security teams are no longer fighting static threats but rather a dynamic, evolving ecosystem that can adapt to defensive measures in near real-time.
Real-World Applications and Sector Targeting
VoidLink has seen extensive deployment within the technology and financial services sectors, where high-value data and complex network topologies provide an ideal environment for its capabilities. In documented implementations, the framework utilized tools like Fscan for internal network mapping and SOCKS proxies to facilitate stealthy lateral movement. By establishing a robust internal pivot point, attackers can scan for vulnerabilities across the internal network that are not visible from the public internet. This allows them to move from a relatively low-value entry point to the core databases or payment processing systems that hold the most sensitive information.
There is also evidence that the framework is preparing for an expansion into Windows environments via DLL side-loading capabilities. While its current focus remains Linux-centric, the modular design allows for the addition of Windows-specific plugins that could bridge the gap between cloud servers and corporate workstations. This cross-platform potential makes VoidLink a comprehensive threat capable of traversing an entire corporate ecosystem, from the cloud backend to the executive’s laptop, using a single, unified management interface.
Technical Hurdles and Defensive Challenges
The detection of VoidLink remains a significant challenge for modern cybersecurity teams due to its robust anti-forensics and evasion mechanisms. The framework is capable of identifying the presence of Endpoint Detection and Response solutions and dynamically adjusting its behavior to avoid triggering alerts. This includes techniques such as memory-only execution, where no malicious files are written to the disk, and the use of legitimate system processes to mask malicious activity. The lack of a clear historical footprint for such “production-ready” frameworks complicates the task of threat hunters who rely on known patterns or indicators of compromise.
Discrepancies in operational timelines also highlight the difficulty of tracking these sophisticated actors. While some intelligence suggested the development of the framework began late in the cycle, evidence of active victims surfaced much earlier than anticipated. This gap suggests that the framework was likely operational and tested in closed environments long before it was detected in the wild. Cybersecurity firms are currently struggling to keep pace with these kernel-level threats, as the traditional signature-based approach is almost entirely ineffective against bespoke, AI-generated code.
Future Trajectory of Modular Malware Frameworks
Looking forward, the integration of autonomous command-and-control agents appears to be the next frontier for frameworks like VoidLink. These agents could independently discover and exploit vulnerabilities within a target network without needing constant instruction from a human operator. Such autonomy would significantly increase the speed of an attack, allowing for the rapid exfiltration of data before a security team can even identify the breach. The development of more advanced cross-platform modularity will also likely continue, eventually creating a seamless pipeline for moving between diverse operating systems and cloud architectures.
The long-term impact on the security posture of global financial and technological infrastructure will be profound. As these modular systems become more prevalent, the cost of maintaining a secure network will rise, requiring a shift toward zero-trust architectures and more advanced behavioral analysis. The era of static defense is ending, and the industry must prepare for a future where malware is as sophisticated, flexible, and well-managed as the most advanced legitimate enterprise software.
Summary and Final Assessment of VoidLink
The review of the VoidLink framework confirmed its status as a highly sophisticated evolution of modular malware, specifically tailored for the complexities of modern Linux cloud environments. The analysis demonstrated how the integration of multilingual programming and AI-assisted development allowed UAT-9921 to create a toolkit that was both resilient and exceptionally difficult to detect. The operational structure, including its tiered access control and professional management interface, indicated a level of organizational maturity that far exceeded standard cybercriminal operations. This framework functioned effectively as a precursor to a new generation of AI-driven threats that prioritized surgical precision and long-term persistence over immediate disruption.
The findings highlighted the growing gap between the capabilities of modular malware and the defensive strategies currently employed by many organizations. The framework’s ability to dynamically generate bespoke implants and its potential for cross-platform expansion suggested that future security models must move beyond simple signature-based detection. The necessity for evolved detection strategies, such as deep kernel monitoring and advanced behavioral heuristics, became clear as the framework successfully evaded traditional EDR solutions. Ultimately, VoidLink served as a stark reminder that the future of cyber warfare would be defined by adaptability, automation, and a sophisticated mirroring of professional software engineering practices.