Akari Saito
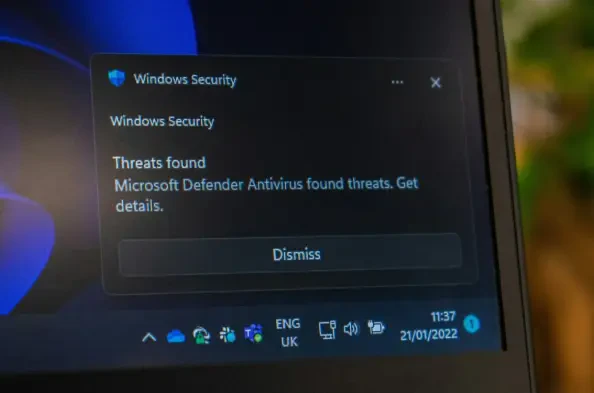
Encryption & Privacy ConsultantIn the evolving world of technology, software updates, security features, and antivirus programs play a significant role in our daily digital lives. As of 2025, Microsoft Defender, a built-in antivirus tool on Windows, remains a crucial application that scans your files and monitors your system for potential threats, providing a robust line of
In today's rapidly evolving financial landscape, Stripe has become an innovative force, reshaping payments with artificial intelligence and stablecoins. As businesses and consumers alike seek more secure, efficient, and global payment solutions, Stripe's advancements in financial technology are particularly significant. These innovations were
The rapidly advancing world of cybercrime presents a formidable challenge to individuals and organizations alike. One of the most significant trends in this dark arena is the rise of Malware-as-a-Service (MaaS), which is revolutionizing how cybercriminals operate. In an era marked by technological advances and digital integration, MaaS has emerged
In the current digital landscape, the quest for antivirus software that effectively balances performance with security remains paramount. Computers are integral to daily life, yet their functionality can be compromised by inadequate security measures. Antivirus solutions must not only provide robust security but also maintain system efficiency to
A cyber incident involving SK Telecom, South Korea's leading mobile network operator, has raised significant alarm in the global technology and telecommunications sectors regarding cybersecurity threats. The attack, which targeted the operator's system on April 19, 2025, compromised sensitive Universal Subscriber Identity Module (USIM) data,
Leveraging AI in Retail: A New Era OpenAI's integration of shopping capabilities into ChatGPT marks a pivotal moment in the evolution of consumer technology. This advancement creates a bridge between AI-driven conversational tools and practical consumer applications, revolutionizing how individuals interact with digital storefronts. The evolution