Data Security
Vernon Yai is a distinguished authority in data governance and privacy, renowned for his work in safeguarding sensitive information within rapidly evolving digital landscapes. With a background rooted in risk management and the creation of sophisticated detection systems, he has become a go-to expert for companies navigating the complexities of
The transition from classical mathematical complexity to the immutable laws of physics marks the most significant shift in secure communications since the invention of the public key. Unlike traditional encryption, which relies on the assumption that certain mathematical problems are too difficult for current computers to solve, Quantum Key
The discovery of the Miasma campaign has sent ripples through the devsecops community, revealing how even the most robust enterprise ecosystems can fall prey to the silent infiltration of supply chain poisoning. This roundup examines the technical nuances of the breach that targeted Red Hat npm packages, drawing from industry observations to
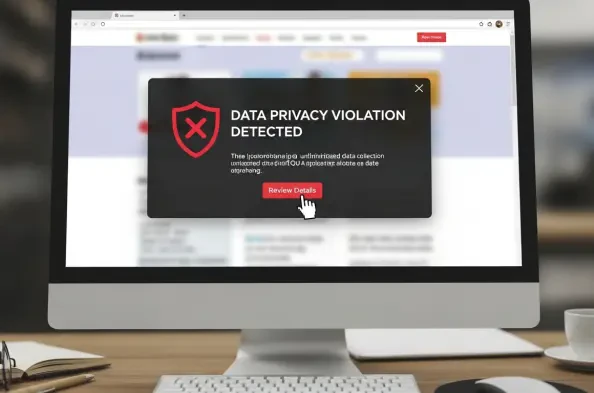
The sophisticated nature of cyberattacks in the current landscape demonstrates that simply collecting data is no longer a viable strategy for maintaining organizational integrity against persistent digital threats. Security teams often find themselves swimming in a vast ocean of telemetry, where every endpoint generates thousands of events, yet
The disconnect between the Energy Commission of Nigeria’s ambitious strategic mandates and its visible digital presence has become a focal point of criticism among industry analysts and international energy investors. While the commission is tasked with the vital responsibility of planning and coordinating national policies, its online