Isla Bailey
Cloud Security SpecialistA New Era of Intelligence: Transforming Static Data into Active Reasoning The rapid convergence of sophisticated machine learning models and massive enterprise datasets has finally pushed the corporate world past the limitations of traditional cloud storage and toward a reality where data acts as its own pilot. This strategic initiative marks a
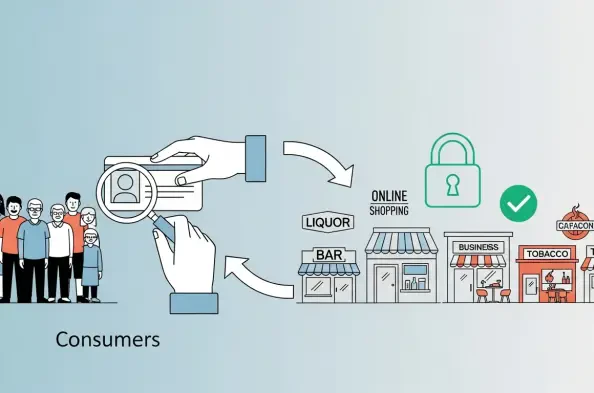
*]:pointer-events-auto R6Vx5W_threadScrollVars scroll-mb-[calc(var(--scroll-root-safe-area-inset-bottom,0px)+var(--thread-response-height))] scroll-mt-(--header-height)" dir="auto" data-turn-id="264aedad-09e4-4c03-b97f-bc729c8a51e3" data-testid="conversation-turn-3" data-scroll-anchor="false" data-turn="user"> For many enterprises, age checks have
Navigating the New Era of Executive Intelligence The global banking sector is undergoing a fundamental reorganization of its power structures as artificial intelligence transitions from a speculative trend to a core driver of financial performance. As the traditional executive suite undergoes a radical redesign, financial institutions are pivoting
Vernon Yai is a titan in the world of data governance and risk management, known for his relentless focus on how sensitive information flows through complex network architectures. As an industry thought leader, he has built a career on identifying the subtle cracks in enterprise defense before they can be exploited by malicious actors. In an era
The traditional boundary separating information technology from core business strategy has permanently dissolved as artificial intelligence becomes the fundamental nervous system for every competitive global enterprise. This shift marks the definitive end of the era when the Chief Information Officer functioned as a back-office manager focused on
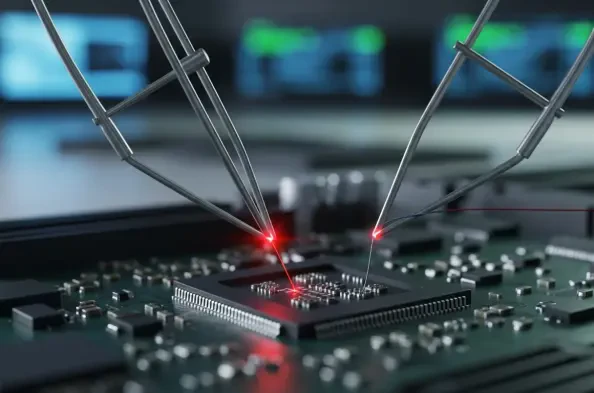
The foundational layer of trust that protects billions of personal computers from sophisticated boot-level malware is undergoing its most significant transformation since the inception of the modern Secure Boot standard. Microsoft is currently implementing a critical update to replace the legacy 2011 Unified Extensible Firmware Interface