Elena Bailón
Breach Response StrategistThe digital environment for Android users has transformed into an intricate web of sophisticated threats where a single tap on the wrong link can lead to catastrophic data loss, identity theft, or financial ruin. As the global dominance of the Android operating system continues to grow, so does its appeal as a primary target for malicious actors.
With the conclusion of Microsoft's mainstream support for Windows 10, a significant portion of the world's computer users are now navigating a digital landscape that has fundamentally changed. The operating system that powers millions of devices did not cease to function overnight, but the invisible, automated shield of continuous security updates
The modern digital landscape increasingly resembles an unwinnable game of "online Whac-A-Mole," where the constant emergence of new risks, from sophisticated data breaches to identity theft, makes it nearly impossible for any single person to stay ahead of cybercriminals. As online threats become more sophisticated and pervasive, the necessity for
The very software tools designed to protect digital creations and intellectual property are increasingly being turned into formidable weapons by cybercriminals, creating a new and challenging front in cybersecurity. In this evolving landscape, threat actors are no longer just building malicious code from scratch; they are cleverly wrapping their
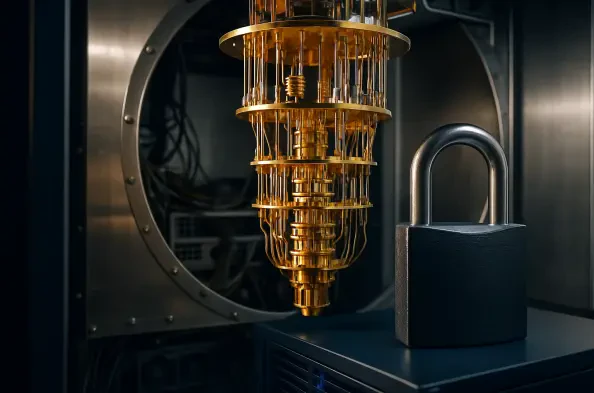
The entire architecture of digital trust, from secure financial transactions to confidential communications, rests upon cryptographic standards that are rapidly approaching their obsolescence. A new class of machine, the quantum computer, operates on principles that fundamentally rewrite the rules of computation, rendering the mathematical
The latest evolution in the ransomware landscape has arrived with a variant that blurs the lines between data extortion and pure destruction, forcing security teams to re-evaluate their defense-in-depth strategies. HardBit 4.0 marks a significant departure from typical ransomware-as-a-service models by integrating a vintage file infector, Neshta,