Lead/Introduction
When the user is no longer a person at a keyboard but a fleet of software agents acting across your stack, every assumption about apps, licenses, and operations gets renegotiated in real time. The tension is palpable: a company that scaled on seats and screens now places its biggest bet on headless agents that plan, coordinate, and execute work without waiting for clicks. For leaders, the stakes rise beyond clever UI—success hinges on orchestrating outcomes across vendors, policies, and data boundaries.
That bet came into sharp focus at TrailblazerDX, where Salesforce framed agents as the front door to business capability and the UI as a secondary, optional touchpoint. It is a decisive step away from the company’s classic mix of CRM depth, low-code tooling, and per-seat pricing. The shift asks a provocative question: if AI is doing more of the work, how should software be designed, governed, and priced?
Nut Graph
This story matters because enterprise software is tilting from systems of record to agentic systems built for outcome execution, not data entry. As large language models mature and API-first ecosystems proliferate, cross-system automation moves from novelty to expectation. In that context, licensing tied to human seats looks misaligned, governance gaps grow visible, and portfolio fragmentation turns costly.
Salesforce’s answer—an agent-first, open architecture—seeks to blend two ideas that rarely coexist: deep domain grounding and model-agnostic interoperability. John Kucera, senior vice president of product management, captured the defense of that position in a single line: “It’s hard to vibe-code our core asset,” a reference to the curated data models and business logic that shape reliable agent behavior. The bet is that openness wins access, while domain depth keeps control.
Body
Salesforce describes a future in which agents are the primary interface and human screens are situational, not central. In practical terms, state, policy, and domain rules become the heart of the stack, and agents orchestrate steps, tasks, and entire processes across multiple systems. Escalation becomes the human’s moment: judgment calls, exception handling, and interventions that correct or teach the agent. That pattern mirrors early wins in support, where Tier 1 resolution rates climbed as agents handled triage, classification, and knowledge lookups before involving a human for edge cases.
The maturation curve tracks a simple progression: first automate steps, then bundle them into tasks, then string tasks into processes, and eventually coordinate capabilities that span departments. In sales, this already shows up as agents qualifying leads, drafting outreach with governed content, logging activities, and assembling forecasts from signal-rich histories. As those agents consume more of the routine, humans move “up the stack” to coach escalations, shape strategy, and refine playbooks.
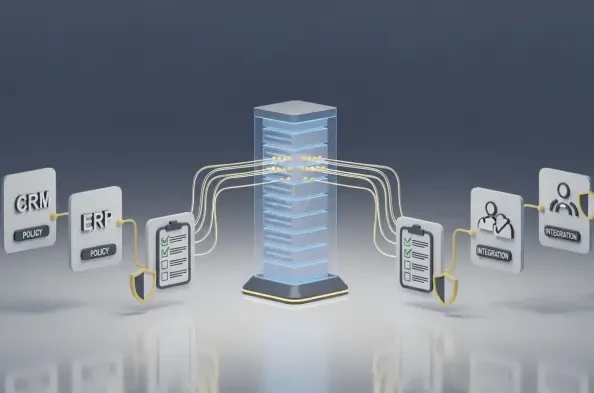
The pivot hinges on openness, which starts at the API layer and extends through MuleSoft, model choice, and interoperability standards. Salesforce argues that enterprise buyers now treat openness as table stakes: agents must read and act across heterogeneous stacks while honoring policy and governance. Kucera’s framing is blunt: general LLMs can generate code, but enterprise agents must be grounded in explicit schemas, process logic, and controls. The company’s claim: a stack that embeds domain depth with guardrails is “hard to beat.”
That defense sits alongside a candid pricing question. If agents perform work units once linked to users, per-seat licensing mismeasures value. Salesforce signaled a transition toward hybrid or consumption-aware models tied to agent activity and outcomes. Revenue timing could feel pressure as customers experiment, but the company suggested the shift would be less turbulent than the industry’s earlier move from perpetual licenses to subscriptions. For CIOs, the operational advice was pragmatic: keep existing subscriptions steady while piloting agent-first flows and negotiating flexible terms.
The organizational implications extend beyond finance. A new role emerged: the agent manager. This leader defines guardrails, tests prompts and policies, monitors telemetry, and directs escalations. In practice, the agent manager curates input sources, approves action scopes, and reviews audit trails for safety and compliance. That function becomes the connective tissue among security, legal, data, and business teams, turning agent behavior into an operational discipline rather than a one-off experiment.
Observability underpins trust. Enterprises demanded fine-grained logs of what the agent saw, why it chose a path, what it changed, and how outcomes compared to policy. Early pilots that paired strong observability with bounded scopes saw faster approvals from risk teams and more sustained ROI. One global retailer, for instance, fenced an agent to handle catalog fixes and low-risk service tickets; the program reduced backlog by double digits while surfacing data hygiene gaps that would have undermined a broader rollout.
As agents grow more capable, process boundaries blur. Salesforce pushed beyond CRM modules to end-to-end flows like order-to-cash that often cross SAP or Oracle domains. The technical posture favored integration fabric and lightweight protocols—such as an MCP-style server—to coordinate intent, context, and actions across stacks. The strategic read is clear: in an agentic world, business capability eclipses application silos, and the orchestration layer becomes the center of gravity.
This expansion invites competition, not only with ERP incumbents but also with hyperscalers, model providers, and automation platforms. Salesforce framed its stance toward foundation model vendors as multi-dimensional: partner, customer, supplier, and occasionally competitor. The differentiation, it argued, would not sit in owning a single model but in policy, observability, security, and integration depth. As specialized models proliferate, customers value the ability to swap, blend, and route while keeping governance stable.
The risk of disintermediation looms over any open ecosystem: if agents can reach any system, they could bypass a platform altogether. Salesforce countered that meaningful traction with Agentforce suggested a different dynamic, in which openness expands reach while domain depth anchors trust. “Position the agent stack where enterprise controls live,” one product leader explained, “and the rest of the system naturally aligns to it.” In other words, be the safest place to run consequential work and neutrality becomes an asset, not a liability.
Data validated the direction. Studies from multiple consultancies reported that high-performing automation programs shared three traits: clean master data, robust APIs, and clear escalation design. Organizations that launched with bounded pilots in support and sales saw time-to-resolution drop by 15–30% and customer satisfaction tick up, provided governance and telemetry were in place from day one. Those patterns informed a simple playbook: start small, instrument deeply, and scale by capability rather than by application.
For CIOs, the portfolio question shifted from “which app?” to “which capability and where should the agent sit?” Mapping lead-to-revenue or order-to-cash across applications quickly revealed redundant workflows and brittle integrations. Reframing investment around capability allowed teams to insert agents at points of latency—handoffs, reconciliations, and repetitive data transformations—without breaking critical compliance flows. Over several quarters, that lens helped leaders re-allocate spend from UI customization to integration quality and policy enforcement.
Procurement strategy evolved in parallel. Scenario planning incorporated consumption-based and outcome-aware pricing alongside seats. Contracts began to feature ramp options for agent usage, with guardrails on burst capacity and clear rollback clauses. Finance teams adjusted cost-allocation models to tie spend to work units rather than headcount, a shift that made productivity gains more visible and encouraged tighter collaboration between technology and operations.
Under the hood, the agent stack coalesced around repeatable patterns. Retrieval and grounding drew from curated knowledge and governed datasets, not ad hoc sources. Policy layers enforced “who can do what” before action execution. Observability collected step-level telemetry and natural-language rationales for audits. And, crucially, human-in-the-loop checkpoints handled ambiguous decisions with documented outcomes that retrained the agent’s behavior. The result resembled a control system more than a chatbot, with feedback loops and safety interlocks designed for regulated environments.
Kucera’s line—“It’s hard to vibe-code our core asset”—echoed throughout these choices. The message: code generation is easy; enterprise-grade judgment is not. Reliable agents require the scaffolding of domain models, lineage-aware data, and explicit process rules. That scaffolding is portable across models, which is why interoperability and neutrality matter. As one CIO put it after a successful service pilot, “Model choice was a procurement question. Grounding and governance were the operational answers.”
Even so, uncertainty persisted. Pricing would adjust, roles would shift, and boundaries with ERP providers would be tested. Salesforce’s posture was to move early and help customers adopt safely at scale, not to declare the debate settled. The company’s willingness to disrupt its seat-based heritage signaled confidence that orchestration, not interface real estate, would define the next decade of enterprise value.
Conclusion
The next moves belonged to operators, not only vendors. Teams that mapped capabilities end to end, cleaned master data, and strengthened APIs had already created fertile ground for agents to absorb routine work while humans focused on exceptions and design. Leaders who formalized agent manager roles, instrumented telemetry, and negotiated flexible pricing had set themselves up to convert pilots into durable programs. Procurement groups that prepared hybrid models—seats for people, consumption for agents—reduced friction when usage spiked.
The practical steps coalesced into a clear sequence: run UI and agent paths in parallel, define escalation ladders with decision rights, and use bounded domains like support triage or sales follow-ups to measure safety, speed, and ROI. From there, scale by capability—lead-to-revenue, then order-to-cash—rather than by application module, and insist on model-agnostic patterns to preserve choice. By the time vendors refined licensing and controls, organizations that treated agents as managed workers, not novelty interfaces, had built a repeatable path to value and shaped how this market would be won.