Risk Management
Diving into the world of cybersecurity, we’re thrilled to sit down with Vernon Yai, a renowned data protection expert with a sharp focus on privacy protection and data governance. With years of experience in risk management and a passion for pioneering detection and prevention strategies, Vernon is a trusted voice in safeguarding sensitive
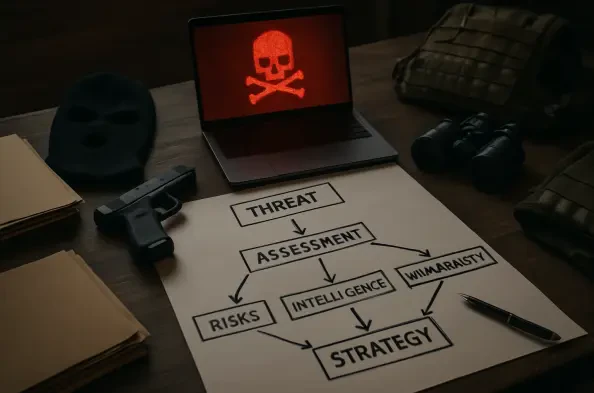
Unveiling a National Vulnerability in Cyber Defense In a digital landscape where cyber threats evolve at an unprecedented pace, a staggering reality emerges: many U.S. states lack the financial muscle to safeguard critical infrastructure, exposing the nation to severe risks. As cyberattacks targeting power grids, water systems, and election
Vernon Yai is a renowned data protection expert with a deep focus on privacy protection and data governance. As a thought leader in the cybersecurity industry, Vernon has dedicated his career to pioneering risk management strategies and cutting-edge techniques for safeguarding sensitive information. In this interview, we dive into the complex
In 2025, imagine a world where artificial intelligence (AI) seamlessly powers every corner of business operations, from crafting strategic plans to handling customer inquiries in real time. Yet, despite this transformative capability, many organizations remain on the sidelines, gripped by concerns over data leaks, system failures, and regulatory
What if the backbone of tomorrow’s groundbreaking AI solutions lies not in flashy algorithms, but in the often-overlooked IT department? A staggering 86% of IT leaders now assert that their teams are the linchpin for scaling artificial intelligence securely across enterprises, according to a recent Forrester Consulting study. This revelation