The rapid evolution of generative artificial intelligence and automated exploitation tools has fundamentally altered the way individuals and organizations perceive digital security in the current landscape of 2026. Gone are the days when a system infection was heralded by an obvious performance lag or a glaringly suspicious pop-up window. Instead, modern cyberattacks have transitioned into a state of near-total invisibility, where malicious code can reside within a system for weeks or months without triggering traditional alarms. The current digital environment is characterized by an arms race between cybercriminals using sophisticated machine learning to find vulnerabilities and security developers using similar technology to patch them. This high-stakes environment has moved beyond the simple “virus” of the past, evolving into a complex web of multifaceted threats that target personal identity, financial assets, and sensitive corporate data simultaneously. Consequently, the reliance on robust, real-time security measures is no longer a matter of technical preference but a foundational requirement for any device connected to the global network.
The Evolution of Digital Warfare and AI Threats
The sophistication of social engineering in 2026 has reached a point where traditional skepticism is often insufficient to protect the average user from a well-crafted attack. Cybercriminals now leverage advanced language models to generate phishing communications that perfectly mimic the tone, vocabulary, and formatting of legitimate institutions, making it nearly impossible to distinguish a fraudulent email from a real one through visual inspection alone. These AI-driven campaigns are not limited to email; they extend to deepfake audio and video used in “vishing” and “smishing” attacks that can trick even the most tech-savvy professionals. Because these threats are designed to bypass the human element of security, the role of antivirus software has shifted from being a reactive scanner to a proactive interceptor. Modern security suites now analyze the metadata and origin of communications in real-time, identifying subtle discrepancies that indicate a fraudulent source before the user even has a chance to interact with the malicious content.
Beyond the visible layers of interaction, malware developers are now deploying “living-off-the-land” techniques that utilize legitimate system tools to carry out malicious activities, effectively blending in with normal operating system processes. These silent threats often involve fileless malware that resides entirely in a computer’s random-access memory, leaving no physical footprint on the hard drive for traditional scanners to find. Once embedded, these programs can exfiltrate data, monitor keystrokes, or act as a gateway for more destructive payloads like ransomware. In 2026, the complexity of these operations means that an unprotected system is essentially an open door for automated scripts that scan the internet for vulnerable IP addresses. Dedicated security software provides the necessary oversight by monitoring system memory and process behavior, ensuring that even if a threat bypasses the initial perimeter, its subsequent actions are identified and halted before significant damage can occur.
Core Mechanics: Signature Detection and Heuristic Analysis
Antivirus technology in the current year continues to rely on the established foundation of signature-based detection, albeit at a scale and speed that was previously unimaginable. This methodology involves maintaining a vast, cloud-based repository of digital fingerprints—unique identifiers for every known piece of malicious code discovered across the globe. When a file is downloaded or an application is launched, the security software instantly compares its signature against this global database. However, because contemporary malware often utilizes polymorphism to change its own code with every new infection, the database must be updated every few seconds rather than daily or weekly. This real-time synchronization ensures that as soon as a new threat is identified in one part of the world, every other protected device is immediately immunized against it. This collective defense mechanism forms a critical barrier against the rapid spread of global malware outbreaks that would otherwise overwhelm individual systems.
While signature detection handles known threats, heuristic analysis has become the primary tool for identifying “zero-day” vulnerabilities that have never been seen before. This approach does not look for a specific file match but instead examines the underlying behavior and structural patterns of a program to determine its intent. If an application suddenly attempts to encrypt a large volume of files or requests unauthorized access to the system registry, the heuristic engine flags it as suspicious regardless of its lack of a known malware signature. In 2026, these engines are increasingly powered by local neural networks that can differentiate between the legitimate operations of a professional video editor and the malicious encryption processes of a ransomware variant. By simulating the execution of suspicious files in a secure, isolated “sandbox” environment, the software can observe the potential impact of a program without risking the integrity of the host system, providing a layer of safety that is essential for exploring the modern internet.
Navigating the Spectrum of Modern Malware
The threat of ransomware continues to be a dominant concern for both private individuals and large-scale enterprises in 2026, as the “Ransomware-as-a-Service” model has lowered the barrier to entry for digital extortion. Modern ransomware variants no longer just lock files; they often involve “triple extortion,” where attackers encrypt data, steal a copy to threaten public release, and launch distributed denial-of-service attacks against the victim’s network. This multifaceted pressure makes recovery incredibly difficult without the aid of specialized security modules designed to block unauthorized encryption in real-time. Antivirus suites now include dedicated “anti-ransomware” shields that automatically create hidden, immutable backups of critical files the moment a suspicious process is detected. This ensures that even if a new strain of ransomware manages to bypass initial detection, the user can restore their data without paying a ransom, effectively neutralizing the financial incentive for the attackers.
In addition to high-profile ransomware, the current digital landscape is plagued by an increase in spyware and “stalkerware” that operates with the specific intent of violating personal privacy. These programs are often designed to be completely invisible, hiding deep within system directories while they record audio from microphones, capture video from webcams, and track geographical movements through GPS data. Many users unknowingly install these tools through compromised “free” software or malicious browser extensions that appear helpful on the surface. Standalone security software is specifically tuned to recognize the intrusive behaviors associated with these programs, providing alerts when an unauthorized application attempts to access hardware peripherals or transmit data to a suspicious remote server. By maintaining a strict policy on data privacy and application permissions, modern antivirus tools act as a vital safeguard against the erosion of personal autonomy in an increasingly connected and monitored world.
Integrated Security Suites: Beyond Simple Scanning
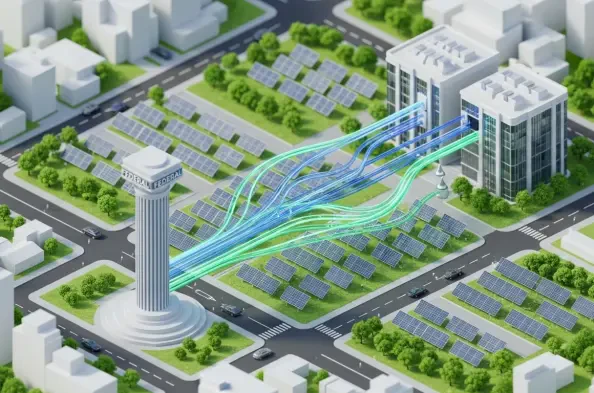
The transition of antivirus products into comprehensive security hubs has reached a new peak in 2026, with most premium suites offering a unified platform for managing all aspects of a user’s digital footprint. No longer limited to just scanning for viruses, these programs now include sophisticated integrated firewalls that manage both inbound and outbound network traffic with granular precision. These firewalls are essential for preventing “lateral movement,” a technique where an attacker who has compromised one device on a home or office network attempts to jump to other connected systems. By monitoring every connection request and comparing it against a list of known safe behaviors, the security suite can isolate a single infected device and prevent a localized incident from becoming a network-wide catastrophe. This level of network-aware protection is a significant upgrade over the basic firewalls typically included in standard operating systems.
Privacy enhancement has also become a standard feature in modern security packages, with many vendors bundling high-speed Virtual Private Networks directly into their interfaces. In 2026, the use of a VPN is a critical necessity for anyone using public Wi-Fi hotspots, which remain a primary target for “man-in-the-middle” attacks where hackers intercept data as it travels between a device and the router. By encrypting the entire data stream and masking the user’s IP address, these integrated VPNs ensure that sensitive activities like online banking or private messaging remain confidential. Furthermore, many suites now include specialized “safe browser” modes that launch a hardened, isolated environment for financial transactions. These environments block all external plugins, disable screen-capture capabilities, and verify the SSL certificates of banking websites with extreme rigor to ensure that credentials cannot be stolen by keyloggers or fraudulent “look-alike” domains that have become increasingly common.
Evaluating the Efficacy of Built-in Protection
A significant portion of the ongoing debate regarding digital security in 2026 centers on whether the built-in protections of major operating systems are sufficient for the average user. Platforms like Microsoft Windows and MacOS have invested heavily in their native security tools, such as Microsoft Defender and XProtect, which provide a respectable baseline of protection for the vast majority of common threats. These tools have the advantage of being deeply integrated into the system kernel, which allows them to operate with very low overhead and a minimal impact on system performance. For a user who strictly adheres to safe browsing habits—such as avoiding pirated software, using unique and complex passwords, and never clicking on unsolicited links—these built-in features can indeed provide an adequate shield against the most frequent automated attacks encountered during daily internet use.
However, the argument for standalone, third-party antivirus software remains compelling because of the specialized depth and rapid response times these independent companies provide. While a massive corporation like Microsoft must manage a global ecosystem of products, a dedicated cybersecurity firm focuses entirely on threat intelligence and rapid mitigation. This focus often translates to faster update cycles for malware definitions and more aggressive implementations of experimental heuristic technologies that can catch emerging threats hours or days before they are integrated into OS-level tools. Moreover, standalone suites offer a level of cross-platform consistency that is vital in an era where users move seamlessly between PCs, tablets, and smartphones. By using a single security provider across all devices, users can maintain a synchronized defense posture, ensuring that a vulnerability discovered on a mobile device is immediately addressed on the desktop as well.
Strategic Defensive Practices for the Modern User
Maintaining a secure posture in the current digital landscape requires a holistic approach that combines sophisticated software with disciplined user behavior and proactive management. No security program, regardless of its technical complexity, can be considered a “silver bullet” that offers 100% protection against every possible contingency. Human error remains one of the most significant variables in the security equation, particularly when it comes to social engineering attacks that bypass technical filters by appealing to the user’s emotions or sense of urgency. Therefore, users must cultivate a healthy skepticism toward all unsolicited digital interactions and verify the identity of senders through secondary channels before sharing sensitive information or clicking on attachments. This combination of “human-ware” and software-ware forms the most effective defense against the highly targeted attacks that have become a hallmark of the current year.
Beyond active monitoring, the implementation of a robust data redundancy strategy is perhaps the most important secondary line of defense against catastrophic data loss. Even with the best antivirus protection, the risk of a hardware failure or a particularly aggressive ransomware infection remains, making regular backups an non-negotiable part of digital life in 2026. Experts recommend a multi-tiered backup approach that includes both a local, physical drive for quick restoration and a secure, encrypted cloud service for off-site protection. This ensures that even if a physical disaster or a complete system compromise occurs, the most critical data can be recovered without yielding to the demands of cybercriminals. When these technical measures are paired with the consistent use of multi-factor authentication and the regular auditing of app permissions, the user creates a “defense-in-depth” architecture that is resilient enough to withstand the ever-evolving challenges of the modern digital world.
The landscape of digital security was shaped by the constant tension between rapid technological innovation and the persistent ingenuity of malicious actors throughout the current year. It was demonstrated that while the core principles of antivirus software remained consistent, the methods of delivery and the breadth of protection expanded significantly to meet the challenges of an AI-driven threat environment. The necessity of these tools was underscored by the increasing frequency of invisible, fileless malware and highly personalized phishing campaigns that targeted unsuspecting individuals and organizations alike. As the year progressed, the distinction between simple malware protection and comprehensive identity management became increasingly blurred, leading to the rise of all-in-one security suites that safeguarded every aspect of a user’s digital life. Moving forward, the integration of hardware-level security and behavioral biometrics will likely become the next frontier in the ongoing effort to secure our global digital infrastructure. Users were reminded that staying safe required a proactive mindset, where the installation of high-quality security software served as the first step in a broader commitment to digital hygiene and vigilant awareness.