Cloud Security
A meticulously documented cyberattack on an Amazon Web Services environment has sent a chilling message through the cybersecurity community, demonstrating that artificial intelligence is no longer a theoretical threat but a potent weapon that can compress a complex cloud intrusion into the time it takes to brew a pot of coffee. The incident,
The polished privacy dashboards and reassuring corporate statements from Big Tech often obscure a stark reality where the most robust security protections remain just out of reach for the average user, locked behind optional settings and unfulfilled promises. This growing divide between the marketing of privacy and the mechanics of its
The very concept of a secure corporate network, once envisioned as a digital fortress with impenetrable walls, is dissolving in the face of modern operational realities. As organizations increasingly embrace decentralization and migrate their critical workloads to complex multi-cloud and hybrid environments, the traditional security perimeter has
Microsoft’s strategic decision to integrate telemetry capabilities equivalent to its highly regarded System Monitor (Sysmon) utility directly into the Windows 11 operating system marks a pivotal moment in the evolution of endpoint security. For years, security professionals have treated Sysmon not as an optional tool but as a foundational
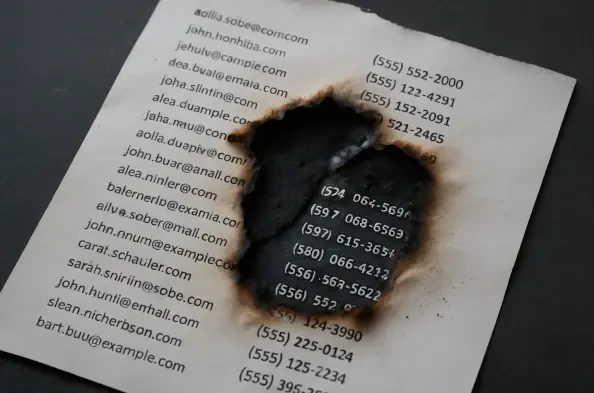
The simple act of subscribing to a newsletter has become a cornerstone of modern content consumption, but it now comes with a critical question about the security of the personal information traded for access to creators. Substack, a dominant force in the independent publishing world, recently confirmed a significant data breach, shaking the