Emerging Data Security Technologies
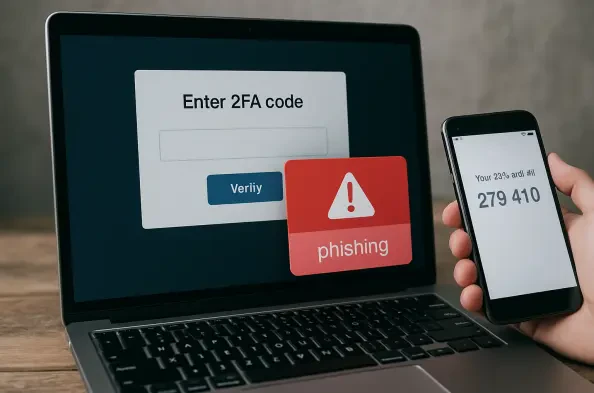
The illusion of absolute security provided by multi-factor authentication has been shattered by the realization that even the most robust digital locks can be picked if the burglar controls the hallway. As organizations increasingly leaned on secondary verification to defend their perimeters, a sophisticated adversary emerged to exploit the very
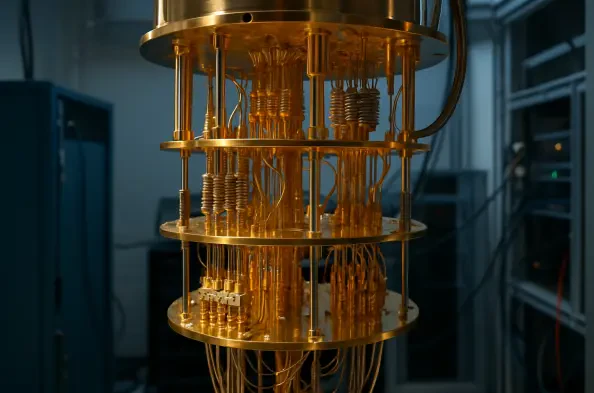
The rapid evolution of quantum computing has fundamentally shifted the cybersecurity landscape, moving the primary concern from classical brute-force attacks to the sophisticated realm of quantum-level decryption. While significant industry resources have been poured into hardening massive data centers and central cloud hubs, a glaring
The transition from classical bit-based logic to the fluid mechanics of quantum processing has moved beyond theoretical physics into a complex era defined by massive infrastructure investments and competing hardware modalities. While popular discourse often simplifies quantum computing into a singular looming breakthrough, the industry currently
The theoretical vulnerability of elliptical curve cryptography to advanced computational threats has evolved from a distant concern into a measurable market variable that dictates current institutional strategies. As quantum hardware continues to advance, the concept of "Q-Day"—the moment when a quantum computer can successfully compromise
The next time your digital assistant suggests adding Hellmann's mayonnaise to your cart, the recommendation might originate not just from your past purchases but from a sprawling new system of intelligence designed by Unilever and Google Cloud. Consumer goods giant Unilever has entered into a landmark five-year strategic partnership with Google