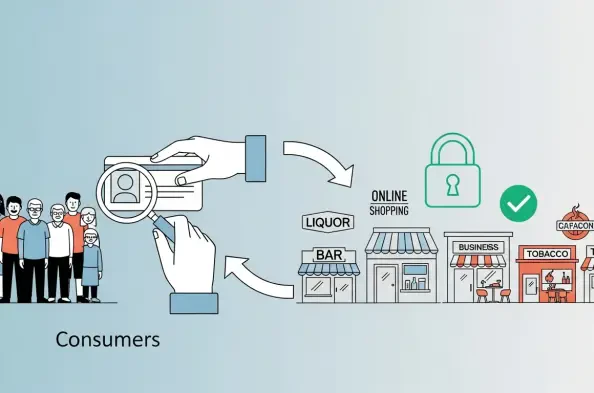
For many enterprises, age checks have moved from being a nice-to-have element in the legal department for compliance to a mandatory item on the product roadmap. More than ever, they influence conversion, brand safety, and the cost of doing business. Decision-makers must treat them as part of the business, with clear service-level agreements, rather than as one-off compliance tasks. And the companies that will win in 2026 are those delivering age assurance that is fast, private, and portable across all relevant business regions without eroding trust or creating risks.
What are age checks? Age verification confirms that a user meets a minimum threshold, but the real question is how to verify this attribute with minimal friction and limited data exposure. Legacy flows that require credit card details or full identity documents increase abandonment and create new attack surfaces. A modern approach proves only what is strictly necessary. Over 18 is an attribute, not an identity, and the design goal is simple: share less data, decide faster, store almost nothing.
As organizations continue adapting to requirements, compliance pressure is intensifying across major markets. The United Kingdom Online Safety Act imposes duties of care that make age assurance a live operational requirement for high-risk services, and the UK regulator, Ofcom, is issuing detailed codes and enforcement timelines. The European Union Digital Services Act also sets expectations for protecting minors, including risk assessments and mitigations for large platforms. Global brands are now subject to obligations at the country and state levels, which means any age verification solution must adapt flexibly to local rules without compromising the user experience.
However, users have grown increasingly more wary of repeatedly uploading sensitive documents. Every extra piece of personal data collected is a future liability. The average cost of a data breach was around $4.4M in 2025, which turns bloated verification flows into tangible balance-sheet risk. The strategic posture is clear. Minimize data collection, shorten retention windows, and prefer proofs over raw documents wherever possible.
Technology Options: Age Estimation
AI-based age estimation has matured quickly, moving from rough demographic guesses to systems capable of producing usable compliance signals in real time. Modern approaches rely on deep learning models trained on large, diverse datasets of facial images, often combined with contextual or behavioral signals such as typing cadence, browsing patterns, or voice characteristics. In practical and realistic deployments, the user experience is simple: a selfie or short live capture is analyzed, and within seconds, the system outputs either a predicted age or, more commonly, a confidence score that the individual is above or below a regulatory threshold (for example, 13, 16, or 18 years old).
Unlike document-based verification, this approach to age estimation avoids the collection and storage of sensitive government identifiers. It reduces both operational friction and regulatory exposure, particularly under data protection frameworks such as the General Data Protection Regulation, which emphasize data minimization. It also lowers barriers for users who may not have access to official IDs or are reluctant to share them online. For low-risk scenarios (such as gating access to general-audience content or tailoring user experiences), this lightweight framework can be sufficient.
However, the technology is not without limitations, and responsible deployment requires active governance. The first major concern is bias and fairness. Age estimation models can perform unevenly across demographic groups, particularly when training data lacks diversity. Variations in skin tone, lighting conditions, cultural presentation, and even camera quality can affect accuracy. As a result, providers should publish disaggregated performance metrics, including error rates by age, gender, and ethnicity. Independent audits and standardized benchmarks are also critical to building trust and ensuring accountability.
The second issue is the appropriateness of the context, because estimation is inherently probabilistic. While a system may achieve low mean absolute error rates overall, individual predictions can still be wrong, especially near threshold boundaries. For higher-risk use cases, such as access to regulated goods or services, estimation alone is rarely sufficient. It should be paired with step-up verification methods, such as document checks or cryptographic credentials, when confidence is low or risk is high.
Attribute-Based Proofs Beat Full Identity
A shift is happening in digital identity: from sharing full identity records to proving only what is necessary. Attribute-based proofs embody this shift by allowing individuals to demonstrate specific claims (including age) without revealing underlying personal data such as birthdate, name, or address. This is made possible through advances in cryptography, particularly selective disclosure and zero-knowledge proofs.
In a typical flow, a trusted issuer (such as a government agency or financial institution) issues a digital credential attesting to a user’s attributes, which can be stored in a secure wallet. When a verifier needs to confirm eligibility, the user can generate a cryptographic proof that satisfies the requirement (e.g., “over 18”) without exposing any additional information. The verifier can check the proof’s validity mathematically, without contacting the issuer or accessing raw personal data.
World Wide Web Consortium has accelerated the standardization of this model through its Verifiable Credentials framework. The release of Verifiable Credentials 2.0 established a common data model and interoperability guidelines, enabling ecosystems of issuers, holders, and verifiers to function across platforms and jurisdictions. It’s a crucial level of standardization: without it, each provider would create incompatible systems, undermining scalability and adoption.
The benefits are substantial for enterprises following this path. First, privacy is significantly enhanced because verifiers receive only the minimum necessary information, reducing the risk of data breaches and misuse. Second, compliance becomes simpler. Organizations no longer need to store large volumes of sensitive personal data, thereby reducing the burden under regulations such as the General Data Protection Regulation and similar frameworks worldwide. Third, cross-border interactions become more efficient, as standardized credentials can be recognized across jurisdictions without the need for complex data-sharing agreements.
Device Signals and Wallets
Age assurance is being reimagined through trusted user devices and digital wallets. In this model, age verification occurs once through a robust process, such as document verification or in-person validation, and the result is stored securely on the user’s device or in a wallet application. Thereafter, when a service needs to confirm eligibility, it can request a simple attestation: for example, “Is this user over 16?” The device responds with a yes/no answer, often backed by cryptographic proof.
The framework offers a streamlined user experience. Instead of repeatedly uploading documents or undergoing checks across multiple platforms, users benefit from a “verify once, reuse many times” paradigm. It also reduces the duplication of sensitive data across services, lowering the attack surface for breaches. From an architectural perspective, it concentrates sensitive processing within a smaller number of hardened components (operating systems, secure enclaves, and wallet applications) rather than distributing it across thousands of websites with varying security postures.
Policy developments are accelerating this model, particularly in Europe. The revision of the eIDAS Regulation introduced the concept of interoperable digital identity wallets that can be used across member states. These wallets are expected to support a wide range of credentials, including proof of age, and to enable secure, user-controlled sharing of attributes. Large platform providers are likely to align with this direction, integrating wallet-based verification into their ecosystems.
The Bottom Line
Age assurance has become an experience problem as much as a compliance problem. The winning strategy is to prove attributes, not identities. Use privacy-preserving proofs and device or wallet signals where possible. Reserve document checks for step-up flows or high-risk gates, keep the system observable through KPIs tied to revenue and risk reduction, and invest in configuration and localization so that one code path can satisfy many regimes without fragmenting the product experience.
There is no one-size-fits-all solution, and there will be edge cases that demand human review. Standards will continue to evolve, national rules will diverge, and customers will push back on flows that feel invasive. That is the point of a risk-tiered, attribute-first design. It acknowledges complexity while keeping the system simple where it matters to users and sustainable where it matters to operators.