Cloud Security
The relentless pursuit of digital agility has forced modern enterprises to confront a staggering reality where the sheer speed of AI-driven software development is frequently neutralized by the stagnant bureaucracy of legacy network security protocols. In the race to achieve complete digital transformation, many organizations are hitting a
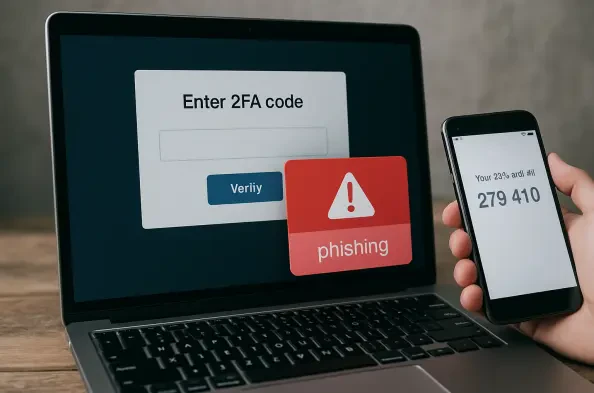
The illusion of absolute security provided by multi-factor authentication has been shattered by the realization that even the most robust digital locks can be picked if the burglar controls the hallway. As organizations increasingly leaned on secondary verification to defend their perimeters, a sophisticated adversary emerged to exploit the very
The rapid metamorphosis of the enterprise digital landscape has fundamentally rewritten the rules of engagement for cybersecurity professionals who must now defend a perimeter that effectively no longer exists in a traditional sense. In this current environment, the definition of an endpoint has expanded far beyond the isolated laptops or mobile
The speed at which a single compromised credential can transform into a full-scale corporate data exfiltration event has forced a radical reimagining of how digital perimeters are policed. For years, security operations centers operated under a fragmented model, where analysts spent more time toggling between disconnected browser tabs than
Modern enterprise environments rely heavily on the integrity of management platforms to orchestrate complex virtual workloads, but a series of recently discovered vulnerabilities has placed these critical systems under intense scrutiny from security teams. Broadcom’s security advisory VMSA-2026-0001, issued on February 24, 2026, highlights a