Data breaches represent a growing financial threat, with the global average cost per incident exceeding $4.88 million in 2024. That figure continues to increase as hackers exploit blind spots and employees unintentionally widen them. As data moves through cloud apps, vendor systems, and unmanaged devices, assuming it’s safe in one place creates more vulnerabilities. The implications are clear: sensitive information leaks lead to costly recovery efforts. But what can businesses do to reduce risk without disrupting business processes? This article outlines ways to leverage data protection to mitigate these growing risks.
The Evolution of Information Security and Risk Management
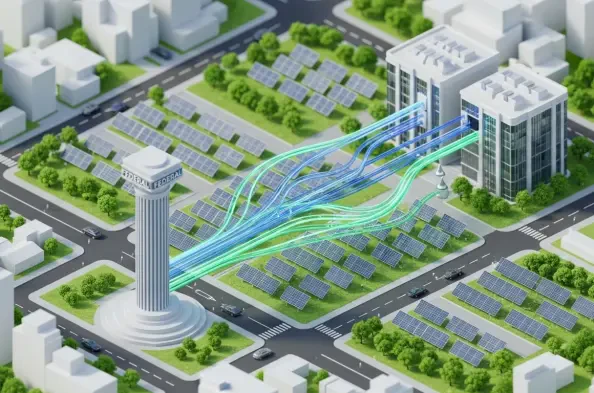
Traditional security models assumed trust based on network location, but the modern work environment requires a data-centered approach. Today’s method focuses on the details by analyzing context and enforcing protection policies based on data sensitivity, user intent, and business needs. This zero-trust approach enables more precise control, answering key questions such as: What is the data, who is accessing it, and why?
Deep content inspection detects specific patterns, like source code or financial data, while contextual analysis looks at user behavior, device status, and unusual data transfers. By comparing behavior against a baseline, the zero trust system can identify anomalies, such as an employee who usually accesses 10 files a day suddenly downloading thousands of customer records. In such cases, policies can require a business justification, quarantine data, or automatically apply encryption. These safeguards ensure legitimate work continues while preventing incidents like fraud or data theft.
Proactively mitigating risk is important because the direct consequences of data compromises include forensic costs, legal liabilities, customer notifications, and fines. Even more concerning are the indirect losses, such as missed opportunities, customer attrition, and weakened business negotiations. This situation worsens when trade secrets or sensitive data are compromised. Since human factors play a big role in breaches, contributing to about three-quarters of incidents (errors or data misuse), an effective data protection program is essential to help minimize risks. Training staff can also make errors less damaging and malicious actions more noticeable and short-lived.
In this evolved data environment, insider risk deserves special attention. Most incidents aren’t malicious; they’re caused by misdirected emails, unsecured cloud storage, or contractors saving sensitive data to personal devices. To manage these risks, precision controls are crucial in preventing such errors from leading to breaches. Simultaneously, the security program must be able to detect malicious intent. Indicators such as rapid downloads, data being moved to hidden locations, and changes in file type signal potential threats. By implementing clear policies and maintaining consistent enforcement, organizations can guide employees in managing sensitive information, thereby reducing the risk to the company.
Some organizations might see strict controls as barriers rather than essential protections, creating tension between keeping data safe and staying productive. A good security program addresses this tension by providing strong protection that doesn’t restrict internal movement while allowing business continuity without increased risk. To boost data security, organizations need a strategic plan that includes solid protective steps at every level.
Build a Strong Data Protection Framework
Effective data protection starts with mapping out where sensitive information is created, stored, and shared. This process includes clearly classifying data and associating each category with specific business obligations and controls, recognizing that not all data is equally important and that different channels carry varying risks. As a result, rules will need to be tailored for each context, whether it’s email, web uploads, collaboration platforms, developer repositories, or data pipelines. By focusing on fewer, well-designed policies that reflect real business needs, organizations can achieve far better productivity and security outcomes than with a disorganized, sprawling set of rules.
This data protection must cover endpoints, networks, cloud services, and approved business apps to ensure comprehensive security. Endpoint controls safeguard data in use, effectively preventing unauthorized transfers and the use of unsanctioned tools. Meanwhile, network controls enhance security by protecting data in motion, allowing for inspection and policy enforcement for web and email traffic.
To further complement these measures, cloud-native controls apply API-level monitoring and remediation within productivity suites and file-sharing platforms. By integrating these layers, organizations can minimize security gaps and reduce overlap, creating a more robust and cohesive protection strategy. A strong security foundation also helps with ensuring that their security measures align with regulatory standards and encourage best practices.
Prioritize Compliance in Security Management
Security management involves assigning clear policy governance responsibilities, having a formal exception process, and regularly reviewing high-risk rules. Each policy should target measurable outcomes, like reducing unencrypted external data sharing or decreasing containment times. Using security AI and automation has proven to reduce breach costs by 1.88 million and improve containment efficiency, which plays a crucial role in compliance.
Businesses can make the mistake of treating compliance as a checkbox exercise rather than integrating it as a strategic asset. This leads to inflexible processes that meet regulatory requirements on paper but fail to address real-world security needs. Organizations often implement standard, one-size-fits-all policies that don’t reflect their unique operational context. As a result, they miss out on leveraging compliance as a tool for driving meaningful security improvements.
While regulations shape the focus of security programs, relying only on compliance can lead to rigid, checkbox-driven processes. Instead, businesses should link compliance efforts to practical policies, backed by solid evidence and thorough reporting. Keep detailed logs of data access and use, and enable automated audit trails to spot any deviations quickly. Policies need to be flexible enough to adapt as business directions change, with governance that keeps pace through well-documented updates. This proactive approach ensures that as companies grow and change, their data protection strategies stay resilient and effective.
Future-Proof the Enterprise with Proactive Measures for Data Integrity
As data volumes and channels expand, relying solely on manual review processes becomes impractical. Automation and analytics have transformed data protection from a reactive approach to real-time management. Organizations that invest in real-time detection and automated containment can handle the complexity of data environments without slowing the business. Industry reporting shows that organizations with mature automation shorten detection and containment times, which correlates with lower breach costs and smaller data-loss events. In practice, this looks like proactive measures that adapt based on observed behavior, guardrails that travel with files, and playbooks that route only the highest-risk events to analysts.
As modern threats increasingly focus on data theft rather than traditional ransomware, security priorities must shift accordingly. While backup and recovery remain crucial, the emphasis now is on preventing data exfiltration, reducing the value of any stolen data, and demonstrating control to regulators and customers. Techniques such as tokenizing payment data, encrypting sensitive fields with format-preserving encryption, and watermarking valuable documents make stolen data less useful; here’s why:
Tokenization: Replaces sensitive values, such as card numbers, with unique tokens, so stolen data is meaningless without the token vault.
Format-preserving encryption: Encrypts sensitive fields while keeping the same data format, so systems can process it, but attackers can’t read it without the key.
Watermarking: Embeds identifiable markers in documents, making leaks traceable and discouraging unauthorized sharing.
These tactics, combined with strong monitoring of data management and verified supplier controls, can help businesses mitigate the risk and impact of data loss.
However, these advancements come with trade-offs. Enhanced controls can introduce friction or require new skills, and endpoint inspection may raise privacy concerns in some jurisdictions, requiring clearly stated duties, transparent policies, and data minimization. For cloud API integrations, organizations may need engineering resources to align labels, identities, and access paths. Budget constraints will demand that businesses focus on meaningful metrics and targeted controls over broad restrictions.
Strategically Focus on Security Metrics and Outcomes
Executives don’t need more apps or features to enhance security. Instead, they need proof that their data protection program effectively reduces risks at a reasonable cost and speed. The best programs focus on a few key metrics that align with business goals, such as:
Mean time to detect and contain suspected exfiltration events, segmented by channel
False positive rate for high-severity policies after tuning, with trend lines
Percentage of sensitive data correctly classified and labeled in top repositories
Volume of sensitive data sent to unauthorized destinations monthly
Coverage of high-risk data channels by control type, with documented gaps and plans
Data loss prevention works best when treated as an ongoing operating capability rather than a one-time rollout. It should evolve as products change, suppliers shift, and regulations tighten. That means regular attack simulations, periodic policy reviews with business owners, and an intake process that quickly onboards new applications and partners. It also means investing in human capacity. Targeted training tied to real incidents outperforms generic awareness campaigns. When employees see that policies protect customer trust and revenue, not just compliance checklists, adoption improves.
The goal is not perfect control. It is informed, defensible risk-taking. Businesses that view data protection as a design constraint, just as they treat safety in manufacturing or quality in software, will keep their advantage. They build for safe collaboration from the start, assume failure at the edges, and instrument the system so that the worst day is containable and explainable.
Conclusion
As complexity increases and attackers become more sophisticated, the risks to data integrity continue to grow. To effectively mitigate these threats, organizations must embrace a disciplined, data-driven approach. This involves focusing on critical metrics and adapting quickly to new challenges.
The decision for leaders is clear: prioritize investing in a robust data protection strategy or risk facing escalating breaches and their costly consequences. Ignoring the need for comprehensive security measures could result in severe financial and reputational damage. Commit to a proactive, adaptive security framework that can deal with the complexities of modern threats and tackle unchecked vulnerabilities as you scale. Will your organization embrace strategic data protection measures today?