Joshua Kaina
Secure Transfer ExpertThe rapid transformation of the digital threat landscape has reached a critical juncture where the traditional manual methods of cyber warfare are being replaced by highly efficient, automated systems. As large language models and specialized agentic frameworks become more accessible, the barrier to entry for conducting sophisticated cyberattacks
The current digital landscape has forced a radical shift in how defensive architectures prioritize visibility across thousands of interconnected endpoints that form the modern enterprise network. As security engineers deploy increasingly complex detection and response agents, adversaries have pivoted toward methods that do not necessarily disable
The sudden emergence of the Payouts King ransomware group represents a paradigm shift in the digital extortion landscape, where seasoned criminal expertise meets advanced technical engineering to dismantle even the most robust corporate perimeters. This threat actor did not materialize from a vacuum but rather crystallized from the remnants of
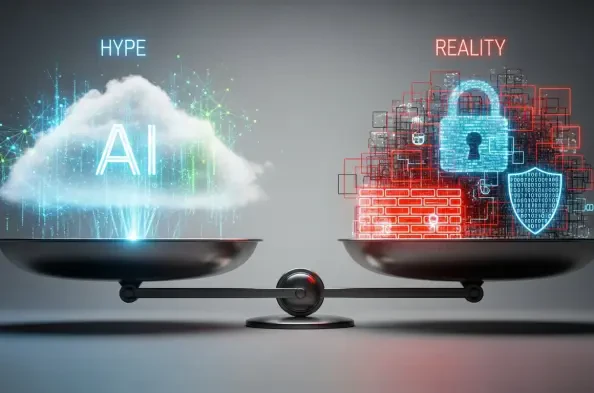
The current cybersecurity landscape is dominated by a relentless stream of artificial intelligence marketing that often blurs the line between revolutionary innovation and sensationalist fearmongering. Chief Information Security Officers are currently finding themselves in a complex position where they must differentiate between actual threat
The rapid integration of autonomous intelligence into offensive cybersecurity toolkits has reached a critical milestone with the emergence of frameworks designed to bypass modern security controls. These systems leverage large language models to orchestrate multi-stage attacks that previously required significant human expertise to execute
The rapid evolution of Large Language Models has transitioned from simple text generation to the deployment of sophisticated agents capable of navigating complex environments and executing multi-step tasks without human intervention. Security researchers have observed a concerning trend where these autonomous entities are no longer just theorized