Privacy Protection
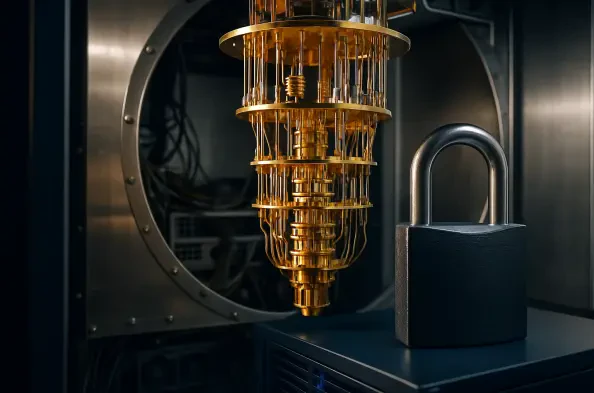
The trust individuals and businesses place in financial advisory firms is foundational, built on the assurance that sensitive personal and financial data will be handled with the utmost confidentiality and security. When this digital fortress is penetrated, the consequences extend far beyond the compromised company, sending ripples of concern
In a significant move to reclaim individual privacy in the digital age, California has officially launched a revolutionary tool designed to give residents sweeping control over the vast and often unseen marketplace of their personal information. The state’s new "Delete Requests and Opt-Out Platform," or DROP, acts as a centralized hub, providing a
With your smartphone now serving as the definitive hub for your entire digital existence, managing everything from intricate financial transactions and private communications to official identity verification, it has become an unprecedentedly valuable target for cybercriminals. The threat landscape has matured far beyond simple viruses, now
In a decisive move to restore the balance of power in the digital data economy, California has officially activated a groundbreaking tool that gives its residents unprecedented control over their personal information. The Delete Request and Opt-out Platform, known as DROP, went live on January 1, 2026, creating a centralized, state-managed service
In the sprawling digital economy where personal data has become a premier commodity, Californians now have access to a powerful new tool designed to reclaim their privacy from the hundreds of data brokers operating quietly in the background. As of January 1, the state has officially launched the Delete Request and Opt-out Platform (DROP), a