The rapid metamorphosis of the enterprise digital landscape has fundamentally rewritten the rules of engagement for cybersecurity professionals who must now defend a perimeter that effectively no longer exists in a traditional sense. In this current environment, the definition of an endpoint has expanded far beyond the isolated laptops or mobile phones of previous years, evolving instead into a strategic control layer that serves as the primary gateway to identity services, cloud infrastructure, and complex AI-driven automation workflows. Organizations have recognized that securing these nodes is no longer just about blocking malicious executables but about managing the intersection of human behavior, machine identities, and decentralized data access. As a result, the industry has undergone a decisive shift away from legacy, signature-based detection mechanisms toward holistic systems that prioritize deep behavioral analytics and autonomous response capabilities. This transition ensures that the endpoint functions not as a vulnerable entry point but as a resilient sensor capable of maintaining integrity within an increasingly interconnected and volatile global business ecosystem.
Modern enterprise architecture now treats the endpoint as the ultimate pivot point for sophisticated actors seeking to infiltrate high-value software-as-a-service environments and cloud-native workloads. Because the workforce is more decentralized than ever, the security of a single device often dictates the safety of the entire corporate network, making identity-aware protection a non-negotiable standard for operational continuity. Current platforms are designed to handle these complexities by integrating seamlessly with broader business systems, providing a unified defense that addresses the risks associated with hybrid work and rapid digital expansion. By focusing on real-time mitigation and the correlation of telemetry across various digital domains, these next-generation solutions ensure that a compromise at the edge does not escalate into a catastrophic breach of core infrastructure. The maturity of these platforms marks a significant milestone in the journey toward a more secure digital future where resilience is built directly into the fabric of every device.
The Decline of Reactive Defense and the Rise of Modern Threats
The obsolescence of reactive security models serves as the primary catalyst for the technological innovations currently dominating the cybersecurity sector. In previous iterations of digital defense, antivirus software relied almost exclusively on extensive signature databases to identify and neutralize known malicious files, but this method has proven increasingly ineffective against modern adversaries who have pivoted toward fileless techniques. These contemporary attackers frequently employ credential abuse and token theft to bypass traditional perimeters, leveraging legitimate user identities to move undetected through sensitive environments. By utilizing native system tools—a sophisticated tactic widely recognized as living off the land—hackers can execute malicious commands that appear completely benign to standard scanners, effectively hiding their activities within the noise of routine administrative tasks. This shift in strategy necessitates a defense mechanism that does not just look for “bad files” but instead monitors for “bad behavior” in real-time.
In addition to the exploitation of identity, memory-level attacks and AI-assisted breaches have become standard components of the modern threat landscape, presenting unique challenges for traditional security frameworks. These advanced threats specifically target the volatile memory of a system to execute code without ever writing data to the physical disk, thereby avoiding detection by conventional file-based scanners. Because these sophisticated methods can easily circumvent older defenses, a broad industry consensus has emerged that protection must be entirely runtime-focused and highly adaptive. Current platforms prioritize the continuous monitoring of active processes, utilizing machine learning to identify subtle anomalies as they occur rather than waiting for a recognizable virus signature to manifest. This proactive stance is essential for defending against zero-day exploits and highly targeted campaigns that are designed to bypass the static defenses that once formed the backbone of corporate security strategies.
Leading Innovators in AI Governance and Layered Prevention
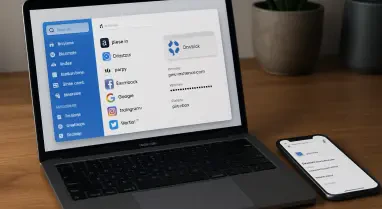
Pluto Security and Bitdefender represent two distinct yet equally vital approaches to the current security landscape, providing organizations with the tools necessary to navigate an increasingly automated digital world. Pluto Security has emerged as a pioneer in the field of AI-aware governance, acknowledging that modern endpoints are no longer exclusively used by humans but also serve as critical nodes for non-human identities and complex automation scripts. Its platform bridges the gap between traditional device activity and broader SaaS governance, ensuring that developers who are building decentralized applications are protected from creation-time risks. By focusing on the unique intersection of artificial intelligence and identity management, Pluto Security offers a level of protection that addresses the specific vulnerabilities of the modern, automated enterprise. This approach is particularly relevant for organizations that rely heavily on automated workflows and require a security solution that can distinguish between legitimate script activity and malicious automation.
Bitdefender continues to excel by focusing on the principles of layered prevention and operational resilience, offering a robust defense-in-depth strategy that remains highly effective against a wide array of threats. Its philosophy centers on high-fidelity detection and the critical ability to recover quickly from security incidents, ensuring that business operations are not permanently derailed by a single breach. A particularly noteworthy feature of its current platform is the advanced anti-ransomware rollback functionality, which empowers administrators to revert an infected system to its exact pre-infection state with minimal effort. This capability is indispensable in a world where ransomware remains a persistent threat, proving that modern security must be as much about rapid recovery and data integrity as it is about the initial prevention of an attack. By combining strong preventive measures with automated remediation tools, Bitdefender provides a balanced approach that addresses both the immediate and long-term needs of the modern digital enterprise.
Integrated XDR and High-Correlation Enterprise Protection
Palo Alto Networks and Trellix have redefined the role of endpoint security by focusing on the power of integration and high-level data correlation across massive, complex infrastructures. Palo Alto Networks utilizes its status as an Extended Detection and Response powerhouse to treat the individual endpoint as just one piece of a much larger, interconnected digital puzzle. By effectively breaking down the historical silos that existed between network, cloud, and endpoint telemetry, it provides security teams with a unified investigation console that delivers cross-layer intelligence. This comprehensive visibility ensures that analysts can track the progression of an attack from its initial entry point through to its ultimate target, preventing the endpoint from becoming an isolated blind spot in the overall defense strategy. The ability to see the “big picture” in real-time allows organizations to respond more effectively to sophisticated, multi-stage campaigns that might otherwise go unnoticed.
Trellix specifically targets large-scale organizations that require the correlation of vast amounts of telemetry data to identify and neutralize complex, multi-stage attacks. Some of the most dangerous threats currently facing enterprises may appear completely harmless when viewed in isolation on a single device, only revealing their malicious nature when analyzed across the entire corporate infrastructure. The strength of the Trellix platform lies in its centralized analytics engine, which is capable of spotting these intricate sequences by correlating events from thousands of different nodes simultaneously. This high-level correlation is absolutely vital for identifying advanced persistent threats that attempt to hide their movements within the massive volume of noise generated by a global corporate network. By turning disparate data points into actionable intelligence, Trellix enables security operations centers to maintain a proactive defense posture that is capable of anticipating and disrupting even the most stealthy adversarial tactics.
Predictive Prevention and Synchronized Defense Strategies
Check Point and Sophos place a heavy emphasis on proactive measures and real-time coordination, seeking to stop potential threats long before they have the opportunity to escalate into full-blown breaches. Check Point’s current strategy is built on a foundation of predictive threat modeling and advanced anti-exploit technology that targets the specific techniques used by modern ransomware actors. By utilizing sophisticated AI to detect anomalies in process behavior and credential usage, the platform can identify and block malicious activity during its earliest stages. The overarching goal of this approach is to prevent the execution of an attack entirely, adhering to the fundamental principle that stopping a breach before it starts is always more cost-effective and less damaging than remediating one after the fact. This focus on predictive prevention ensures that organizations can stay one step ahead of attackers who are constantly evolving their methods to bypass traditional defenses.
Sophos utilizes a unique synchronized security model that facilitates constant, high-speed communication between different security layers, such as the endpoint and the network firewall. If an individual endpoint identifies a potential threat or exhibits suspicious behavior, it can automatically signal the network to isolate the affected device without requiring any manual intervention from an IT administrator. This creates an immediate, automated containment barrier that prevents an attacker from moving laterally through the system to access more sensitive data or infrastructure. This level of real-time, automated coordination significantly reduces the burden on human analysts and ensures that response times are measured in seconds rather than the hours or days it might take for a human to intervene. By integrating the endpoint and the network into a single, cohesive defense system, Sophos provides a level of operational security that is specifically designed to counter the high-velocity attacks common in today’s digital landscape.
Autonomous Innovation and the Death of the Static Signature
SentinelOne has established itself as a leader in the shift toward truly autonomous security, utilizing advanced machine learning to minimize the need for manual intervention during a security incident. Its platforms are engineered to hunt, contain, and remediate threats in real-time, often acting independently to neutralize a threat before a human analyst has even been alerted to the situation. This degree of autonomy is crucial for reducing dwell time, which is the period an attacker remains undetected within a system and is often the most critical factor in determining the total cost of a breach. In the current environment, the ability for a platform to act decisively and independently is considered a baseline requirement for any enterprise-grade solution, as the speed of modern attacks has long since surpassed the capacity of manual response teams. By automating the most time-sensitive aspects of threat detection and response, SentinelOne allows organizations to maintain a high level of security without requiring a massive increase in staff.
A universal trend among all leading security platforms is the definitive end of the static signature as a primary means of protection, marking a total industry consensus that checking files against a database of known threats is no longer sufficient. Instead, modern platforms focus on intent-based monitoring, asking whether a specific process is behaving in a way that suggests malicious intent, such as unauthorized privilege escalation or unusual data encryption patterns. This behavioral shift, when combined with a deep understanding of identity and SaaS context, ensures that security systems can detect even the most novel and previously unseen zero-day exploits. By moving away from the rigid constraints of signature-based detection, organizations are better equipped to handle a threat landscape that is characterized by rapid change and constant innovation. This transition to behavioral-centric security represents the most significant evolution in endpoint protection since the inception of the antivirus industry, providing a much-needed defense against the next generation of digital threats.
Automation and Operational Resilience in Security Operations
The ultimate objective of endpoint security has undergone a fundamental shift from mere threat detection to the pursuit of total operational resilience, ensuring that organizations can continue to function even during an active attack. Current platforms prioritize the ability to maintain critical business functions by providing features like automated containment and forensic rollback as standard components of their service offerings. These tools allow organizations to isolate specific threats or compromised devices without the need to shut down entire departments or networks, thereby minimizing the financial and operational impact of a security incident. This evolution reflects a realistic and mature understanding of the modern threat landscape, where it is assumed that breaches will eventually occur. The focus has therefore shifted toward ensuring that these breaches are not allowed to disrupt the core mission of the enterprise or lead to prolonged periods of downtime.
For Modern Security Operations Centers, these technological advancements serve as a critical remedy for the persistent issue of alert fatigue, which has long plagued security analysts. Analysts are frequently overwhelmed by a high volume of low-fidelity notifications that lead to dead ends, wasting valuable time and increasing the risk that a genuine threat will be overlooked. Next-generation platforms solve this problem by prioritizing incidents based on behavioral risk and providing context-rich telemetry that explains exactly why an alert was triggered. By handling the most common and easily identifiable threats automatically, these systems free up human experts to focus on high-level strategy and proactive threat hunting. This shift in workload not only improves the overall efficiency of the security team but also ensures that the organization is better prepared to handle the complex, human-led attacks that require a high degree of sophisticated analysis.
Structural Differences Between Traditional and Next-Gen Models
The transition to current security models represents a significant structural upgrade from the traditional frameworks that defined the industry for decades, offering a level of visibility and control that was previously impossible. Legacy models were characterized by periodic system scans and a heavy reliance on manual remediation by IT staff, creating a reactive posture that struggled to keep pace with the velocity of digital business. These older systems often operated in isolation, providing limited insight into how an attack on one device might be connected to broader activity across the network or in the cloud. In sharp contrast, modern models are cloud-native from the ground up and focus on continuous runtime monitoring, providing a real-time stream of telemetry that allows for the immediate identification of suspicious activity. This continuous visibility is the foundation of a proactive defense strategy, enabling organizations to catch threats in their earliest stages before they can cause significant damage.
Under these new models, the very definition of success in cybersecurity has changed to reflect a more nuanced understanding of risk and resilience. In the legacy era, success was often measured by the simple absence of alerts, which frequently provided a false and dangerous sense of security while hidden threats persisted in the background. Today, success is defined by the measurable reduction of dwell time and the effective prevention of lateral movement into sensitive business systems or high-value data repositories. Organizations now place a high value on platforms that offer policy-based guardrails and deep integration with SaaS environments, recognizing that the endpoint is the foundational layer for all secure, AI-driven growth. This shift in metrics emphasizes the importance of agility and responsiveness, ensuring that the security infrastructure is capable of supporting the rapid pace of modern innovation while maintaining a robust and uncompromising defense posture.
To maintain a competitive and secure posture in the current digital landscape, organizations must move beyond the basic implementation of security software and instead focus on building a resilient, identity-centric architecture. The transition to behavioral analytics and autonomous response is no longer an optional upgrade but a fundamental requirement for protecting sensitive data and maintaining business continuity. Leaders should prioritize platforms that offer deep integration with their existing identity and cloud ecosystems, ensuring that security is not an isolated function but a core component of every business process. Furthermore, investing in platforms that provide automated containment and rapid recovery capabilities will ensure that the organization can withstand even the most sophisticated attacks without suffering catastrophic losses. By embracing these advancements, enterprises can transform their endpoints from potential vulnerabilities into powerful assets that drive secure growth and innovation in an increasingly complex world. In the preceding years, the focus was on blocking known threats; today, the focus has successfully shifted to maintaining operational integrity through advanced behavioral intelligence and autonomous mitigation strategies.