Data Security
While the tech world fixated on the public debuts of large language models, a parallel revolution in cloud infrastructure quietly amassed a staggering 205% year-over-year growth, reshaping the very foundation of artificial intelligence development. This explosion gave rise to a new class of specialized providers, dubbed "neoclouds," which have
Navigating the complexities of the modern tech labor market requires a sharp, data-driven perspective. To make sense of the conflicting signals—from sector-wide job cuts to falling unemployment rates—we sat down with Vernon Yai. As a data protection and governance expert, Vernon brings a unique lens to hiring trends, focusing on how risk
The contemporary digital ecosystem is teetering on a precarious edge, where the relentless persistence of established cyber threats like state-sponsored espionage and sophisticated ransomware campaigns is dangerously intersecting with the operational fragilities introduced by a new wave of technological innovation. This convergence is creating a
We're joined today by Vernon Yai, a renowned data protection expert whose work in privacy and data governance has made him a leading voice on risk management and safeguarding sensitive information. We'll be diving into California's recent crackdown on data brokers, exploring the profound risks of trading personal health data, the mechanics of
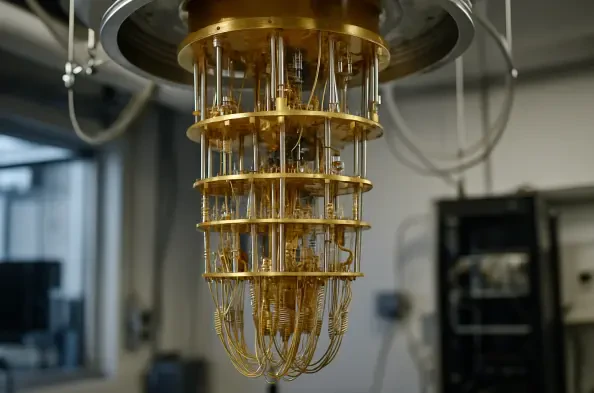
The impending arrival of fault-tolerant quantum computers represents less of a technological ripple and more of a seismic shockwave poised to shatter the foundations of modern digital security, rendering today's encryption standards obsolete. While the race to develop new, quantum-resistant algorithms is a critical technical endeavor, a recent