Emerging Data Security Technologies
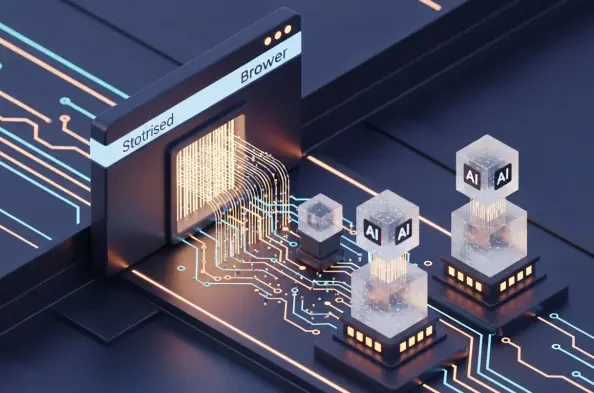
The Dawn of Autonomous Productivity and Its Security Implications The current transition from reactive web interfaces to autonomous digital agents represents one of the most profound reorganizations of corporate software architecture since the initial migration to the cloud. This evolution has birthed a new class of web navigation tools known as
The traditional phone call from a bank’s fraud department asking if a customer really just purchased a luxury watch in another country has become a relic of a less sophisticated digital era. Financial security has undergone a massive transformation that favors invisible, fluid protection over the rigid protocols that previously inconvenienced
The staggering reality for the modern digital enterprise is that while data serves as the foundational fuel for innovation and competitive edge, it has simultaneously transformed into the single most complex and volatile liability within the global security landscape. As organizations navigate the intricate architectures of hybrid clouds,
The rapid evolution of machine intelligence has moved beyond simple chatbots to sophisticated autonomous agents that can manage entire workflows without constant human oversight. As organizations delegate complex tasks to these digital entities, they are effectively granting non-human actors the authority to navigate sensitive internal networks
The modern digital landscape is no longer a place where traditional firewall barriers and simple antivirus signatures can offer even a modicum of guaranteed protection against sophisticated threats. In an era where attackers deploy automated scripts and generative algorithms to probe for vulnerabilities at machine speed, the reliance on