Privacy Protection
The looming arrival of quantum computing, a technological milestone often referred to as “Q-Day,” presents an unprecedented threat to global digital security, with projections suggesting that by 2033, these powerful machines could shatter the encryption standards that protect everything from financial transactions to government secrets. This has
The financial aftershock of a significant cyber incident now extends far beyond the initial breach, with the average cost soaring past $4.5 million and penalties for delayed reporting amplifying the damage by nearly a third. This unforgiving economic reality, coupled with an increasingly hostile digital environment, is forcing a radical
The very tool designed to shield the world's most sensitive conversations from prying eyes has been cleverly turned into a conduit for espionage, according to a stark warning from German intelligence agencies. The encrypted messaging application Signal, long championed as a bastion of digital privacy by journalists, activists, and government
In a significant move that aligns its regulatory framework with stringent global standards, Hong Kong's privacy regulator is set to reintroduce amendments that will mandate data breach reporting and establish a system of administrative fines. This revival of long-discussed changes to the Personal Data (Privacy) Ordinance (PDPO) signals a new era
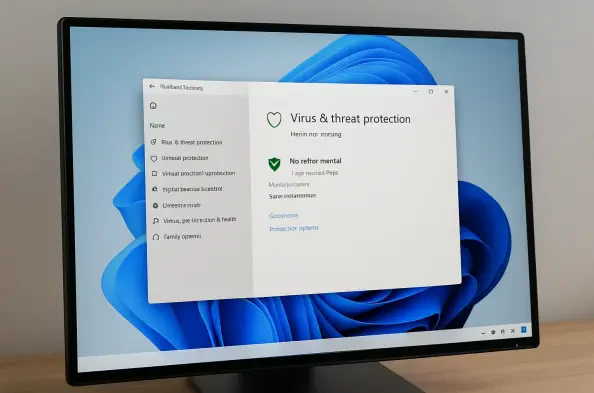
While Microsoft Defender Antivirus stands as a formidable and deeply integrated security solution for Windows 11, providing robust, real-time protection at no extra cost, there are specific, legitimate scenarios where its constant vigilance can become a temporary obstacle. For developers compiling large-scale applications, security researchers