Is Acalvio ShadowPlex the Best Deception Technology?
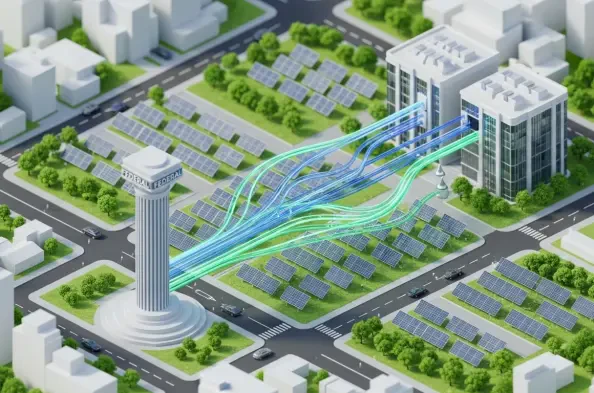
In the current high-stakes landscape of 2026, the traditional model of reactive cybersecurity has become an unsustainable burden for modern security operations centers that are constantly overwhelmed by an endless stream of low-fidelity alerts. While legacy intrusion detection systems and security information and event management platforms have provided the foundation for defensive strategies, they often fail to differentiate between benign user anomalies and genuine malicious intent. This lack of precision forces analysts into a perpetual state of triage, leading to burnout and missed threats. As a result, the industry is witnessing a massive pivot toward preemptive technologies that prioritize early-stage detection through proactive engagement. Gartner recently noted that preemptive security measures will account for more than half of all IT security spending by 2030, a sharp increase from the niche status these tools held only a few years ago. At the heart of this shift lies deception technology, which effectively turns the attacker’s own reconnaissance phase against them. Acalvio ShadowPlex has emerged as a frontrunner in this space by offering a sophisticated, AI-driven platform that does more than just deploy honeypots; it creates an entire fabric of deceptive assets that forces adversaries to navigate a minefield of digital breadcrumbs and honeytokens before they can ever reach their ultimate objective. By focusing on the attacker’s need to explore and harvest credentials, the platform provides a unique vantage point that traditional tools simply cannot replicate.
1. Core Mechanics: Transforming Attacker Intent into Defensive Intelligence
ShadowPlex differentiates itself through its agentless architecture, which utilizes a centrally managed Deception Center to orchestrate a vast array of realistic decoys across hybrid environments. This system avoids the common pitfalls of traditional endpoint-based tools by employing lightweight projection sensors that present deceptive services locally without the need for cumbersome software installations on every production host. These sensors can project everything from simple server facades to complex, high-interaction environments that mimic specific operating systems and cloud-native services. By populating the network with these assets, the platform creates an environment where an attacker’s first step is likely to be their last undetected move. The AI-driven nature of the platform ensures that these decoys are not static; they adapt to the specific naming conventions, inventory patterns, and network topology of the organization, making them indistinguishable from legitimate assets. This realism is critical because sophisticated adversaries often look for signs of deception, such as outdated service versions or inconsistent metadata, to avoid being caught. By automating the design and deployment of these assets, ShadowPlex allows even mid-sized security teams to maintain a robust deception layer that would otherwise require a dedicated staff of specialized engineers to manage and update manually.
Beyond the mere presence of decoys, the true value of this technology lies in the high-fidelity signal it provides to the security operations center. Unlike behavioral analytics, which can be tripped by a developer running a heavy script or an administrator performing late-night maintenance, a deception alert is inherently authoritative because a legitimate user has no business reason to interact with a decoy host or attempt to use a honeytoken. When an alert fires, it is a clear indicator of unauthorized intent rather than a statistical anomaly that requires hours of investigation to validate. This level of certainty allows security teams to automate their response playbooks with a high degree of confidence, knowing that the risk of disrupting business operations is virtually non-existent. Furthermore, the platform integrates seamlessly with existing security stacks, including EDR, SIEM, and SOAR, to feed verified telemetry directly into the tools analysts are already using. This means that a detected interaction with a honeytoken can immediately trigger an endpoint isolation via a tool like CrowdStrike or a credential revocation in Active Directory, drastically reducing the mean time to contain a threat. In an era where lateral movement can happen in minutes, this ability to compress the response cycle through high-confidence detection is a decisive advantage for modern defenders who must operate with limited resources.
2. Implementation Strategy: The Initial Thirty-Day Pilot Phase
Successfully deploying a deception platform requires a structured approach that prioritizes immediate visibility while building a foundation for long-term operational health. During the first thirty days of a rollout, the focus should remain on a controlled pilot program situated within a single physical site and one primary cloud subscription. This initial stage is designed to validate the integration between ShadowPlex and the existing security operations ecosystem, specifically ensuring that alert routing and enrichment function as expected within the SIEM and SOAR platforms. Security teams should begin by seeding a small number of honey accounts in a dedicated test organizational unit and projecting basic decoys near high-value assets. This allows the organization to establish a baseline for mean time to detect and triage, using controlled simulations to verify that the platform captures hostile actions such as credential dumping or lateral RDP attempts. By keeping the initial scope narrow, administrators can iron out any networking or routing issues that might arise when projecting decoys into different segments. This phase is also the ideal time to define the criteria for success, such as the precision of alerts and the speed of the notification chain, which will be used to justify broader expansion in the following months.
As the first month concludes, the team should have a clear understanding of how the platform interacts with authorized activity, such as vulnerability scanners or administrative tools. Establishing a robust whitelist for these legitimate services is a critical step during the pilot phase to prevent the deception layer from generating its own form of noise. Documentation of these exceptions ensures that as the deployment scales, the security operations center maintains a clear view of what constitutes an authorized interaction versus a genuine threat. The pilot phase also serves as an educational period for tier-one analysts, who must become familiar with the specific metadata provided in a deception alert, such as the source host, the specific honeytoken touched, and the captured command history. This familiarity is essential for the rapid classification of incidents as the platform moves into production. By the end of this period, the organization should be ready to transition from a proof-of-concept mindset to an operational one, having proven that the technology can integrate into their daily workflows without creating significant overhead for the IT operations teams or the network administrators who manage the underlying infrastructure.
3. Core Expansion: Scaling Deception to Sensitive Production Enclaves
From day thirty-one to day sixty, the deployment strategy shifts from validation to the protection of the organization’s most critical assets and administrative zones. This expansion should target the five most sensitive network subnets, where the impact of a breach would be most severe, such as those housing core databases or financial systems. During this phase, identity-based deception becomes a primary focus, with honey accounts and service principals being distributed throughout live production organizational units. It is vital during this stage to establish clear ownership for each set of deceptive assets, ensuring that identity teams and security analysts are aligned on the exception rules and maintenance schedules. Cloud-specific tokens should also be introduced into regulated environments, such as those subject to HIPAA or PCI-DSS requirements, provided that strict logging and rotation standards are maintained to meet compliance obligations. This creates a dense fabric of triggers that an adversary is likely to encounter if they manage to breach the perimeter and begin searching for elevated privileges. The goal of this middle phase is to ensure that any lateral movement attempted by an intruder is met with a high-fidelity tripwire that alerts the security team before the attacker can reach their final target.
To validate the effectiveness of the expanded deployment, organizations should conduct a coordinated purple team exercise during this period, specifically focusing on lateral movement and identity misuse techniques. By having internal or external security testers attempt to navigate the protected segments, the defense team can verify that the decoys are believable and that the automated response playbooks function correctly under real-world conditions. The results of these exercises often lead to important refinements in how decoys are presented or how breadcrumbs are placed on endpoints to entice attackers. For example, if a tester is able to bypass a decoy segment by identifying a naming convention discrepancy, the team can adjust the automated design parameters within the ShadowPlex Deception Center to improve realism. This iterative process ensures that the deception layer remains dynamic and continues to challenge the assumptions of even the most skilled adversaries. By the end of the second month, the platform should be fully integrated into the organization’s high-risk zones, providing a robust second line of defense that complements existing endpoint and network security controls while providing much-needed visibility into internal traffic patterns.
4. Enterprise Integration: Broadening Visibility and Establishing Governance
The final phase of the ninety-day rollout focuses on extending the deception fabric to the furthest reaches of the enterprise, including remote offices and industrial (OT) segments where visibility has traditionally been limited. These environments are often targeted by attackers because they may lack the dense telemetry available in central data centers or primary cloud regions. By deploying ShadowPlex projection sensors in these areas, organizations can create early-warning systems that detect unauthorized discovery and lateral probing within sensitive network zones. In OT environments, this requires careful segmentation to ensure that decoys can be interacted with by an intruder without creating any risk to production control systems. This stage also involves finalizing the formal schedules for rotating decoys and updating honeytokens to ensure they do not become “stale” or easily identifiable over time. Effective governance is the hallmark of a mature deception program, and this phase should include the creation of standard operating procedures for system upkeep, including regular audits of whitelisted scanners and the automated update of deceptive credentials. This ensures the long-term durability of the defense.
As the ninety-day mark approaches, the security leadership should begin reporting key performance indicators to senior management that demonstrate the tangible value of the preemptive defense strategy. Metrics such as “detections prior to impact” and the reduction in mean time to contain are particularly effective at communicating the platform’s ROI to non-technical stakeholders. These reports should highlight specific instances where the deception layer provided the earliest signal of a potential incident, allowing the SOC to intervene before data was exfiltrated or systems were compromised. Continuous validation through recurring red team and purple team testing should be established as a standard practice, ensuring that the deception layer evolves alongside the changing threat landscape. This proactive posture transforms the security organization from a reactive cost center into a resilient operational unit that can anticipate and divert threats with surgical precision. By building this culture of continuous testing and improvement, the organization ensures that its investment in deception technology remains a critical pillar of its overall security architecture for the foreseeable future, providing a level of protection that is both scalable and sustainable.
5. Preemptive Defense Components: The Six Pillars of Modern Security
A modern security architecture relies on a collection of proactive controls that work in concert to shape attacker behavior and reduce the overall blast radius of a potential breach. The first pillar of this defense is forecasting threat intelligence, which involves using data to predict the methods and tooling an adversary might use. By anticipating these campaigns, security teams can reinforce likely entry points and harden the attack surface before exploitation occurs. The second pillar is sophisticated cyber deception, where ShadowPlex plays a central role. By diverting intruders into monitored environments, defenders can study their techniques in real-time while using honey accounts to trigger authoritative alerts. This interaction provides invaluable forensic data that can be used to further harden the environment. The third pillar is automated defensive shifting, which increases attacker uncertainty by dynamically changing network routes or the appearance of exposed services. This moving target defense makes it incredibly difficult for an adversary to maintain a persistent foothold or plan a reliable attack path, as the environment they are scanning is constantly in flux, forcing them to spend more time on reconnaissance and increasing the likelihood of they will trip a sensor.
The remaining three pillars focus on internal visibility and the continuous validation of existing controls. Identity Detection and Response (ITDR) is the fourth pillar, specifically designed to monitor for credential theft and unauthorized privilege escalation within environments like Active Directory and Entra ID. ShadowPlex augments this by providing deceptive identities that alert the SOC the moment they are used. The fifth pillar is visibility and exposure control, which involves the continuous mapping of internal and external assets to identify and remediate vulnerabilities before they are exploited. Finally, the sixth pillar is constant security validation through breach and attack simulation. This ensures that the entire stack of defensive controls is actually functioning as intended and that there are no gaps in detection or response. Deception technology sits at the center of these six pillars, acting as a “truth signal” that reduces ambiguity and allows the other components of the security stack to act faster. When a honeytoken is triggered, the organization doesn’t need to debate the probability of a threat; it can immediately move to containment, confident in the accuracy of the signal. This integrated approach creates a formidable barrier that is difficult to bypass and even harder to exploit.
6. Technical Capabilities: Scalability and Forensic Capture Depth
ShadowPlex provides a range of technical features designed to make deception both realistic and easy to manage at scale within complex enterprise environments. The platform’s agentless deployment model is one of its most significant advantages, as it allows for the projection of decoys into diverse network segments without requiring the installation of software on every endpoint. This minimizes the risk of conflicts with production workloads and simplifies the process of achieving broad coverage across the organization. The system offers variable decoy complexity, allowing teams to deploy low-interaction triggers for wide coverage and high-interaction systems for gathering detailed forensic evidence when an intruder is detected. These high-interaction decoys can mirror specific services and applications, providing a rich environment where an attacker can be observed as they attempt to execute their playbooks. This depth of engagement is critical for understanding the techniques, tactics, and procedures used by an adversary, which can then be used to improve the overall security posture of the organization. The ability to switch between these levels of interaction allows for a flexible defense that can be tailored to the risk profile of different segments.
Another critical feature is the platform’s self-managing rotation capability, which automatically updates the appearance and metadata of decoys to ensure they remain believable to sophisticated hackers. Experienced attackers often look for “stale” assets that haven’t changed over time, using them as indicators that a deception layer is present. By rotating these assets, ShadowPlex maintains the integrity of the deception and forces the attacker to continuously re-evaluate their environment. Furthermore, the platform excels at forensic collection, automatically capturing network traffic in PCAP format and recording command histories during any interaction with a decoy. This data is invaluable for incident responders, as it provides a clear record of what the attacker was trying to achieve and how they managed to gain access to the system. This level of detail reduces the time spent on manual investigation and allows for a more rapid and accurate assessment of the scope of a breach. By providing both the trigger and the forensic evidence in a single platform, ShadowPlex streamlines the entire incident response lifecycle, from initial detection to final remediation, making it a powerful tool for any modern security operations center.
7. Operational Analysis: Strengths and Strategic Advantages
The primary strength of Acalvio ShadowPlex lies in its ability to significantly reduce operational friction while simultaneously increasing the quality of security signals. By employing an agentless model, the platform can be deployed rapidly across thousands of segments without the need for extensive change management processes that typically accompany endpoint-based tools. This ease of deployment allows security teams to achieve a high level of coverage in a fraction of the time required by traditional methods. Additionally, the high-fidelity nature of the alerts generated by the platform helps to combat analyst fatigue, which is a major challenge for many modern security teams. When a tier-one analyst receives a deception alert, they can be nearly certain that it represents a legitimate threat, allowing them to prioritize their efforts on the most critical incidents. This precision not only improves the effectiveness of the security operations center but also boosts morale by reducing the time spent on frustrating false positives. The platform’s strong integration with the wider security ecosystem further enhances its value, as it allows for the automated enrichment of alerts and the execution of rapid containment actions.
In addition to these operational benefits, the platform’s ability to provide a “truth signal” within the security stack is a major strategic advantage. By working seamlessly with tools like Splunk, Microsoft Sentinel, and CrowdStrike, ShadowPlex ensures that its high-confidence data is available exactly where it is needed most. This integration allows for a more cohesive and coordinated response to threats, as information from the deception layer can be used to inform actions taken by other security tools. For example, a detection in ShadowPlex can be used to trigger a more aggressive scanning policy in a vulnerability management tool or to increase the logging level on nearby production hosts. This synergy between different layers of the security stack creates a more resilient defense that is greater than the sum of its parts. For organizations operating in highly regulated sectors or those with complex, hybrid environments, the ability to generate clear, actionable intelligence from the internal network is an essential capability. By providing this visibility without the noise of traditional monitoring tools, ShadowPlex enables security leaders to make more informed decisions and to manage risk more effectively in an increasingly dangerous digital landscape.
8. Identifying Constraints: Challenges in Cost and Governance
Despite its many advantages, there are areas where ShadowPlex and the broader deception market could benefit from increased transparency and improved reporting features. One of the primary challenges for organizations considering the platform is the lack of public pricing guidance, which can make initial budget planning and side-by-side comparisons with other technologies difficult. Like many enterprise-grade security solutions, the cost is typically tied to the size of the environment and the specific modules selected, requiring a formal engagement with the vendor to determine the final price. This opacity can be a hurdle for mid-market organizations that need clear cost expectations before embarking on a new security initiative. Additionally, while the platform provides excellent forensic data, there is room for improvement in the out-of-the-box reporting dashboards. Built-in tools for tracking decoy health, rotation status, and overall coverage gaps would reduce the reliance on custom SIEM queries and provide a more intuitive view of the program’s operational health. Hygiene is a daily requirement for any deception program, and having these metrics available at a glance would be a significant benefit for system administrators.
Furthermore, while the technology is highly versatile, organizations in strictly regulated sectors like healthcare or government often require more detailed blueprints to accelerate compliance with frameworks such as FedRAMP or HIPAA. Providing more prescriptive guidance on how to deploy honeytokens and decoys within these scoped environments would help teams navigate the complex governance requirements they face. For example, understanding how to manage the logging of interactions with deceptive assets without violating data privacy regulations is a common concern that could be addressed through more detailed documentation. Similarly, the library of OT-specific decoy templates could be expanded to include a wider range of industrial protocols and device types commonly found in critical infrastructure. While the current support is solid, the unique nature of OT environments means that more turnkey options are always in demand. Addressing these gaps would not only make the platform more accessible to a wider range of organizations but would also strengthen its position as the premier solution for preemptive defense. By continuing to refine these areas, Acalvio can ensure that ShadowPlex remains a vital and user-friendly tool for defenders across all industries.
9. Strategic Directions for Resilient Security Frameworks
The implementation of Acalvio ShadowPlex proved to be a decisive move for organizations seeking to transition from a reactive posture to a proactive defense model that prioritized high-fidelity detection. By successfully deploying a fabric of deceptive assets, security teams were able to shift the burden of uncertainty back onto the adversary, forcing them to operate with increased caution and slowing their progress through the network. The integration of these preemptive signals into existing SOC workflows allowed for a dramatic reduction in response times, as analysts no longer had to spend hours validating every anomalous event. Moving forward, the focus for security leaders should remain on maintaining the hygiene and realism of the deception layer through automated rotation and continuous validation. This proactive approach not only reduced the total cost of potential breaches but also provided a clear, actionable path for improving the overall resilience of the enterprise. By treating deception as a fundamental component of the security stack, organizations ensured they were prepared for the sophisticated threats of 2026 and beyond.
Future considerations for deception programs should include the further automation of response playbooks and the expansion of identity-centric defenses into every layer of the hybrid cloud environment. As attackers continued to refine their methods for credential abuse, the placement of honeytokens and service principals became even more critical for early detection. Organizations that invested in these preemptive controls were better positioned to navigate the complexities of modern digital infrastructure while maintaining a high level of security. The lesson learned from these implementations was that the most effective defense is one that actively engages the intruder, turning their own tactics into a source of intelligence for the defender. By continuing to evolve these strategies and integrating them into a holistic security framework, enterprises built a durable and effective barrier against even the most determined adversaries. The journey toward a more resilient future was defined by the willingness to adopt these advanced technologies and the commitment to operational excellence in their day-to-day management.