Data Security
Imagine a digital landscape where data flows at speeds and capacities once thought to be the stuff of science fiction, fundamentally altering how industries and societies operate in profound ways. This is the tantalizing vision offered by Spatiotemporal Topological Combs (ST-Combs), a groundbreaking technology unveiled in a pivotal article on
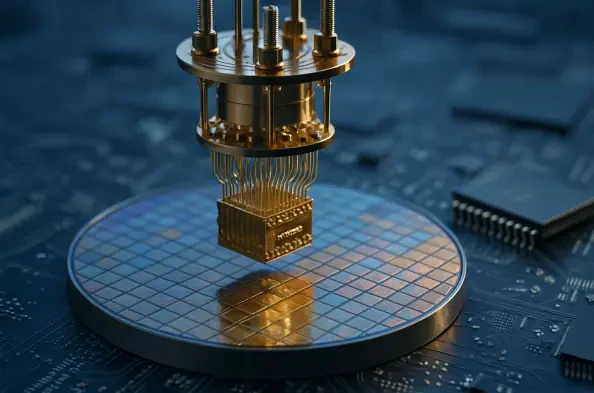
The convergence of quantum computing and semiconductor technology stands as a monumental leap forward, fundamentally altering the trajectory of computational power and artificial intelligence (AI) in ways that challenge the imagination. As of October 2025, this fusion is not merely a theoretical concept but a dynamic force driving innovation
Ransomware attacks have escalated into a global crisis, with corporations facing unprecedented threats to their data and operations, as demonstrated by the recent breach of Asahi Group. On October 7, the notorious Qilin ransomware gang claimed responsibility for a major cyberattack targeting Asahi Group, a leading Japanese beverage and food giant.
I'm thrilled to sit down with Vernon Yai, a renowned data protection expert with a wealth of experience in privacy protection and data governance. With a career dedicated to risk management and pioneering detection and prevention techniques, Vernon has become a trusted voice in safeguarding sensitive information. In this conversation, we dive into
In an era where cyber threats are becoming increasingly sophisticated, enterprises face unprecedented challenges in safeguarding their digital assets from breaches that can compromise sensitive data and disrupt operations. Traditional passwords, long a staple of authentication, have proven to be a weak link, easily exploited through phishing,