Data Segmentation & Isolation
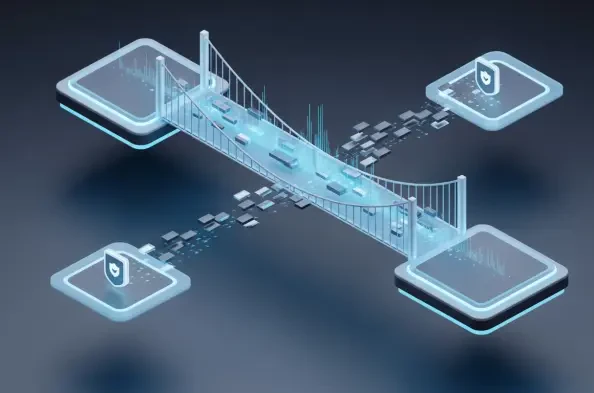
The digital ecosystem has evolved into a complex web where the traditional concept of a protected corporate perimeter has effectively dissolved into a series of interconnected relationships. Managed Service Providers (MSPs) are currently witnessing a transformative shift as Third-Party Risk Management (TPRM) moves from a niche compliance
The rapid disappearance of the traditional network perimeter has forced a radical rethinking of how organizations protect their most sensitive digital assets. As enterprises migrate to complex multi-cloud environments, the old method of guarding the "front door" with a single firewall has become obsolete. Today, the real battlefield is identity,
For decades, the towering monoliths of global finance have relied on COBOL-based infrastructure that remains remarkably stable yet increasingly incompatible with the rapid velocity of modern digital demands. This intersection of ancient logic and cutting-edge intelligence has birthed a phenomenon where tools like Anthropic’s Claude Code are no
Vernon Yai is a preeminent authority in data protection, known for his deep expertise in privacy governance and the mechanics of risk management. With a career dedicated to safeguarding sensitive information, he has become a leading voice in the development of innovative detection and prevention techniques tailored for the modern enterprise. As
When a massive data leak makes headlines, the technical post-mortem almost always highlights a specific misconfiguration, yet the silent catalyst is usually a failure of corporate imagination and leadership. While a security engineer might point to an open S3 bucket or an overly permissive API as the primary culprit, these technical lapses are