Privacy Protection
The sheer volume of digital fraud reported in 2026 indicates that nearly every active consumer has likely had their personal information compromised in at least one major data breach over the last several years. According to recent federal reports, more than six million incidents of fraud occur annually, pushing identity theft protection services
The digital landscape changed forever when one of the world's largest social media conglomerates decided to pivot away from a core security promise, affecting millions of daily interactions. Meta has officially terminated support for opt-in end-to-end encryption (E2EE) for Instagram direct messages. This move represents a significant reversal of a
The sudden realization that one's highly sensitive financial and medical history has been accessed by unauthorized parties is a nightmare scenario for any modern consumer. Strauss Borrelli PLLC, a nationally recognized law firm specializing in data privacy litigation, has officially launched an investigation into US Mortgage Corporation following
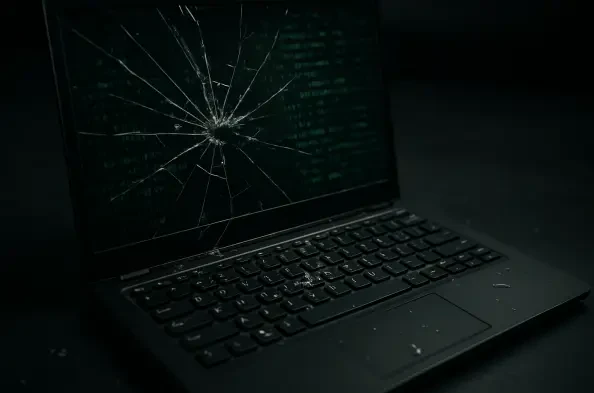
The current landscape of digital security is undergoing a massive shift as traditional methods struggle to keep up with increasingly fluid threats that circumvent historical network perimeters. This transformation marks a decisive move away from protecting fixed digital perimeters toward a more adaptive approach centered on the concept of
The rapid advancement of quantum computing has fundamentally shifted the cybersecurity landscape, turning theoretical vulnerabilities into urgent operational risks for every digital enterprise. While the widespread availability of high-performance quantum processors is still evolving, the cryptographic foundations of the modern internet are