Joshua Kaina
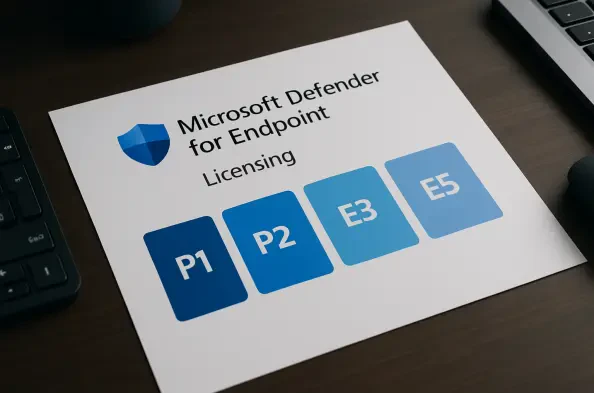
Secure Transfer ExpertModern cybersecurity professionals no longer view endpoint protection as a secondary defensive layer but rather as the primary battleground where the integrity of an entire corporate network is decided. Microsoft Defender for Endpoint represents a fundamental shift in how organizations approach this challenge, moving away from the antiquated model
The next time your digital assistant suggests adding Hellmann's mayonnaise to your cart, the recommendation might originate not just from your past purchases but from a sprawling new system of intelligence designed by Unilever and Google Cloud. Consumer goods giant Unilever has entered into a landmark five-year strategic partnership with Google
The digital foundation of modern computing experienced a significant reinforcement this month as chipmaking giants Intel and AMD released an unprecedented wave of security patches in a coordinated effort to address critical vulnerabilities. In a massive update for February 2026, the two companies collectively resolved over 80 security flaws
The silent hum of automated processes has given rise to a new operational paradigm where digital agents, once solitary workers, now form sophisticated, coordinated teams to tackle complex business challenges. As this digital workforce begins to collaborate, a critical question emerges: does security complexity scale at the same pace? The
The rapid evolution of cloud infrastructure has rendered traditional incident response playbooks obsolete, leaving many security operations teams struggling to investigate breaches that unfold at a speed their manual processes simply cannot match. Unlike the static environments of on-premises data centers where investigators had the luxury of
The very foundation of confidential computing, which promises to shield sensitive data from even the most privileged administrators, has been shaken by the discovery of a critical vulnerability in one of its cornerstone technologies. A recent collaborative security audit between Google and Intel has brought to light a significant flaw within