Breach Management
In an era where digital connectivity underpins nearly every aspect of daily life, the threat of cyberattacks looms larger than ever, with California facing an increasing number of data breaches and phishing scams that jeopardize personal and public safety. From malware disrupting critical infrastructure to social engineering tactics targeting
In an era where digital security is paramount, the staggering breach at Capita, a leading British outsourcing firm, stands as a sobering reminder of the high stakes involved in protecting sensitive data. In 2023, the personal information of 6.7 million individuals was compromised, resulting in a hefty $18.7 million fine (14 million pounds) from
In a digital era where data serves as both currency and weapon, a chilling breach has shaken the very foundations of national security, exposing critical vulnerabilities in the systems meant to protect us. A hacker collective known as "the Com" has publicly released the personal details of hundreds of US federal officials from agencies such as the
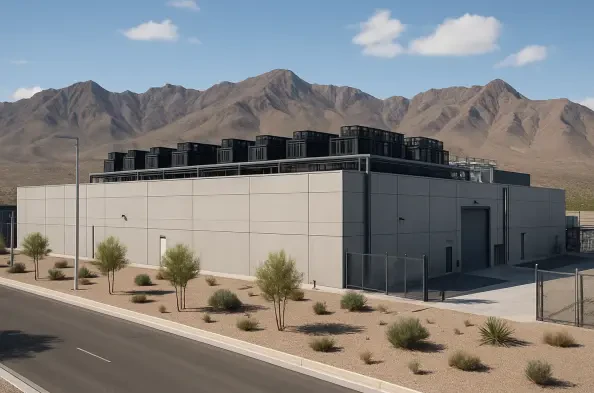
In a landscape where artificial intelligence is reshaping industries at an unprecedented pace, Meta Platforms has made a bold $1.5 billion investment in a new data center in El Paso, Texas, marking its 29th global data center and third in the state. This facility is poised to become a cornerstone for AI infrastructure with a staggering 1-gigawatt
In a striking display of defiance, over 30 major US news organizations have banded together to reject a newly introduced Pentagon press access policy, igniting a heated debate about the balance between national security and press freedom. Under the leadership of Defense Secretary Pete Hegseth, the policy imposes stringent rules on journalists