Cloud Security
In the current digital landscape where data breaches occur with surgical precision, relying solely on the security protocols of third-party cloud providers has become a precarious gamble for both individuals and enterprises alike. While modern platforms have implemented robust infrastructure, they still represent centralized targets that attract
The landscape of digital threats has shifted from simple, destructive viruses to complex, multi-stage social engineering campaigns that target the person behind the keyboard rather than the software inside the machine. For many Windows users, the built-in protection of Microsoft Defender feels like a convenient and cost-free solution to
The staggering reality for the modern digital enterprise is that while data serves as the foundational fuel for innovation and competitive edge, it has simultaneously transformed into the single most complex and volatile liability within the global security landscape. As organizations navigate the intricate architectures of hybrid clouds,
The modern digital landscape is no longer a place where traditional firewall barriers and simple antivirus signatures can offer even a modicum of guaranteed protection against sophisticated threats. In an era where attackers deploy automated scripts and generative algorithms to probe for vulnerabilities at machine speed, the reliance on
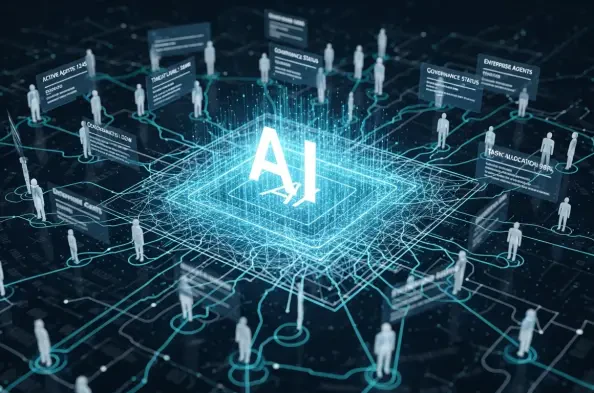
Every single second, millions of digital interactions occur within a global enterprise without a single human finger touching a keyboard or a single pair of eyes viewing a screen. This invisible workforce has quietly expanded to the point where non-human identities, such as service accounts, API keys, and OAuth tokens, now outnumber human