Endpoint Security
Encountering a sudden system prompt stating that a new app is required to open a windowsdefender link can be an incredibly jarring experience for any Windows user. This specific notification typically surfaces when the operating system fails to execute the windowsdefender: protocol, which acts as the internal highway connecting various interface
A single misrouted prompt, an under-scoped permission, or an unseen agent chain could now pivot an enterprise from efficiency to exposure faster than any legacy breach pathway, and that reality forced the biggest names in technology to compress years of AI security roadmap into a single, decisive month. The clearest signal came from mergers and
When payroll approvals freeze behind a lagging SSO prompt and a video call drops as the VPN renegotiates keys, the business does not pause, it hemorrhages time, trust, and momentum across teams and customers. These aren’t headline-grabbing outages; they’re the routine stalls that creep into daily workflows—crashing collaboration apps, delayed MFA
The landscape of digital infrastructure security is currently undergoing a radical transformation as malicious actors shift their focus from static data exfiltration toward the creation of autonomous, self-propagating entities capable of hijacking the very tools that developers trust most. At the center of this escalation is a sophisticated new
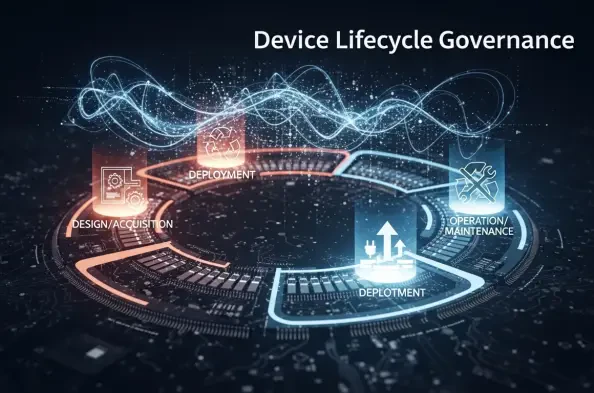
The traditional practice of squeezing every last drop of utility out of an aging laptop has transformed from a frugal business habit into a dangerous operational liability. Organizations that once viewed hardware as a static asset to be owned until failure are now finding that this reactive stance creates massive bottlenecks in productivity and