Isla Bailey
Cloud Security SpecialistThe traditional grocery landscape is undergoing a radical metamorphosis as data-driven intelligence shifts from a supportive function to the primary engine of corporate strategy. Kroger has taken a definitive step toward this future by establishing the new role of Chief Data and AI Officer, a move that signals a comprehensive pivot toward a
The sudden proliferation of autonomous artificial intelligence agents across corporate networks has fundamentally altered the baseline of digital operations, turning what were once static analytical tools into independent decision-makers. While initial iterations of AI focused on passive observation and defensive monitoring, the current generation
The relentless pursuit of digital agility has forced modern enterprises to confront a staggering reality where the sheer speed of AI-driven software development is frequently neutralized by the stagnant bureaucracy of legacy network security protocols. In the race to achieve complete digital transformation, many organizations are hitting a
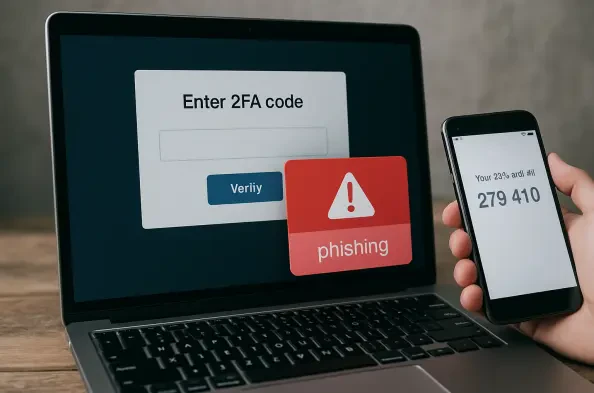
The illusion of absolute security provided by multi-factor authentication has been shattered by the realization that even the most robust digital locks can be picked if the burglar controls the hallway. As organizations increasingly leaned on secondary verification to defend their perimeters, a sophisticated adversary emerged to exploit the very
The rapid evolution of quantum computing has fundamentally shifted the cybersecurity landscape, moving the primary concern from classical brute-force attacks to the sophisticated realm of quantum-level decryption. While significant industry resources have been poured into hardening massive data centers and central cloud hubs, a glaring
The rapid migration of sophisticated threat actors from the dark web to mainstream messaging platforms has redefined the modern cybersecurity landscape, turning instant communication tools into weaponized environments. What once served as a simple encrypted chat application has morphed into a sprawling, multi-layered marketplace where the barrier