Third-Party Risk Management
The global cybersecurity landscape is currently grappling with a sophisticated architectural shift that threatens to render traditional law enforcement takedown strategies obsolete. For decades, the primary method for dismantling malicious networks involved seizing centralized command-and-control servers or neutralizing registered domains, but the
Modern cyber adversaries have moved beyond the low-hanging fruit of guessed passwords, pivoting instead to a sophisticated era where technical precision defines the new digital battleground. This fundamental transformation reveals that human-centric errors are being superseded by high-speed technical exploitation. The Shift from Credential Abuse
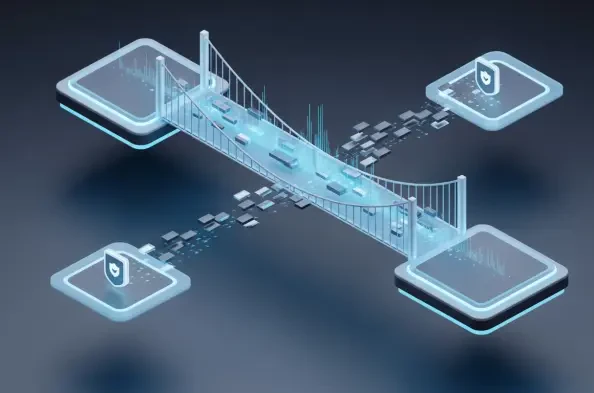
The rapid disappearance of the traditional network perimeter has forced a radical rethinking of how organizations protect their most sensitive digital assets. As enterprises migrate to complex multi-cloud environments, the old method of guarding the "front door" with a single firewall has become obsolete. Today, the real battlefield is identity,
The traditional vision of a unified, borderless digital ecosystem is rapidly dissolving as nations prioritize technological self-reliance over the cost efficiencies once promised by globalized cloud infrastructure. This pivot toward digital protectionism, frequently labeled as tech nationalism, signifies the strategic deployment of policy to
The transformation of Adobe from a boutique creative software provider into the backbone of global enterprise intelligence marks one of the most significant shifts in the modern technological landscape. While many companies are still experimenting with localized AI tools, Adobe has successfully positioned itself at the center of a $2.5 trillion