Data Security
In an environment where cybersecurity defenses are increasingly reliant on automated pattern recognition and signature-based scanning, the emergence of the DEEP#DOOR framework represents a sophisticated pivot toward stealth and surgical precision. This Python-based remote access trojan, recently identified by researchers, operates with a level of
The silent proliferation of autonomous artificial intelligence agents across global enterprises has created a massive security vacuum that traditional identity management systems simply cannot monitor or control effectively. As the digital landscape undergoes this rapid metamorphosis, the traditional concept of identity is being stretched to its
The rapid evolution of frontier artificial intelligence has forced a dramatic confrontation between the pursuit of absolute technological dominance and the non-negotiable requirements of modern national defense. This tension is best illustrated by the White House’s transition away from the Biden-era Executive Order 14110, which prioritized a broad
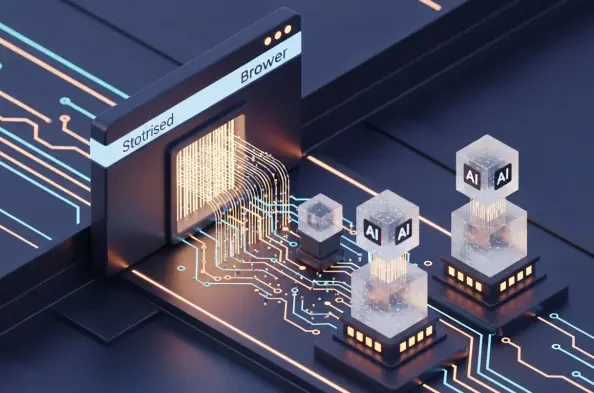
The Dawn of Autonomous Productivity and Its Security Implications The current transition from reactive web interfaces to autonomous digital agents represents one of the most profound reorganizations of corporate software architecture since the initial migration to the cloud. This evolution has birthed a new class of web navigation tools known as
The traditional phone call from a bank’s fraud department asking if a customer really just purchased a luxury watch in another country has become a relic of a less sophisticated digital era. Financial security has undergone a massive transformation that favors invisible, fluid protection over the rigid protocols that previously inconvenienced