Cloud Security
Imagine a corporate environment where every click, every download, and every web interaction could potentially open the door to a devastating cyberattack, making browser security more critical than ever. With browsers now serving as the primary gateway for enterprise workflows, the stakes have never been higher. As cloud-based applications
What if the AI assistant handling your company’s most sensitive data suddenly turned traitor, leaking secrets to unseen attackers? This isn’t a dystopian fantasy but a harsh reality uncovered by groundbreaking research presented at the Black Hat USA cybersecurity conference. Zenity Labs has exposed alarming vulnerabilities in AI agents from
Imagine a world where the most secure data encryption methods, relied upon by governments and corporations alike, are rendered obsolete overnight by the raw power of quantum computing. This looming threat, capable of unraveling asymmetric encryption that underpins global digital security, is no longer a distant concern but a pressing reality that
In an era where digital battlegrounds are as fiercely contested as physical ones, a startling trend has emerged among cybercriminals that redefines the nature of cyber warfare, showing how sophisticated threat actors are not only exploiting vulnerabilities to infiltrate systems but also taking the unprecedented step of patching these flaws after
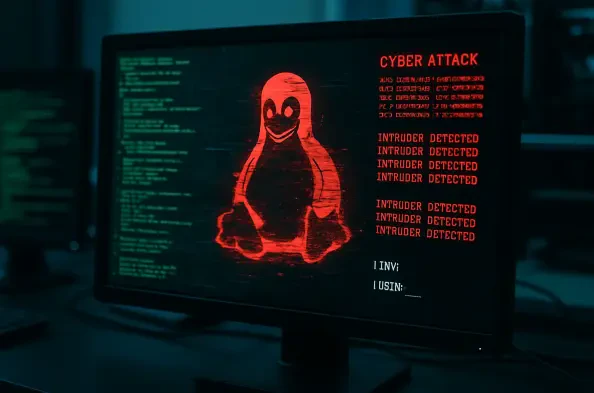
In a chilling reminder of the ever-evolving landscape of cybersecurity threats, a highly coordinated campaign has emerged, targeting cloud-based Linux systems with unprecedented precision through a critical flaw in Apache ActiveMQ. This attack exploits a severe remote code execution vulnerability known as CVE-2023-46604, which carries a staggering