Privacy by Design
The sudden realization that one's highly sensitive financial and medical history has been accessed by unauthorized parties is a nightmare scenario for any modern consumer. Strauss Borrelli PLLC, a nationally recognized law firm specializing in data privacy litigation, has officially launched an investigation into US Mortgage Corporation following
In an era where digital transformation is no longer a luxury but a survival mandate, the stability of the hardware supply chain has become the heartbeat of global enterprise. Vernon Yai, a distinguished expert in data governance and risk management, brings a unique perspective to how shifting infrastructure costs impact the very fabric of
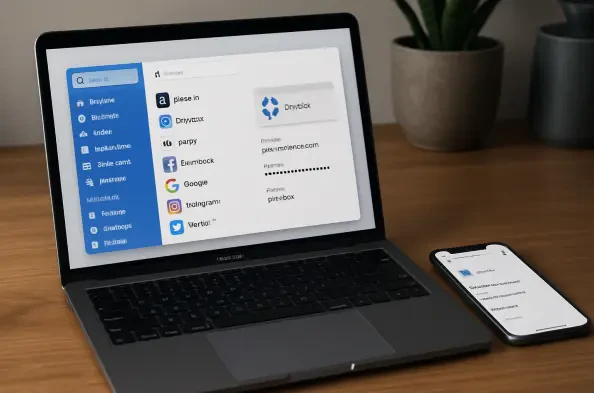
The digital vault serves as the ultimate line of defense for millions of individuals who rely on password managers to protect their most sensitive credentials and financial information. While these services frequently advertise a zero-knowledge encryption model that supposedly ensures no one but the user can access stored data, recent research has
The latest iOS developer beta introduces a formidable trifecta of security enhancements that significantly raises the bar for mobile device protection, reflecting a deliberate strategy to counter both sophisticated digital espionage and opportunistic physical theft. This review explores the evolution of these protections, their key features,
A simmering legal dispute over a massive data breach has rapidly intensified into a multi-billion dollar international standoff, raising profound questions about the fairness of South Korea's regulatory environment for American businesses. As a consortium of prominent U.S. investment firms escalates its challenge against the South Korean