Isla Bailey
Cloud Security SpecialistVernon Yai stands at the critical intersection of rapid technological evolution and the rigid necessities of corporate data security. As a data protection expert specializing in privacy governance, he has witnessed the "Shadow AI" phenomenon transition from a niche IT concern to a systemic enterprise risk. In an era where the pressure to automate
Enterprises across the globe are currently discovering that the primary bottleneck to scaling generative artificial intelligence is not the lack of sophisticated models, but rather the underlying complexity of fragmented and unoptimized data architectures. To address these persistent infrastructure hurdles, IBM and Nvidia have established a deeper
The increasing sophistication of digital exploits has forced a fundamental rethink of how software ecosystems manage vulnerability remediation without disrupting the daily workflows of millions of users worldwide. Apple has introduced a mechanism titled Background Security Improvements to accelerate the delivery of critical protections for its
The rapid transformation of a legitimate security auditing tool into a high-speed data extraction engine has recently caught the global cybersecurity community off guard. Salesforce recently issued a stark warning regarding a surge in malicious activity where threat actors are leveraging a customized version of AuraInspector to strip sensitive
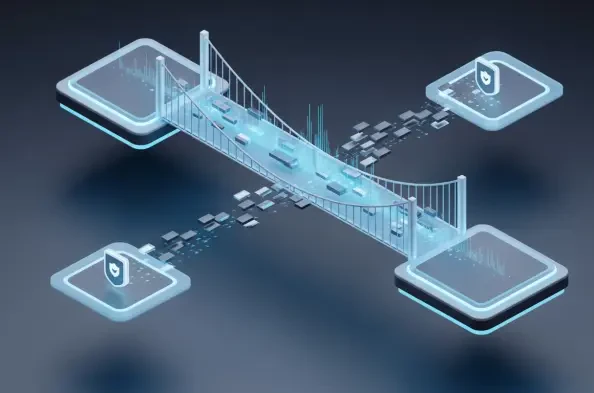
The rapid disappearance of the traditional network perimeter has forced a radical rethinking of how organizations protect their most sensitive digital assets. As enterprises migrate to complex multi-cloud environments, the old method of guarding the "front door" with a single firewall has become obsolete. Today, the real battlefield is identity,
The Dawn of a New Era in AI-Driven Cybersecurity Consolidation The completion of Google’s $32 billion acquisition of Wiz marks a watershed moment in the technology sector, signaling a fundamental shift in how cloud infrastructure is protected. As the largest acquisition in the history of the cybersecurity industry, this deal represents more than