Data Security
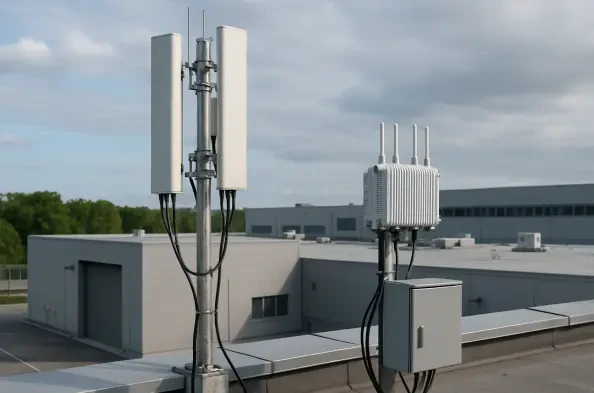
The unceasing global demand for faster, more reliable, and ubiquitous digital connectivity has continually challenged the limits of existing wireless infrastructure, creating a pressing need for a transformative leap forward. A recent U.S. breakthrough in 5G+ Massive MIMO (Multiple-Input Multiple-Output) technology now stands as a pivotal
The seamless integration of cloud storage into modern operating systems has become a cornerstone of productivity, yet this convenience has introduced a new and formidable attack surface, as evidenced by a recently disclosed zero-day vulnerability. A critical flaw within a core Windows component responsible for managing cloud files is being
In the intricate ecosystem of cloud computing, the tools that operate silently in the background often carry the most significant weight, and a new report reveals how vulnerabilities in one such tool can unravel the security of entire digital infrastructures. A cluster of five interconnected vulnerabilities discovered in Fluent Bit, a ubiquitous
As AI reshapes the enterprise landscape, no role is undergoing a more profound transformation than that of the CIO. Vernon Yai, a leading expert in data protection and privacy governance, joins us to dissect this evolution. With a deep focus on risk management and safeguarding sensitive information, he offers a unique perspective on the challenges
Imagine a world where cyber threats evolve faster than the human mind can track, where a single vulnerability in a cloud system could cost millions in damages before anyone even notices the breach. This is the reality facing organizations today as they navigate increasingly complex hybrid and multi-cloud environments. At the latest AWS re:Invent