Cloud Security
The traditional grocery landscape is undergoing a radical metamorphosis as data-driven intelligence shifts from a supportive function to the primary engine of corporate strategy. Kroger has taken a definitive step toward this future by establishing the new role of Chief Data and AI Officer, a move that signals a comprehensive pivot toward a
The sudden proliferation of autonomous artificial intelligence agents across corporate networks has fundamentally altered the baseline of digital operations, turning what were once static analytical tools into independent decision-makers. While initial iterations of AI focused on passive observation and defensive monitoring, the current generation
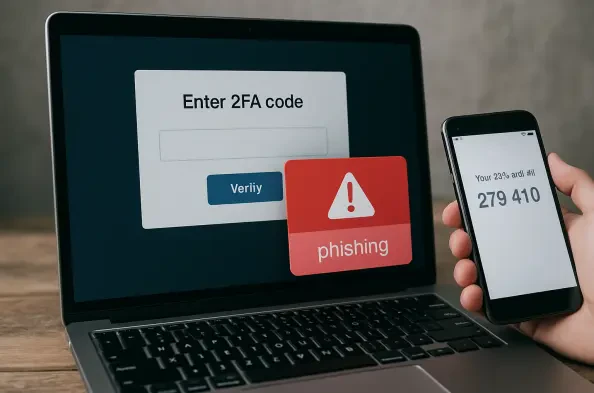
The illusion of absolute security provided by multi-factor authentication has been shattered by the realization that even the most robust digital locks can be picked if the burglar controls the hallway. As organizations increasingly leaned on secondary verification to defend their perimeters, a sophisticated adversary emerged to exploit the very
The rapid migration of sophisticated threat actors from the dark web to mainstream messaging platforms has redefined the modern cybersecurity landscape, turning instant communication tools into weaponized environments. What once served as a simple encrypted chat application has morphed into a sprawling, multi-layered marketplace where the barrier
The rapid metamorphosis of the enterprise digital landscape has fundamentally rewritten the rules of engagement for cybersecurity professionals who must now defend a perimeter that effectively no longer exists in a traditional sense. In this current environment, the definition of an endpoint has expanded far beyond the isolated laptops or mobile