The rapid acceleration of quantum hardware has long been cited as the ultimate Achilles’ heel for decentralized financial networks, yet recent industry analysis suggests the threat is far more manageable than the doom-laden headlines often imply. This shift in perspective comes as analysts from firms like Bernstein categorize the quantum transition not as an existential crisis, but as a medium-term system upgrade cycle. While a theoretical quantum machine capable of breaking Bitcoin’s security remains several years away, the window for preparation is narrowing, with current estimates placing a significant technological threshold about three to five years into the future. By moving beyond the initial panic, stakeholders are beginning to understand that the protocol’s survival depends on a disciplined migration rather than a radical redesign. This realization is reshaping how developers prioritize security updates, focusing on the specific areas where quantum advantage poses a genuine risk while acknowledging the parts of the network that remain fundamentally robust against even the most advanced qubits.
Structural Vulnerabilities and the Quantum Advantage
The Cryptographic Breaking Point
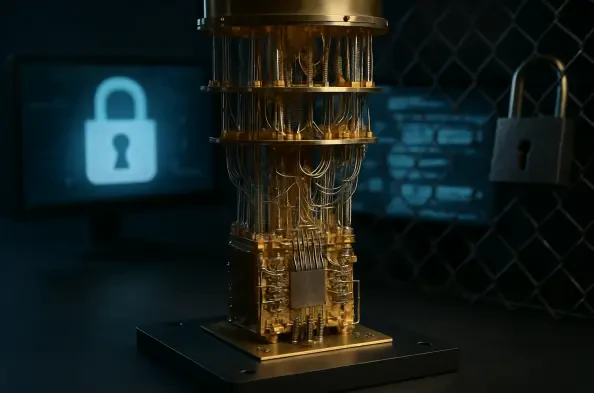
The fundamental risk inherent in the rise of quantum computing stems from the profound operational differences between classical binary machines and quantum systems utilizing qubits. Unlike classical computers that process information in bits as either a zero or a one, quantum machines leverage superposition and entanglement to exist in multiple states simultaneously, allowing for the execution of complex mathematical functions at unprecedented speeds. For the cryptocurrency sector, the primary concern remains Shor’s algorithm, a mathematical process specifically designed to find the prime factors of large integers, which could effectively break the Elliptic Curve Cryptography currently used to secure Bitcoin wallet signatures. Recent research from major players like Google Quantum AI indicates that a system possessing approximately 500,000 stable qubits could potentially crack a signature in less than fifteen minutes. While current hardware has not yet reached this scale, the trajectory of development suggests that the industry must treat this timeline as a definitive deadline for protocol updates.
This specific vulnerability is centered on the way public keys are handled within the blockchain ecosystem, particularly during the moment a transaction is broadcast to the network. Under the current Bitcoin architecture, the public key is not revealed until the owner signs a transaction to spend the funds; prior to that, the funds are protected by a hash of the public key, which is considered quantum-resistant. However, the brief window between the broadcast of a transaction and its inclusion in a block provides a potential opening for a quantum adversary to intercept the signature, derive the private key, and attempt to redirect the funds to a different address. This “front-running” attack represents the most immediate threat to active users once quantum hardware reaches sufficient maturity. Consequently, the development of faster block times or more immediate finality has been discussed as a temporary buffer, though the long-term solution necessitates a complete transition to new cryptographic primitives that do not rely on the mathematical problems quantum computers are designed to solve.
Maintaining the Integrity of Mining
In stark contrast to the vulnerabilities found in digital signatures, the underlying hashing process used in Bitcoin mining is significantly more resilient to the advancements of quantum computation. Mining relies on the SHA-256 algorithm, which is a symmetric cryptographic function that behaves differently than the asymmetric elliptic curve schemes used for wallets. While Grover’s algorithm provides a quantum speedup for searching unsorted databases and could theoretically be applied to mining, the advantage it offers is merely quadratic rather than exponential. This means that a quantum computer would not be able to instantly solve blocks; instead, it would effectively act as a more efficient specialized hardware miner. Experts suggest that the SHA-256 standard is likely to remain secure for millions of years because the energy requirements and physical constraints of quantum systems do not provide the same overwhelming advantage in hashing as they do in factoring. This distinction is crucial because it ensures the security of the network’s history and issuance remains intact.
The impact of quantum miners on the network’s difficulty adjustment mechanism would mirror the historical transition from CPUs to ASICs that the industry witnessed in the early years of the previous decade. If a quantum-enhanced miner were to join the network, the protocol would naturally respond by increasing the difficulty of the mathematical puzzles, thereby maintaining the ten-minute block production target. This self-correcting feature prevents any single entity from monopolizing the hash rate through superior technology, provided that the distribution of quantum hardware eventually becomes as decentralized as the current generation of silicon miners. Furthermore, because hashing is less susceptible to quantum attacks, the massive cumulative energy spent securing the chain since its inception acts as a permanent barrier. An attacker would still need to amass more computational power than the rest of the network combined to rewrite history, a task that remains economically and physically prohibitive regardless of whether the hardware utilizes classical bits or quantum bits.
Proactive Migration and Network Evolution
Securing Legacy Digital Assets
While the protocol itself can be upgraded, the most concentrated risk remains within the millions of Bitcoin stored in legacy addresses that were created during the network’s early development. Approximately 1.7 million BTC currently resides in Pay-to-Public-Key formats, which, unlike modern address types, reveal the public key directly on the blockchain without an additional layer of hashing. This exposure makes these dormant coins prime targets for what security researchers call “harvest now, decrypt later” strategies. In this scenario, an adversary could collect the encrypted data today and store it until quantum technology matures enough to break the encryption years from now. Since many of these addresses are associated with the earliest miners or lost keys, they cannot easily be moved by their original owners to more secure, quantum-resistant formats. This creates a unique situation where a significant portion of the total supply—estimated between 20% and 50%—could eventually become vulnerable to theft if no protocol-level intervention is implemented to protect these assets.
The challenge of migrating these legacy assets is compounded by the core tenet of decentralization, which generally discourages forceful intervention in user balances or the freezing of specific addresses. However, as the quantum threat approaches, the community may have to consider a “soft fork” that implements a deadline for moving funds into quantum-secure wallets. Under such a proposal, any funds remaining in legacy formats after a certain date would essentially become unspendable or would require a proof-of-burn process to be reissued in a new format. This debate highlights the tension between maintaining the immutability of the ledger and ensuring the long-term solvency of the network. If hundreds of billions of dollars in Bitcoin were suddenly liquidated by a quantum-equipped attacker, the market impact would be catastrophic. Therefore, the migration of legacy assets is viewed as a critical security priority for custodians and long-term holders who must prioritize moving their holdings to modern formats like Taproot, which provide a better foundation for future quantum upgrades.
Implementation of Post-Quantum Standards
The Bitcoin development community is already laying the groundwork for a transition to post-quantum cryptography through proposals such as BIP360, which aims to introduce alternative signature schemes. One of the primary candidates for this upgrade includes lattice-based cryptography, which is believed to be resistant to Shor’s algorithm because it relies on mathematical problems that remain difficult for both classical and quantum machines to solve. Implementing these new standards will likely involve the introduction of Winternitz or Lamport signatures, which are characterized by their “one-time” use nature and significantly larger data sizes compared to current signatures. The technical trade-off involves a substantial increase in the amount of data required for each transaction, which could lead to higher fees and increased storage requirements for node operators. Despite these costs, the consensus among core contributors is that the preservation of the network’s integrity outweighs the inconvenience of larger transaction sizes, leading to a deliberate and methodical testing phase.
Preparation for the post-quantum era is not limited to Bitcoin; it has become a coordinated effort across the entire technological landscape, with the Ethereum Foundation and Google setting internal targets for 2029 to achieve quantum readiness. This alignment across the tech industry provides a shared framework for developing, testing, and auditing new cryptographic libraries that can be integrated into blockchain protocols. Blockstream CEO Adam Back has emphasized that the current state of quantum computing is still in its infancy, with existing machines only capable of performing extremely basic calculations that pose no immediate threat to modern encryption. This perspective provides a grounded reality check, suggesting that the industry has a clear window of time to perfect its migration strategies. By observing how other major infrastructures adapt, Bitcoin developers can select the most efficient and battle-tested solutions, ensuring that when the switch to post-quantum standards finally occurs, it is as seamless as previous major upgrades like the activation of SegWit.
Actionable Paths Toward Long-Term Resilience
The transition to a post-quantum era was eventually viewed as a manageable evolution of the protocol rather than a terminal event. Industry leaders successfully identified that the threat was neither novel nor immediate, allowing for a disciplined upgrade of wallet standards and encryption methods. The priority remained the timely migration of legacy assets and the implementation of quantum-resistant signatures within the necessary five-year window. Custodians and long-term holders took proactive steps to rotate their keys, which significantly mitigated the risk of future decryption attacks. Developers integrated new cryptographic libraries that balanced security with network efficiency, proving that the decentralized nature of the project was an asset in adapting to technological shifts. Ultimately, the stability of the network depended on the execution of these security upgrades, which ensured that the fundamental value proposition of the digital asset remained intact even as hardware capabilities advanced. By treating the quantum challenge as a standard technical hurdle, the community reinforced the long-term viability of the ecosystem.