Encryption Techniques
In an era where digital security is paramount, a menacing new ransomware strain known as BQTLOCK has emerged as a significant danger to Windows users across the globe, catching the attention of cybersecurity experts due to its sophisticated design and devastating impact. This malicious software, distributed through unconventional channels like
In an era where data breaches and system vulnerabilities dominate headlines, the quest for secure and reliable storage solutions has never been more critical, prompting innovators to rethink filesystem designs from the ground up with a focus on resilience and safety. RedoxFS, an integral part of the Rust-based Redox Operating System, emerges as a
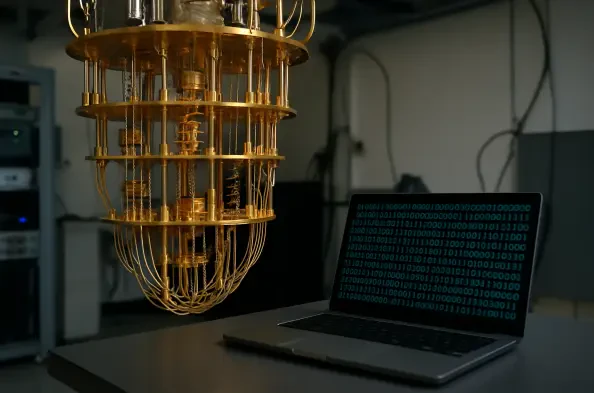
Imagine a world where the digital locks protecting sensitive information—banking transactions, government secrets, and personal data—are suddenly rendered useless by an unstoppable computational force. Quantum computing, with its potential to solve complex problems at speeds unimaginable to traditional systems, poses exactly this threat to current
Introduction to Google Password Manager Review In an era where digital threats loom larger than ever, with over 80% of data breaches linked to weak or reused passwords, the need for robust password management has never been more critical, setting the stage for evaluating tools designed to safeguard online identities. This pressing challenge
In an era where digital privacy is increasingly under scrutiny, a significant clash between governmental authority and technological innovation has emerged in the United Kingdom, spotlighting the delicate balance between national security and individual rights. The UK government, through its Home Office, has issued a renewed demand to Apple, one