Encryption Techniques
In a world increasingly defined by digital interactions, the clash between national security imperatives and individual privacy rights has never been more pronounced, especially when it comes to encrypted technologies that safeguard personal data. A significant milestone in this ongoing debate has recently unfolded as the British government has
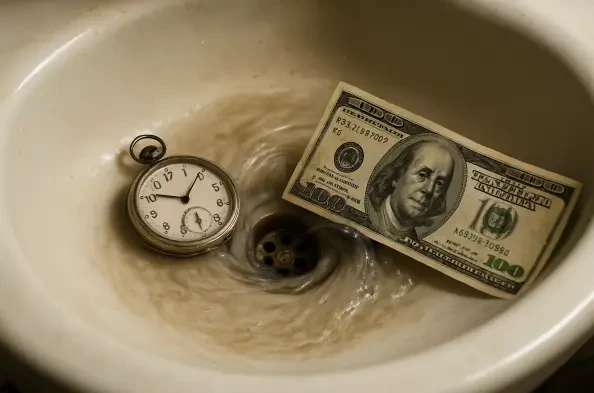
Imagine sitting at a desk on a busy Tuesday afternoon, with a critical project deadline looming, only to realize that the last three hours have been spent tinkering with a shiny new AI tool discovered on a social media platform. What started as a quick test to boost efficiency ended up costing $50 in credits and an entire afternoon, leaving the
What happens when the very tools meant to protect law enforcement become their greatest vulnerability? Picture a high-stakes operation where police officers rely on encrypted radio communications to coordinate a critical response, only to find their messages intercepted and manipulated by unseen adversaries. This chilling scenario is no longer
In a digital landscape where cybersecurity threats evolve at an alarming pace, a new and formidable adversary has emerged, challenging even the most advanced security infrastructures with its cunning tactics. Detected in early August this year by specialists in Türkiye, a sophisticated Java-based malware known as SoupDealer has demonstrated an
Unveiling a Hidden Threat in Cloud Container Management Imagine a scenario where a seemingly harmless container in a cloud environment becomes the gateway for attackers to seize control over an entire infrastructure, exposing sensitive data and compromising critical workloads. This alarming possibility has come to light with the discovery of a