Emerging Data Security Technologies
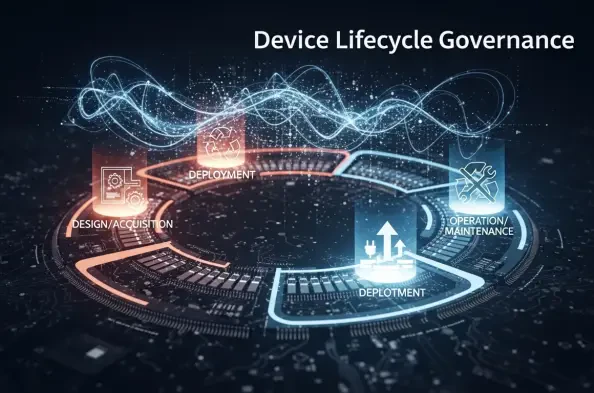
A New Era of Intelligence: Transforming Static Data into Active Reasoning The rapid convergence of sophisticated machine learning models and massive enterprise datasets has finally pushed the corporate world past the limitations of traditional cloud storage and toward a reality where data acts as its own pilot. This strategic initiative marks a
The quiet hum of server farms across the globe represents a seismic shift in power where digital infrastructure now dictates the pace of human ingenuity more than the software itself. While the world watches the latest chatbot updates, a much larger power shift is occurring in the data centers that power them. Amazon’s recent decision to inject
The modern corporation is currently drowning in a sea of unstructured data and fragmented workflows that even the most advanced dashboards have failed to navigate successfully. The Snowflake Agentic Enterprise represents a significant advancement in the data management and artificial intelligence sectors, moving beyond the passive storage of
The promise of autonomous digital workers has captured the corporate imagination, yet many organizations find that seamless productivity remains buried under layers of technical debt and astronomical operational bills. This roundup explores the current landscape of agentic systems, gathering insights from industry leaders and technical architects
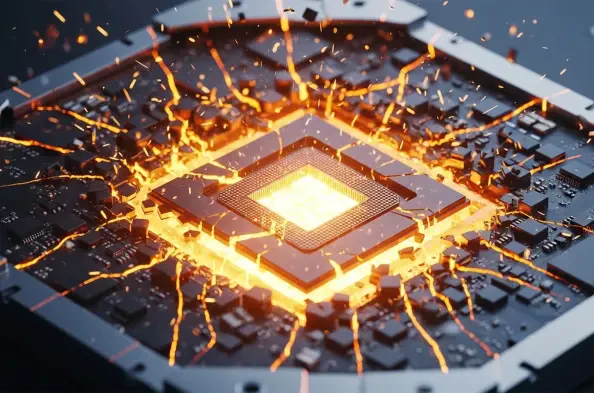
The microscopic architecture of modern graphics processing units now serves as a clandestine gateway for sophisticated attackers to dismantle the security boundaries of an entire operating system. While the tech industry has historically prioritized patching software vulnerabilities, researchers at the University of Toronto have demonstrated that