Emerging Data Security Technologies
The rapid integration of artificial intelligence into business operations has created a hidden crisis of ownership that many executive boards are only just beginning to recognize. While companies have rushed to adopt powerful large language models and generative tools to gain a competitive edge, they have largely overlooked the strategic danger of
The sleek monitors of modern engineering hubs are currently flickering with a startling technical contradiction: developers are drafting code 55% faster than they were just a short while ago, yet the actual time it takes to release a single feature has often crawled to a standstill. While large language models have turned the act of writing
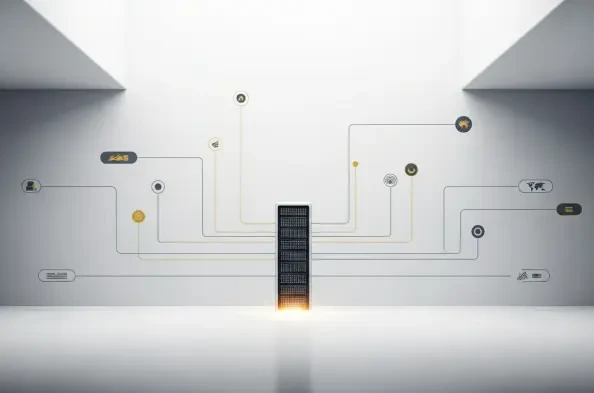
In an environment where the average laptop contains more intellectual property than most physical vaults, the necessity for robust full disk encryption has reached a critical tipping point for both corporate entities and private citizens. By 2026, the traditional notion of perimeter-based security has largely failed, forcing a shift toward a
In an age where digital intercepts occur in milliseconds, the ability to make data physically inaccessible until a specific calendar date represents the ultimate frontier in cybersecurity resilience. The strategic alliance between Gardiyan and QTLE marks a significant step forward in enterprise cybersecurity by integrating advanced Time Lock
A single compromised vendor can now trigger a cascading digital catastrophe across an entire global network, leaving organizations vulnerable to threats they cannot even see. As corporate ecosystems become increasingly reliant on automated tools and interconnected services, the traditional methods of checking security boxes are proving